Documentation
User Guide for Domain Administrators
ExchangeDefender admin portal service documentation for domain administrators. This role has secure access to all policies, logs, configurations, service subscriptions, and user management.
User Guide for Domain Administrators
Summary
ExchangeDefender Admin Portal gives organization (domain) administrators central access to all policies, logs, configurations, service subscriptions, branding, and user management. From this secure site, accessible via desktop and mobile, you can manage email security for your entire organization and customize it to fit your specific needs. The login credentials or password reset link will be sent to you by your IT department and you can access all services here:
ExchangeDefender Admin Portal
Navigating around ExchangeDefender's User Interface (UI) is simple, with a tool bar across the top for most common tasks, and management sections (links) on the left.
The rest of the UI contains the main functionality for whichever section you're currently managing. Almost all pages will also have a tabbed interface for additional settings, ability to export the current view into a csv/pdf, and search/paging functions. When you are in sections that require your full attention and you want them to take up most of the screen (for going through SPAM messages, auditing access logs, etc) you can also click on the << icon next to shrink all the navigation and menu displays and focus on the content of the section you are working on.
Almost all pages will also have a tabbed interface for additional settings, ability to export the current view into a csv/pdf, and search/paging functions.
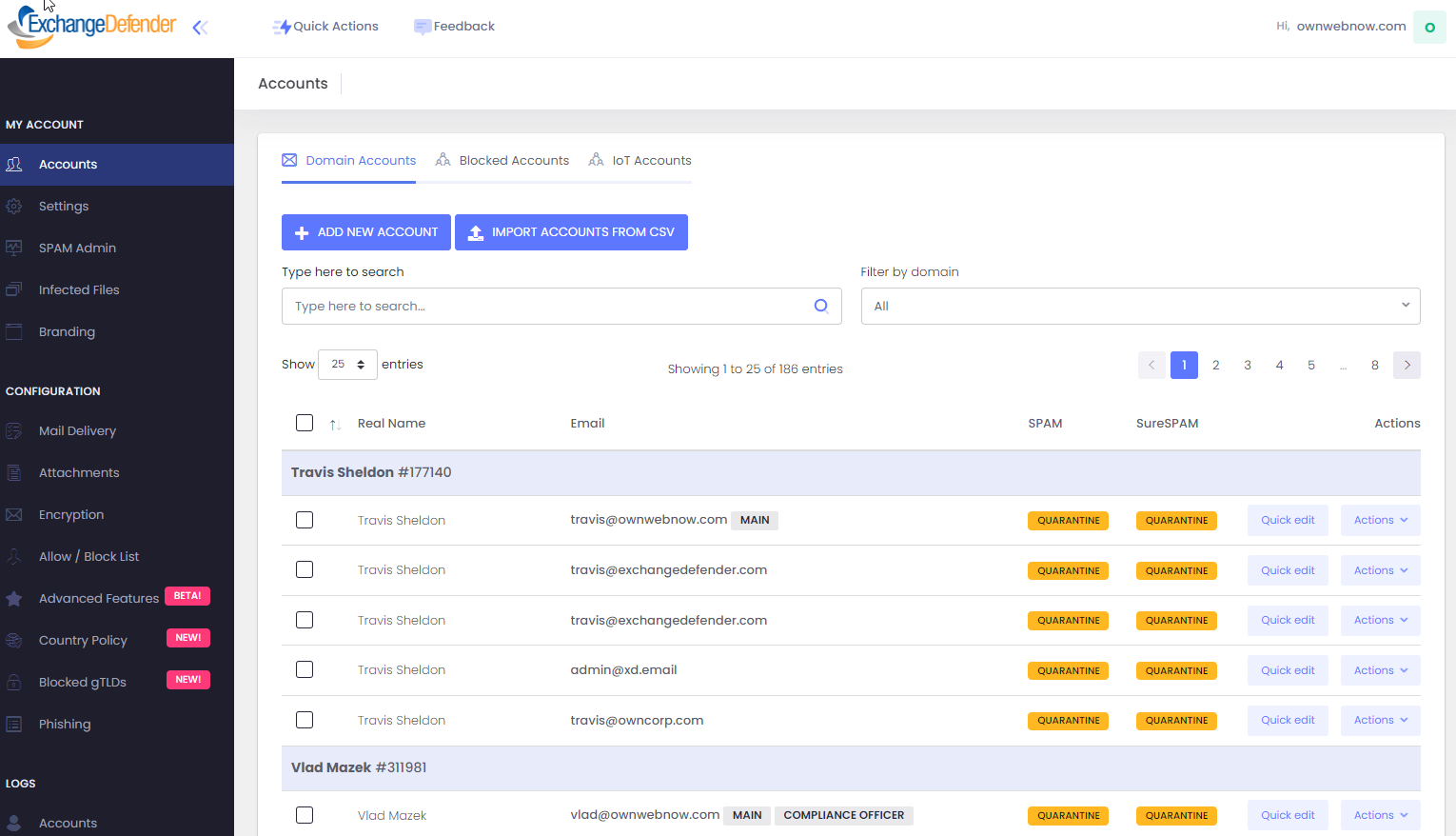
Domains - Accounts
ExchangeDefender organization administrators manage all user accounts from a single interface available from the Accounts tab. Across the top you will see tabs for Domain Accounts, Blocked Accounts, and IoT Accounts .
Domain Accounts - All the accounts and email aliases associated with the members of your organization, as well as all the aliases (for additional email addresses the user manages, for vanity purposes, and for public folders / shared mailboxes, etc)
Blocked Accounts - Accounts and email addresses that are not meant to be protected by ExchangeDefender.
IoT Accounts - Machine / system accounts for Internet of Things devices to send alerts or notifications (printers, copiers, thermostats, sensors, etc).
Managing Accounts
To protect another user, click on +Add New Account. All users are listed below and the form supports multi-select, enabling administrators to apply the same action to multiple accounts (i.e. mass password reset)
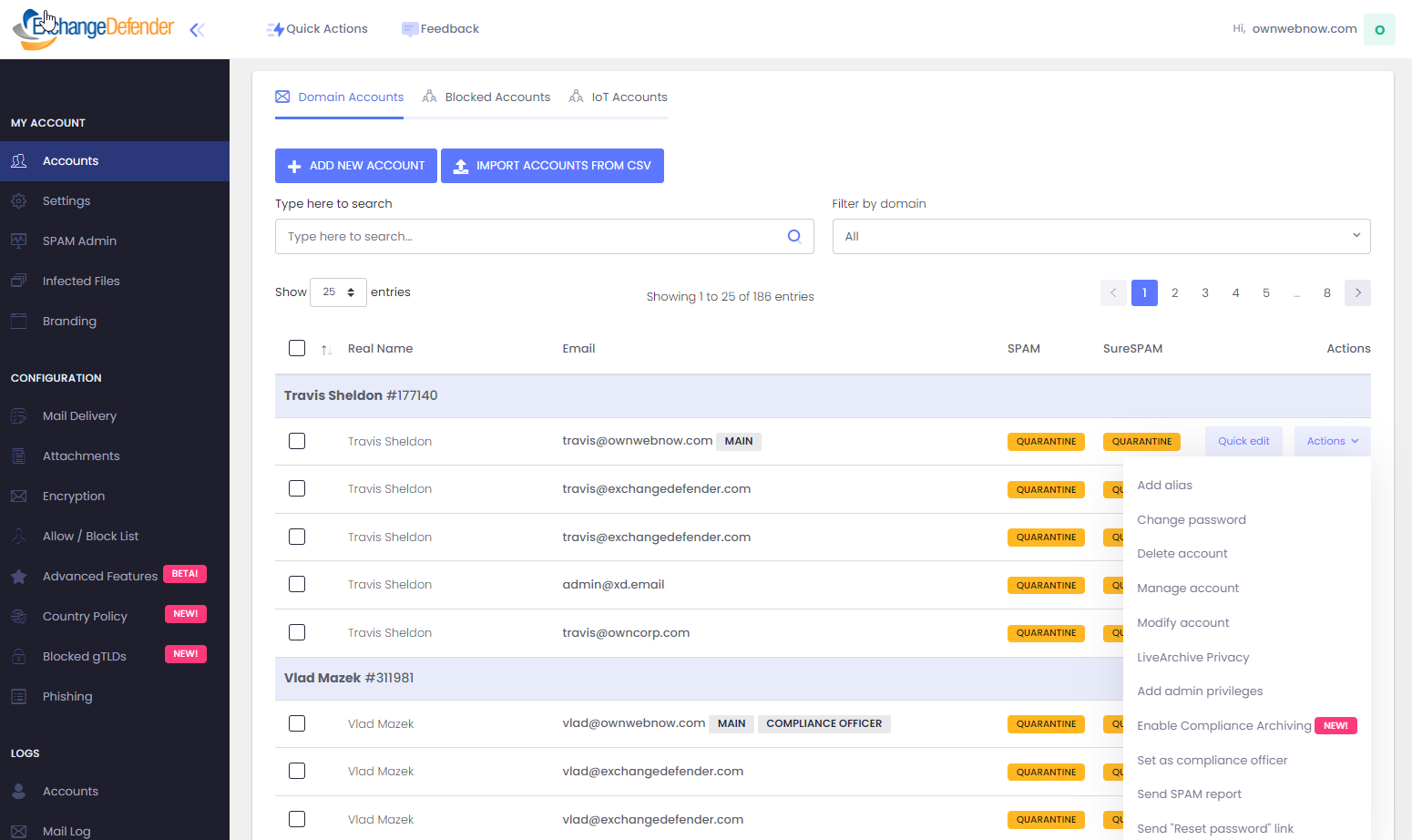
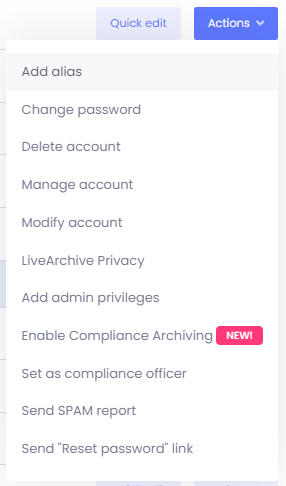
All email accounts within your organization are listed here. You can search for individual addresses or filter your view by domain (by default all are displayed). The main email address is at the top of each account (MAIN) and you can use Quick edit to quickly modify SPAM and SureSPAM policies. Additional options are available under the Actions menu:
- Add Alias- Protect an additional email address and associate it with the selected account.
- Change Password - Change Password allows you change the user's password and select a new password. This is different from Reset Password.
- Delete Account - Deleting an account will remove the email address from ExchangeDefender as well as all their policies and data.
- Manage Account- Manage Account is a superuser shortcut, clicking on this action will log you in and allow you to impersonate the user (and see what they see, for support purposes)
- Modify Account - Modify account enables you to change account configuration and policies.
- LiveArchive Privacy - LiveArchive is an always-on realtime business continuity solution that contains up to a year of your sent and received messages. If you would like to keep other users out of specific LiveArchive mailboxes you can setup a different password. This would prevent administrators from being able to access your LiveArchive or change your LiveArchive password without permission.
- Set as Compliance Officer - If your organization subscribes to ExchangeDefender Compliance Archiving, setting a user as a Compliance Officer will give them additional administrative functionality.
- Enable Compliance Archiving - This feature can be enabled/disabled on a per-user basis. Contact https://support.exchangedefender.com if this is the first archiving mailbox in the domain and confirm archiving is working.
- Send SPAM Report - ExchangeDefender Pro subscribers can setup Daily SPAM Quarantine Reports that email them the list of messages we quarantined as SPAM, this option allows you to send them the report again (the new report will be generated)
- Send "Reset Password" link - This option will send the user a reset link. Unlike Change Password, you will not be asked to pick a new password, the password will be changed to a random secure password, and the user will get a reset link to pick a new password. This is helpful if the account has been compromised or you just want to force the user to change their password for security reasons.
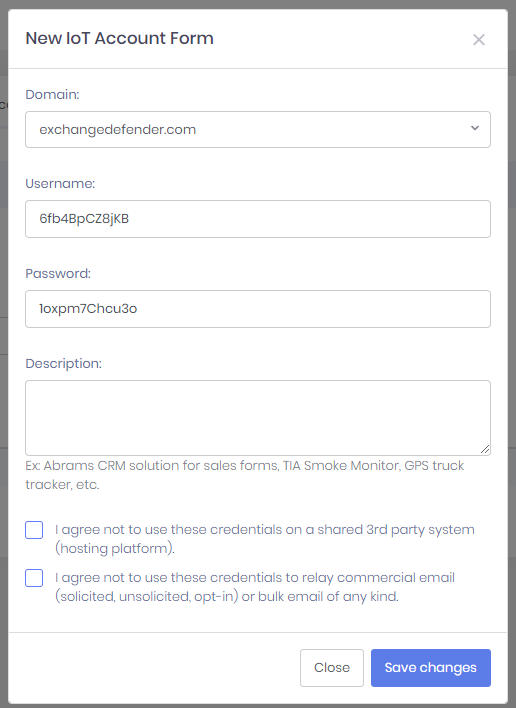
Domains - Accounts - IoT Accounts
ExchangeDefender enables organizations to connect their IoT (Internet of Things) devices to the Internet and enable email functionality.
These devices range from printers, copiers, alarms, sensors, and even third-party services that generate alerts and require a local SMTP server. Since most organizations no longer have SMTP servers, ExchangeDefender provides a free SMTP gateway. In order to add a new IoT account click on +ADD NEW IOT ACCOUNT.
ExchangeDefender strongly encourages domain / organization administrators to create an IoT account for every device or service on the network.
If one of the devices or services gets compromised (common IoT issue) they will have free access to relay mail and ExchangeDefender aggressively shuts down abuse. Because IoT devices tend to have complex configuration processes, changing the password on multiple devices should be avoided at all cost by setting up an account for each device. For this reason alone, ExchangeDefender IoT accounts are free of charge.
- Username & Password - ExchangeDefender randomly generates the username and password for each device.
- Description - Device or service description.
- Disclaimers - ExchangeDefender requires strict compliance to assure security of our platform, asking you not to use the accounts for commercial/SPAM purposes or put the credentials on shared systems (WordPress blogs/forms)
ExchangeDefender IoT devices are required to relay through the following server: outbound-auth.exchangedefender.com which is load balanced across multiple data centers for redundancy. If your ISP allows you to use port 25 (even most business connection ISPs require special permission) you can use port 25 with TLS/SSL. If you cannot use port 25, please try port 2525.
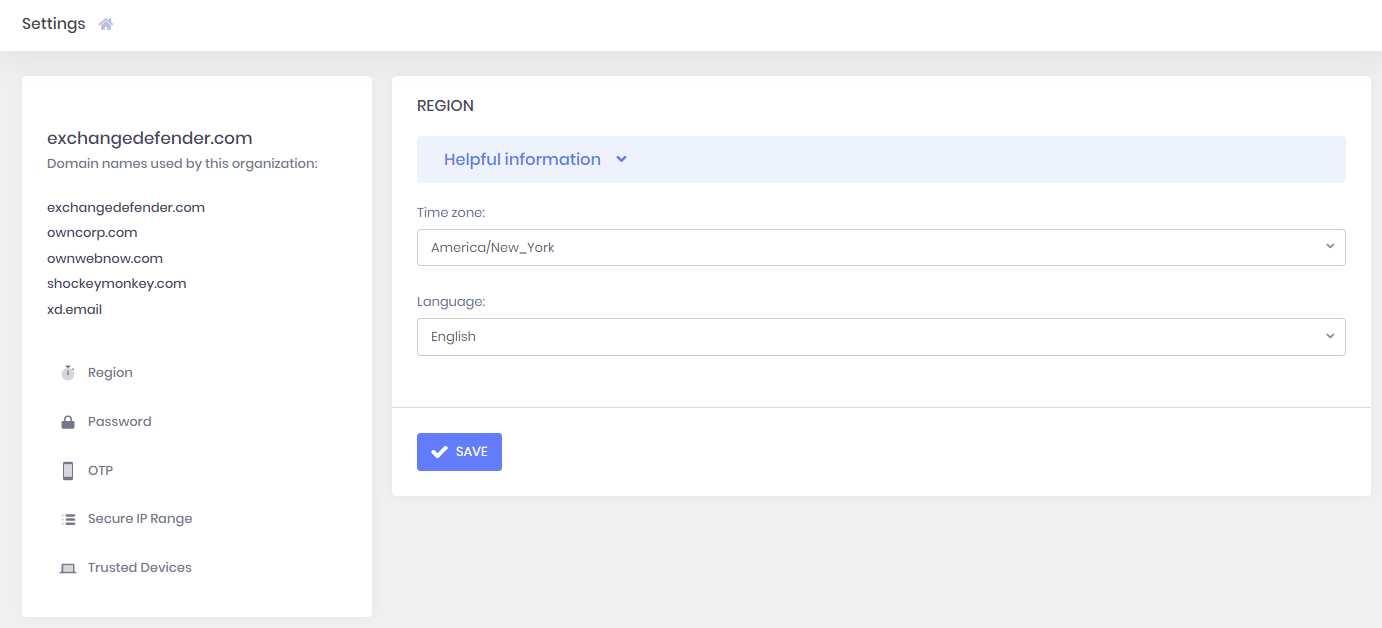
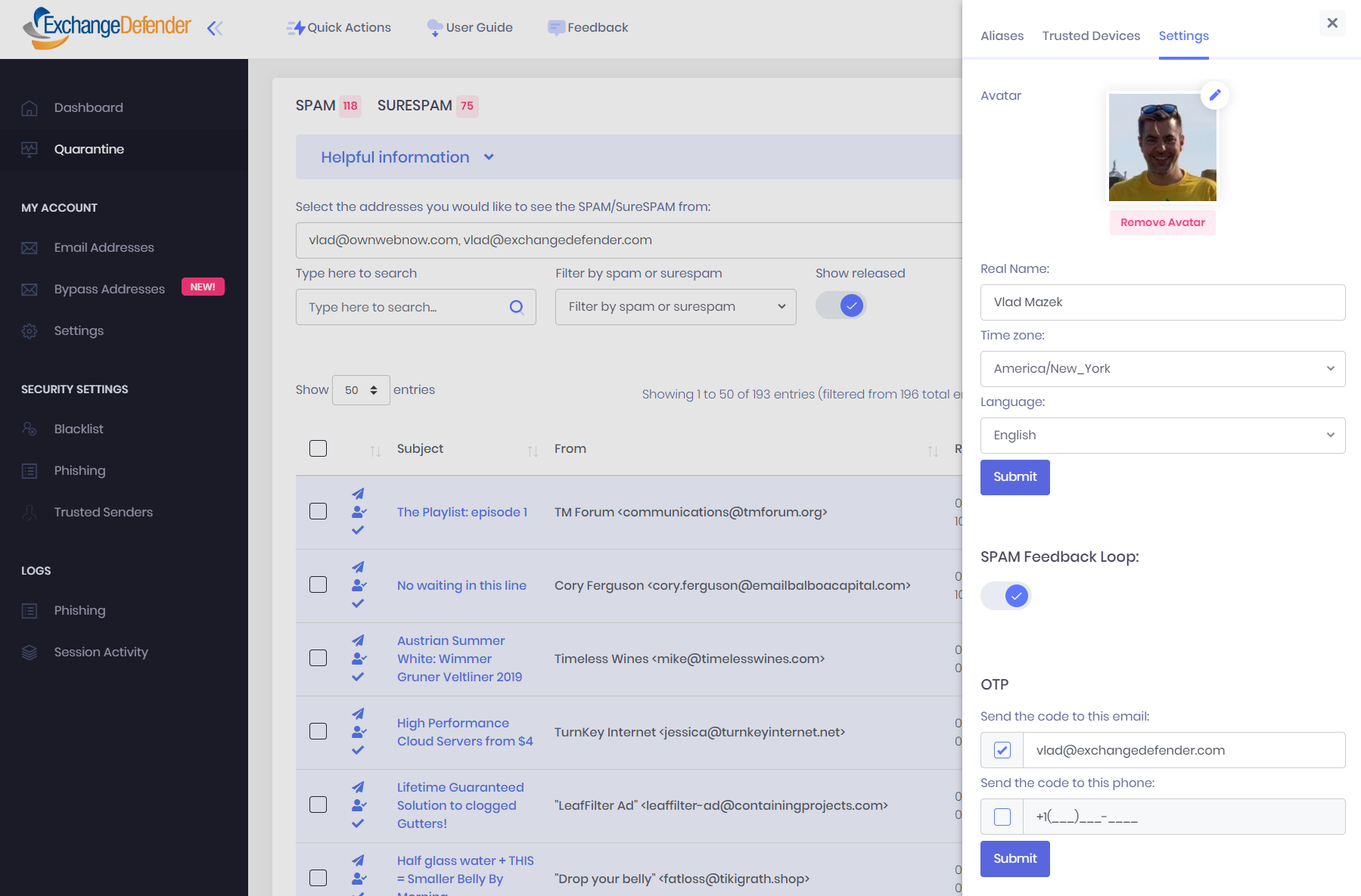
Domains - Settings
ExchangeDefender Settings for Domain Administrators is used to manage security and account settings for the Domain Administrator (ie: exchangedefender.com) account only. Region enables you to configure your language and time zone (which is used as a basis to show timestamps everywhere in the portal as well as determine when to send SPAM Quarantine reports)
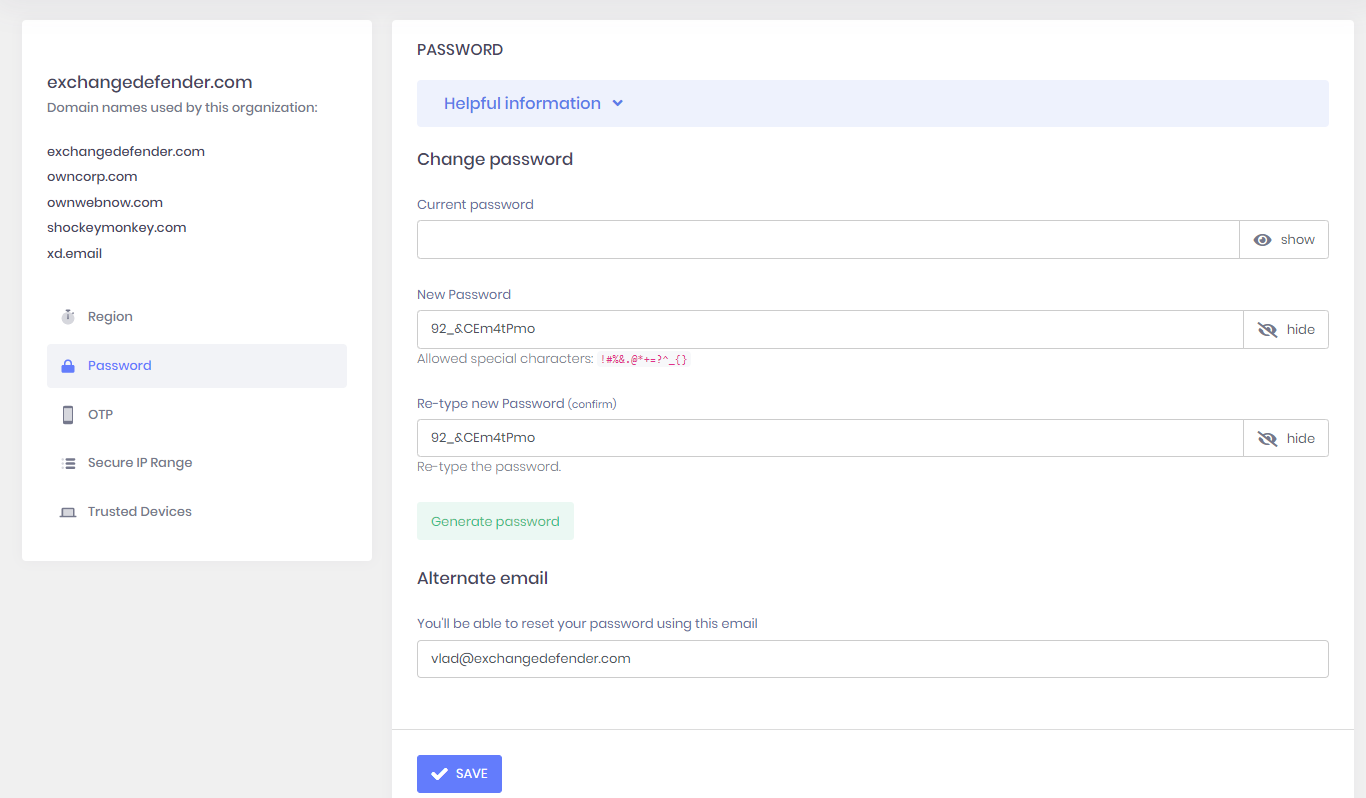
Domain Administrator password should be changed every 90 days and complexity requirements are in place. ExchangeDefender also recommends providing an alternate email address in the event that you forget your password and need to gain access.
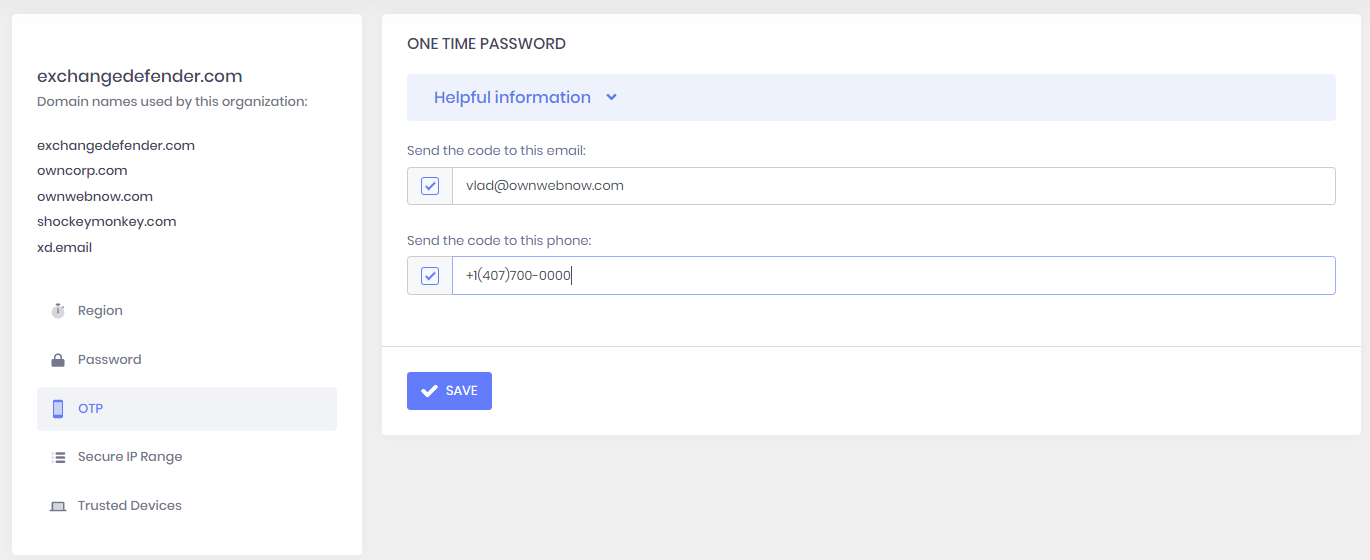
One Time Password (OTP) and two factor authentication (2FA) can be managed from this screen and we strongly recommend using a mobile phone as an additional authentication device.
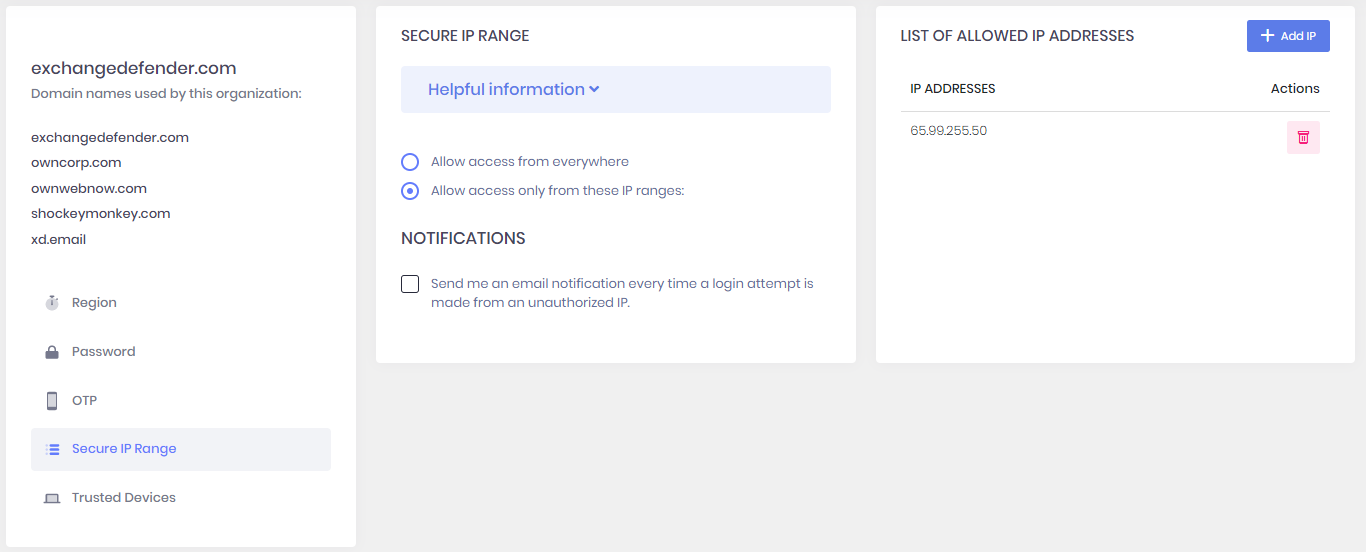
Secure IP Range feature enables organizations with advanced security policies to restrict access to ExchangeDefender to specific IP ranges. Furthermore, you can request an email notification whenever a login is attempted from an IP address outside of your authorized range.
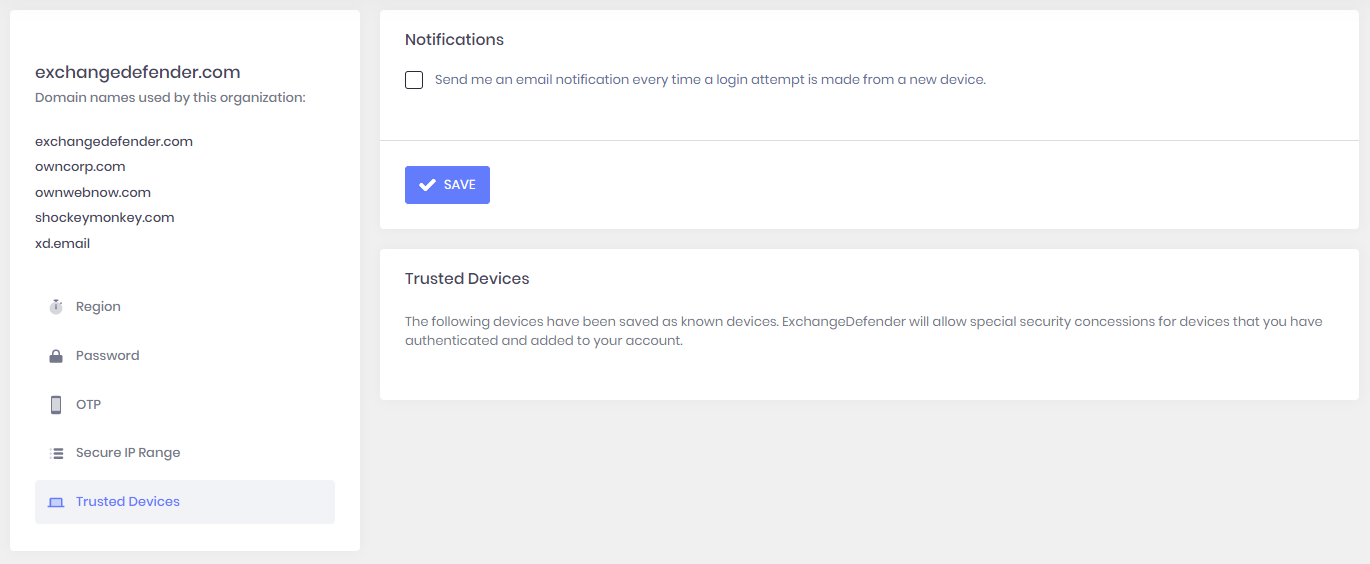
Trusted Devices enables ExchangeDefender to remember and trust known devices. You can request an email notification whenever a new device accesses the Domain Administrator section of the portal.
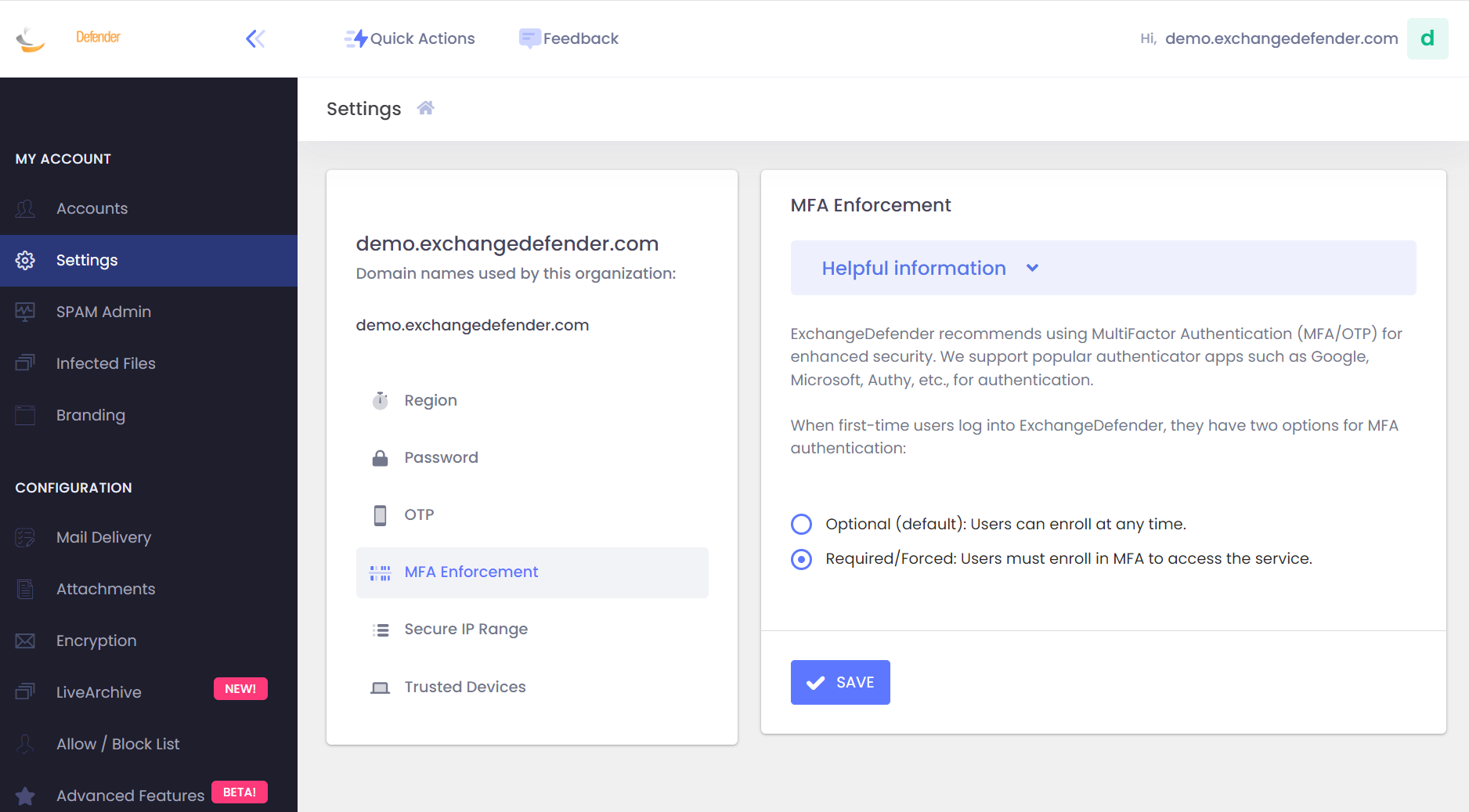
Enforcing MFA Enrollment at Domain Level: Updated Procedure
Effective March 2024, ExchangeDefender introduces a new feature empowering administrators to enforce MFA enrollment at the domain level. This enhancement streamlines the process, allowing you to require MFA enrollment with just one click at https://admin.exchangedefender.com.
ExchangeDefender has introduced an MFA Enforcement Policy, offering a convenient yet secure method to enforce MFA enrollment at the domain level. Implementing MFA Enforcement adds an extra layer of security without the hassle of device-specific enrollments.
How It Works:
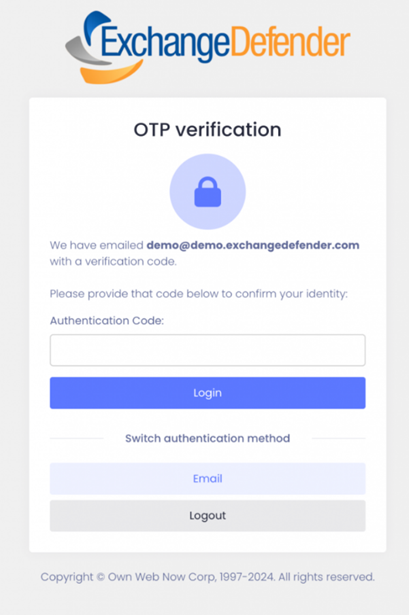
Verification Prompt: Users attempting to access Inbox, WFS, or LiveArchive on admin.exchangedefender.com will be prompted to verify their identity.
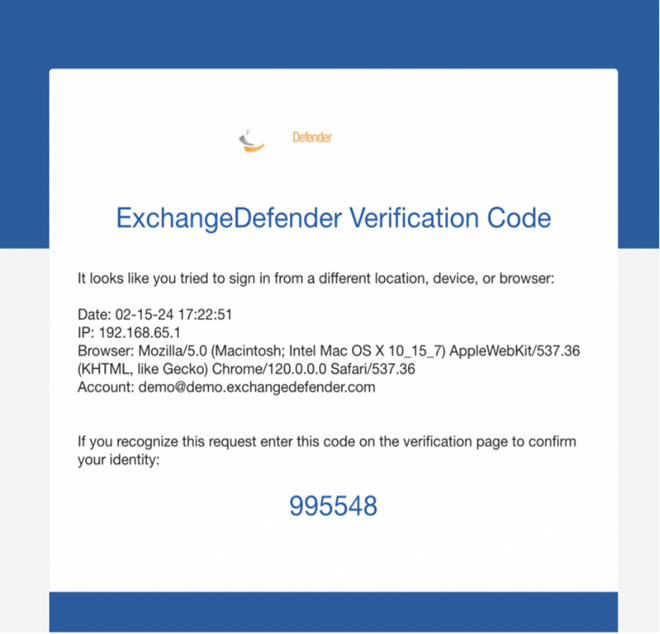
Email Verification: Users receive an email from ExchangeDefender containing a verification code.
Secure Login: Users enter the provided code, securing their ExchangeDefender login with MFA, even without enrolling a device.
Setting up MFA Enforcement:
- Access your ExchangeDefender settings inside your Admin dashboard at admin.exchangedefender.com
- Navigate to MFA Enforcement preferences.
- Choose "Required" or "Forced" mode.
- Upon the first visit to admin.exchangedefender.com, users enter their credentials.
- Email MFA Verification: Users receive an email with a verification code.
Seamless Enrollment: After email verification, users' authenticator apps are enrolled by scanning the QR code.
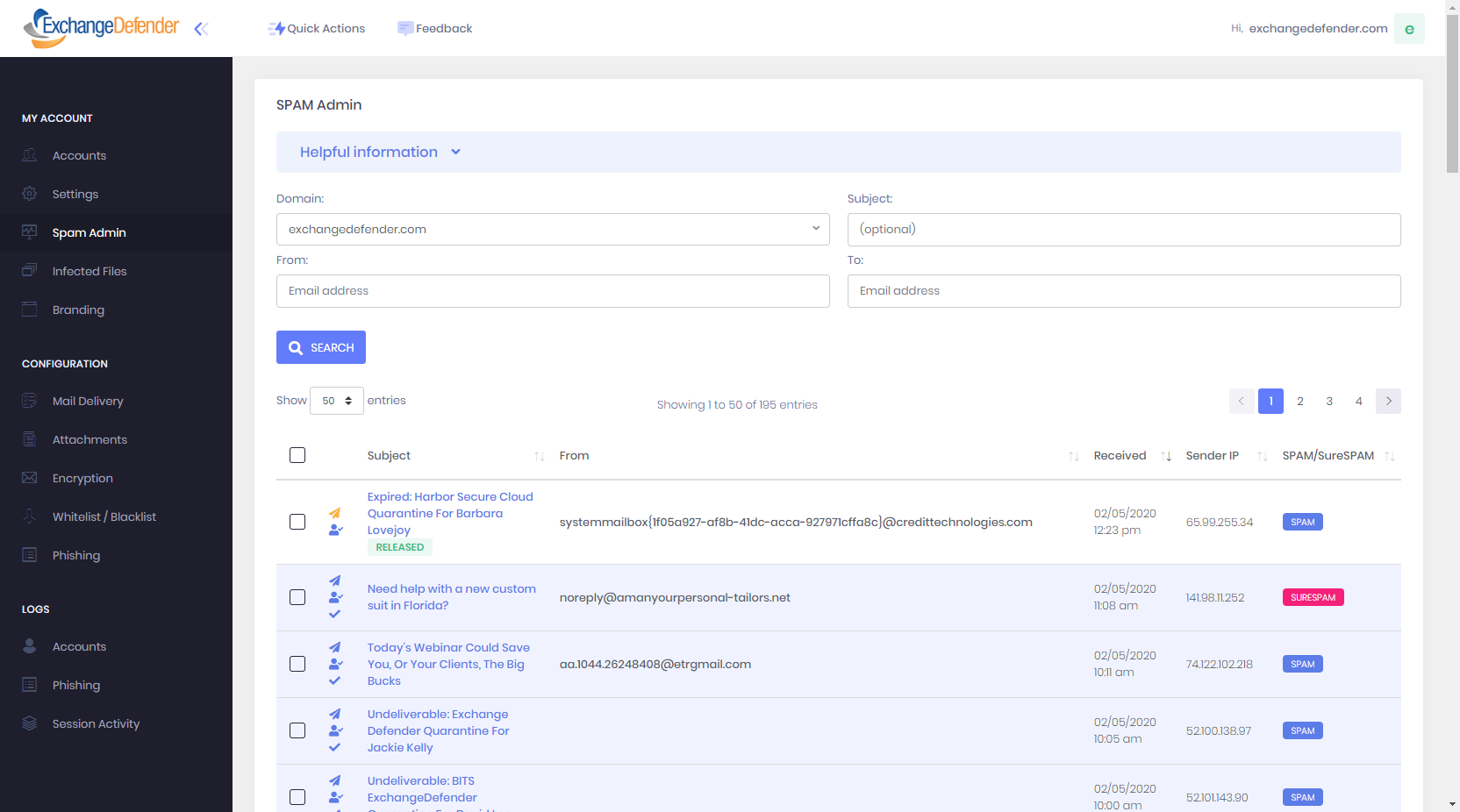
Domains - SPAM Admin
ExchangeDefender SPAM Admin section is intended for email administrators that are in charge of managing and releasing SPAM messages on behalf of the other users in an organization. Some smaller organizations (typically law, medical, construction) designate a person on staff that is responsible for releasing SPAM messages and infected files on behalf of other employees.
ExchangeDefender uses the same controls and management for SPAM Admin that every user is already familiar with from the user SPAM quarantine management. SPAM Admin can search, restrict the SPAM listing by domain, sender, recipient, and subject to make it easy to find specific messages you are expecting.
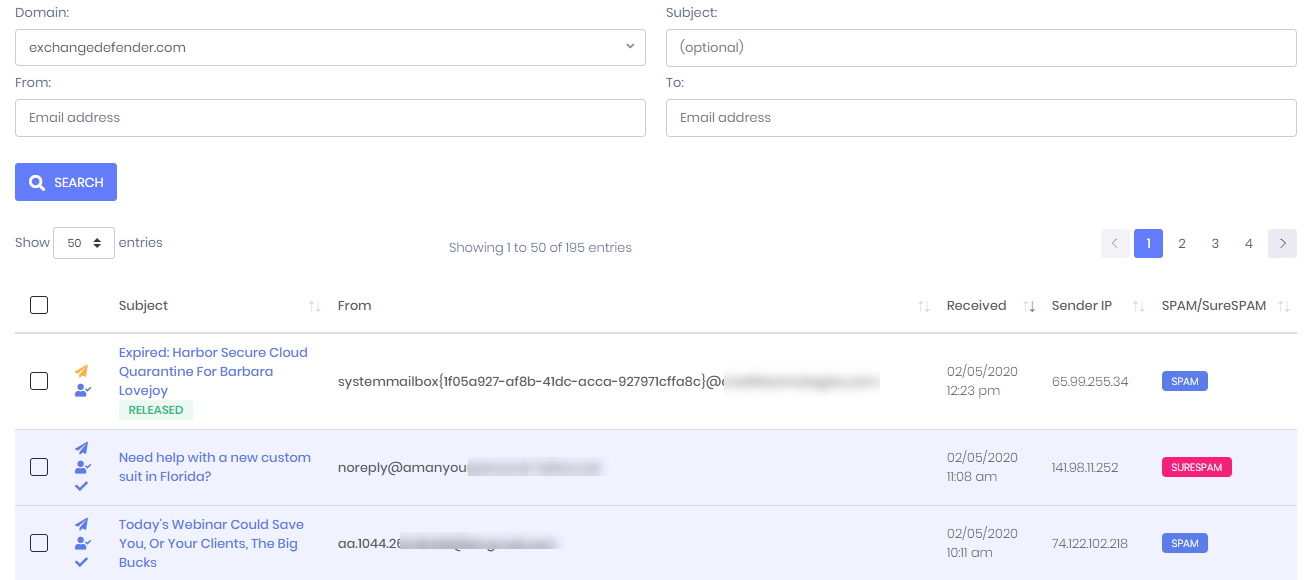
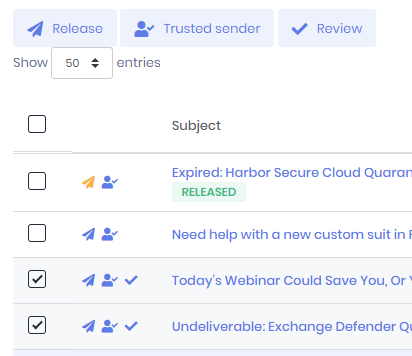
ExchangeDefender Quarantine Search is essentially the ExchangeDefender SPAM Quarantine Report for the entire organization. Domain administrators may use this form to locate any piece of junk mail quarantined for the entire organization and quickly act on it. Just select any message (or multiple messages) and additional buttons will enable you to:
- Release - Selected messages will be released from the ExchangeDefender SPAM quarantine and delivered to the recipients Inbox.
- Trust Sender - Selected messages will be released from the ExchangeDefender SPAM quarantine, delivered to the recipients Inbox, and the senders email address will be added to the user's allowlist.
- Review - Review option simply flags the message as reviewed so it does not show up in future searches. This option is convenient and designed for staff that is checking the list often and only wants to see messages that were quarantined since the last review.
To quickly Release, allowlist, or review a message you can click on one of the shortcut icons next to the Subject. Clicking on the subject will load the message and give you options to Release, Print, and allowlist (add to Trusted Senders).
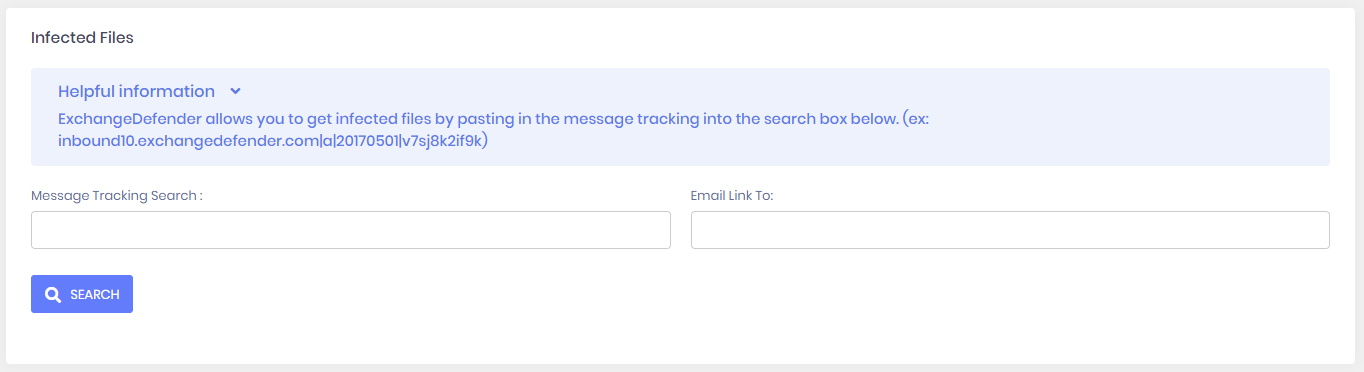
SPAM Admin - Infected Files
ExchangeDefender enables domain / organization administrators to access infected file quarantines on behalf of users. If one of ExchangeDefender's many antivirus engines detects a threat, it is quarantined or saved on our network and the user is sent a notice that one of the dangerous attachments has been removed with a tracking id. Administrators can use the search to locate the message and get the download link.
Email link to option gives domain administrators to send the attachment download link via email to the user or to another party that can review it. The email simply contains the message information and the link to download the attachment.
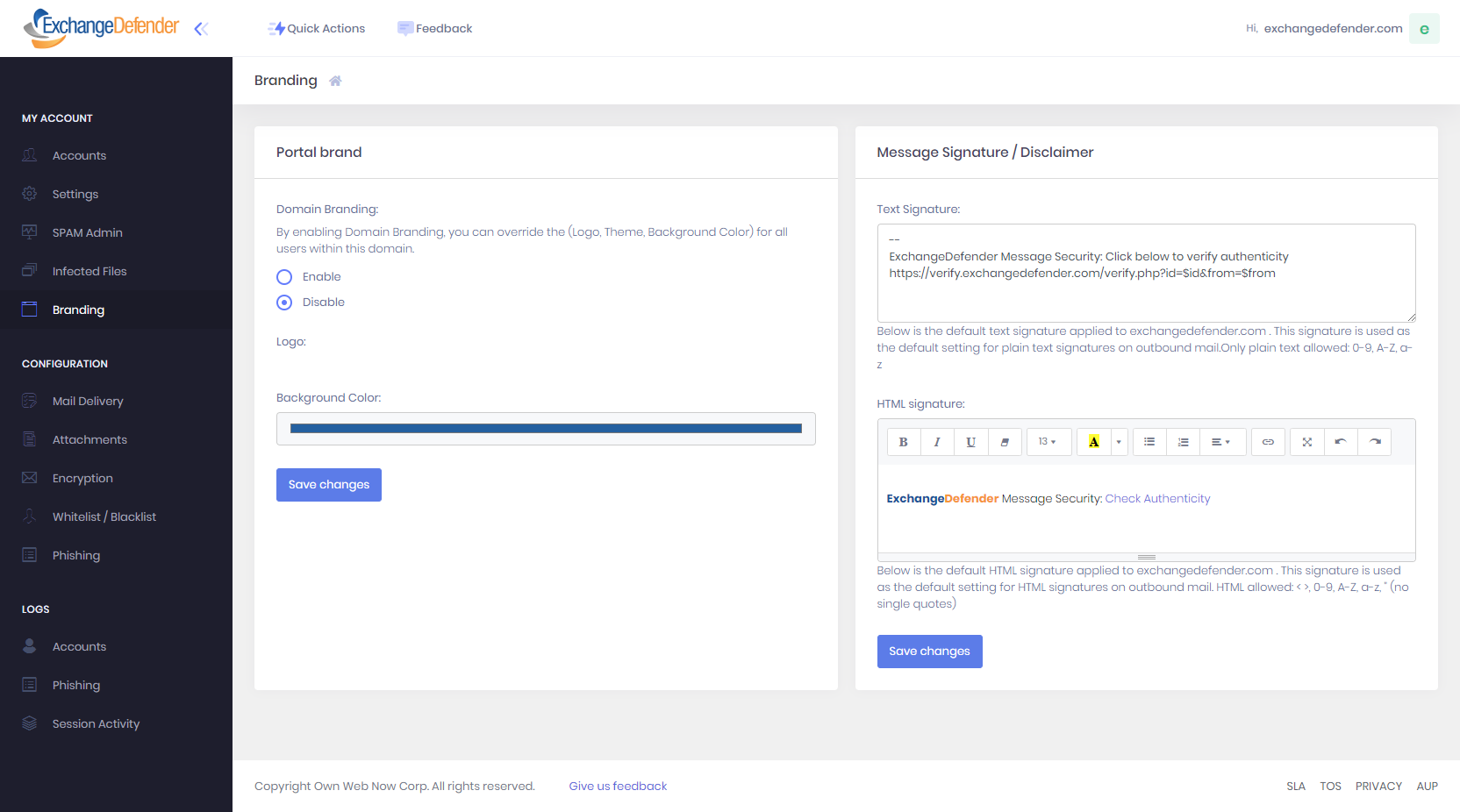
Domains - Branding
ExchangeDefender enables organizations to extend their branding to the ExchangeDefender portal, and to standardize their corporate email signature or disclaimer on all outbound messages. This is a global setting for all domains in the organization and every message coming from the domain will be signed with the text and HTML markup provided here.
By enabling Domain Branding you can upload the logo that will be displayed on the Domain Admin and User sections of the portal (instead of ExchangeDefender, MSP, or reseller branding). Main background & accent color can also be personalized.
Domains - Configuration
ExchangeDefender Domain Admin portal offers rich customization and security enforcement policies. Everything regarding how ExchangeDefender works for your organization is here.
Mail Delivery section enables you to set mail flow policies:
- Mail Servers - Policies for email delivery, authorized relays, and LiveArchive.
- Postmaster - Organization postmaster, notified in case of abuse or other security sensitive events.
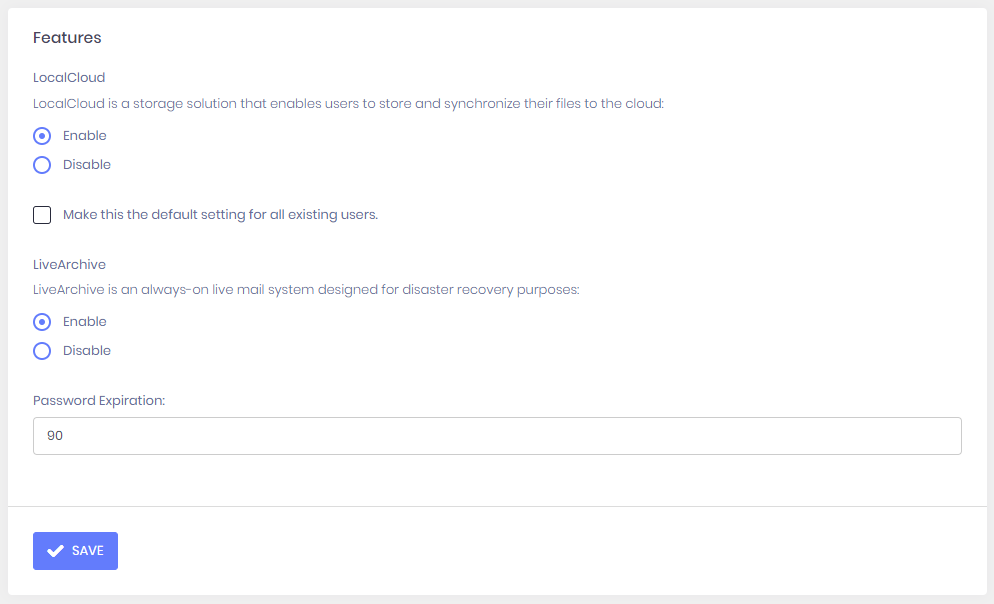
- Features - Enable and disable misc ExchangeDefender functions.
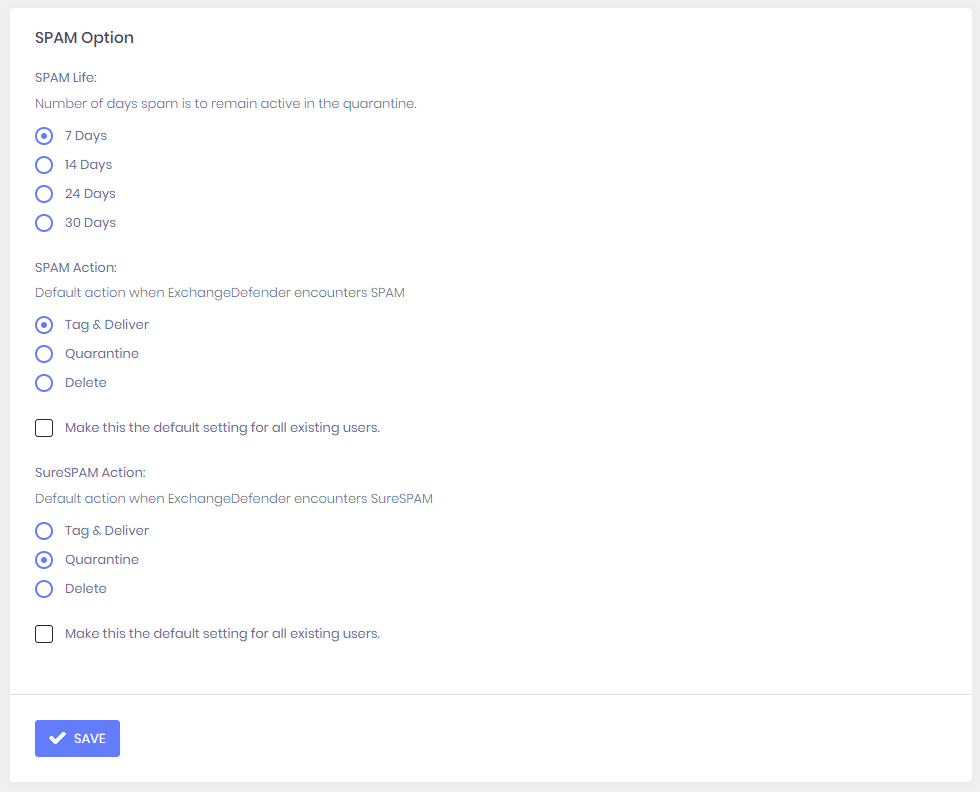
- SPAM Options - Configure SPAM handling.
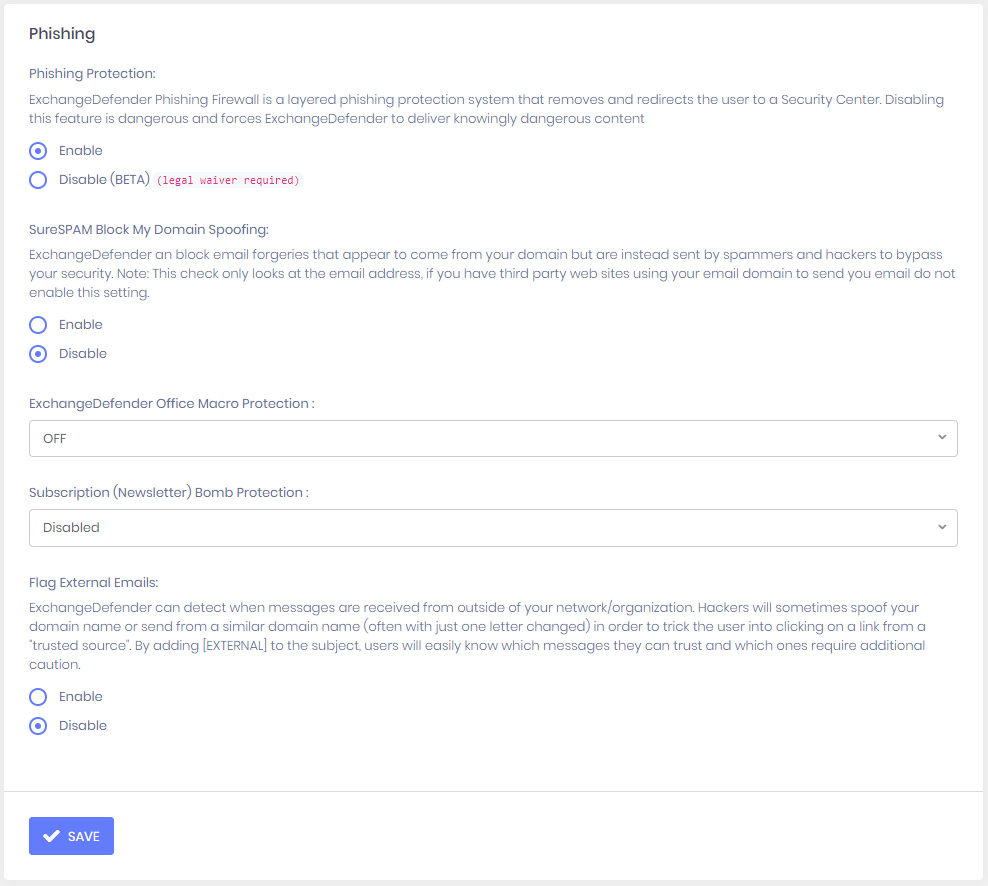
- Phishing Options - Configure Phishing protection and alerting.
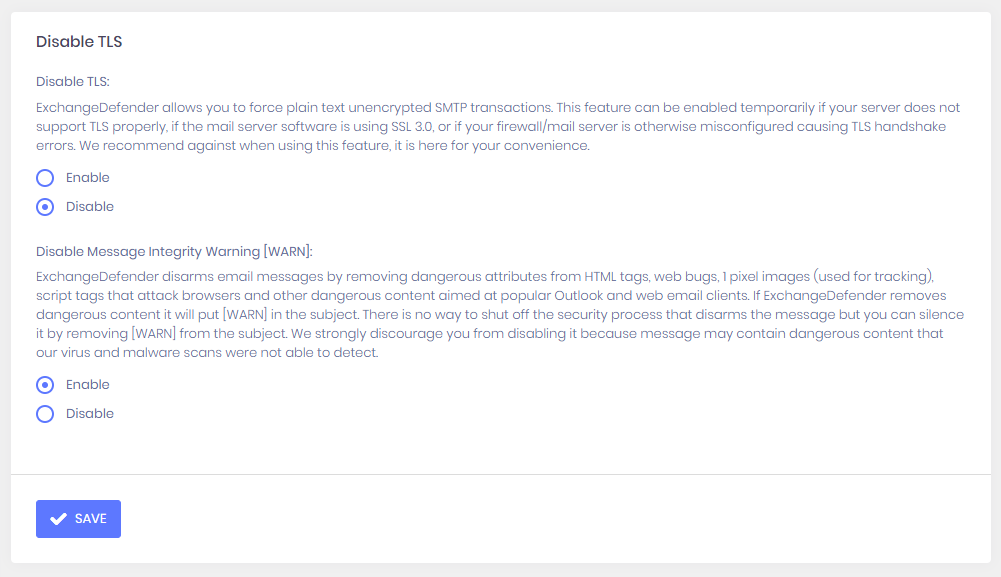
- Disable TLS - Manage TLS/SSL functionality of your domain.
- Report Options - ExchangeDefender Pro reporting features and schedules.
- SPF Records - DNS data for Sender Policy Framework (SPF) and DomainKeys (DKIM)
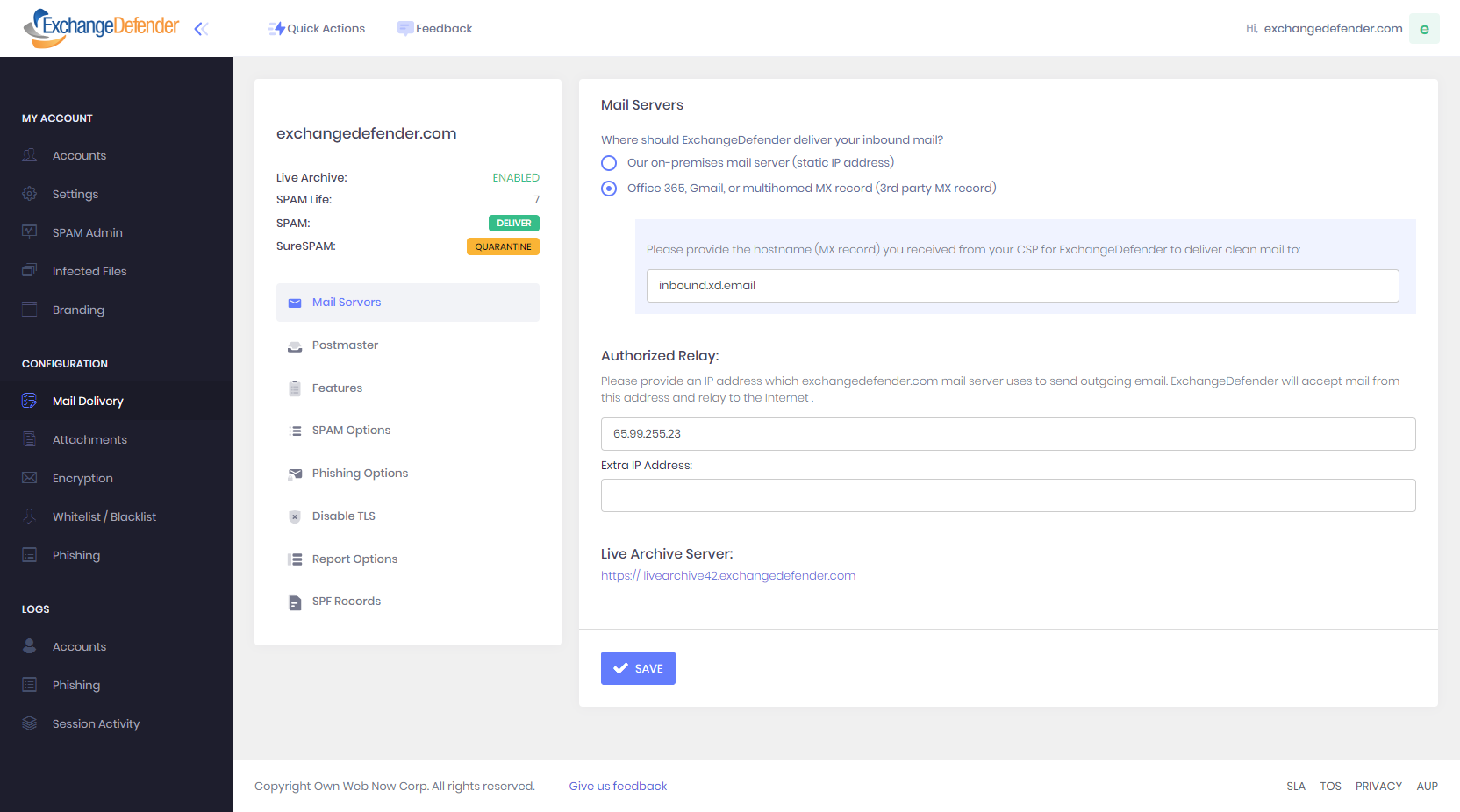
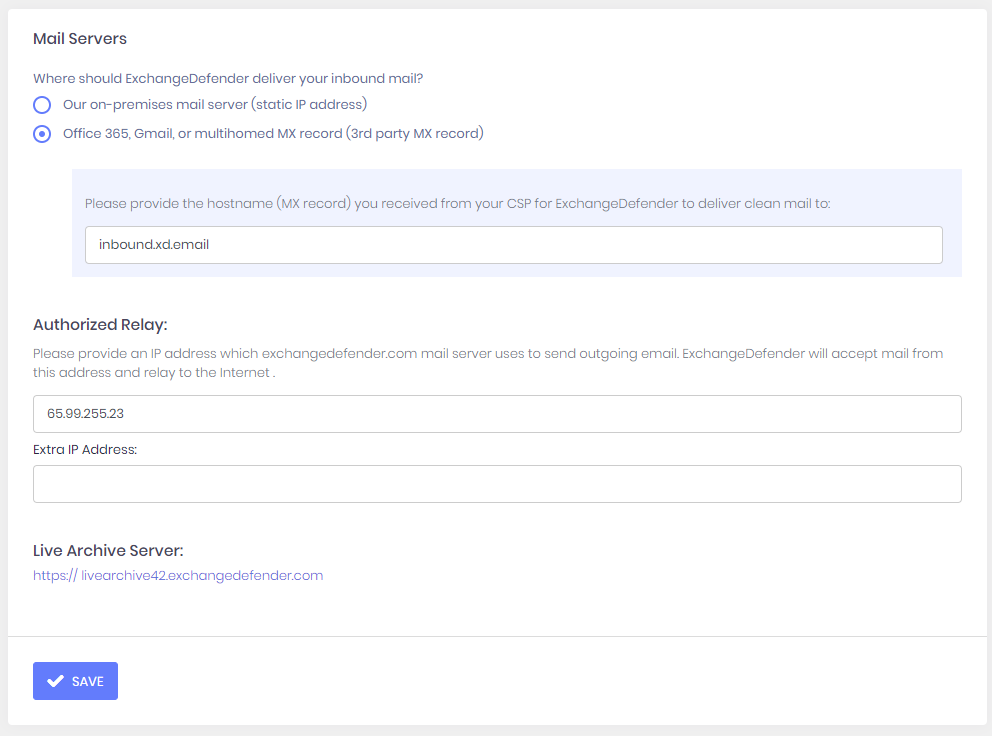
Mail Delivery - Mail Servers
ExchangeDefender Mail Delivery policies determine how ExchangeDefender routes your email.
Inbound Mail
Our on-premises mail server (static IP address) - If you choose this option you will be prompted for the IP address of your mail server. This must be a static IP address (ExchangeDefender can work with dynamic ranges, but it is unsupported and will result in mail loss).
Office 365, Gmail, or multihomed MX record (3rd party MX record) - If you choose this option you will be prompted for the MX record given to you by the 3rd party email provider. If you have multiple records either provide just the top one, or contact us about your DNS options to support multiple MX records.
Authorized Relays
ExchangeDefender can also relay outbound mail on behalf of your organization. You can provide up to 2 IP addresses that we will authorize to relay mail for your organization through our outbound mail infrastructure at outbound.exchangedefender.com.
LiveArchive
ExchangeDefender LiveArchive server for your organization.
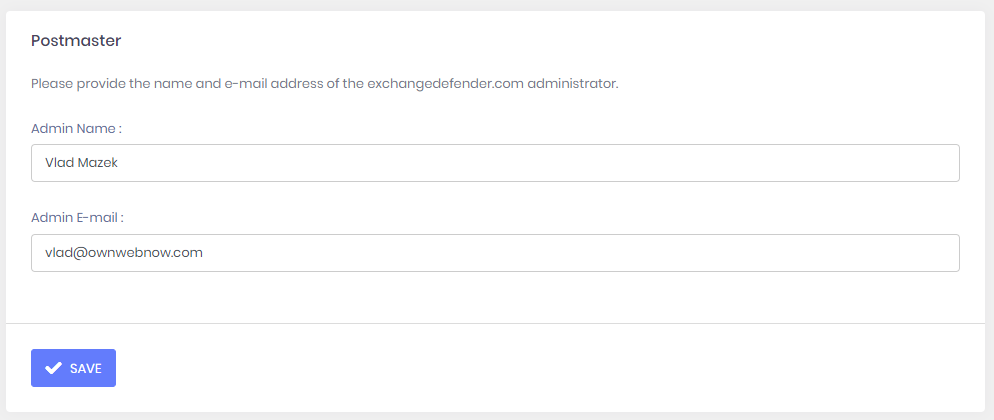
Mail Delivery - Postmaster
Mail Delivery - Features
ExchangeDefender enables you to disable and enable additional services.
- LocalCloud - ExchangeDefender service that stores ExchangeDefender processed attachments and logs in a secure, encrypted storage (for infected attachment delivery, queue files, etc)
- LiveArchive - ExchangeDefender service designed for mail resiliency and business continuity.
- Password Expiration - ExchangeDefender service designed to monitor accounts that haven't changed their password recently (to disable it, set the expiration to 0).
Mail Delivery - SPAM Options
- SPAM Life - Number of days that ExchangeDefender will keep SPAM messages and make them available for review/release.
- SPAM Action - ExchangeDefender has 3 options when it comes to handling SPAM messages.
- Tag & Deliver - When ExchangeDefender classifies a message as SPAM, it will append [SPAM] to the subject and deliver the message to the client.
- Quarantine - When ExchangeDefender classifies a message as SPAM it will quarantine the message on our network. Users can get a daily SPAM and intraday SPAM report that gets emailed to them, or through the admin portal at https://admin.exchangedefender.com , or through Outlook add-in, or through Windows Desktop client. ExchangeDefender Essentials can only access their quarantined messages via the portal. Once a message is quarantined it can be accessed, previewed, printed, replied to or forwarded, and it can also be released down to the client's mail server on demand.
- Delete - When ExchangeDefender classifies a message as SPAM it will delete the message. Please note that this action is not reversible , the message is discarded before being stored on any of our servers so there is no way to recover the message once it's been deleted.
- SureSPAM Action - ExchangeDefender has the same three options for handling SPAM. SureSPAM is a classification for SPAM messages that we have a 99.9% confidence that the message is SPAM based on its origin, patterns, and advanced SPAM detection.
Mail Delivery - Phishing Options
ExchangeDefender Phishing Options enable Domain Administrators to configure security policies that protect users from identity theft.
Phishing Protection - Configuration for ExchangeDefender Phishing Firewall. Disabling this feature requires a legal waiver as this policy forces us to deliver content we know is dangerous and exposes ExchangeDefender to legal liability if such dangerous content reaches your network.
SureSPAM Block My Domain Spoofing -Enabling this policy will flag all outbound mail from your domain as SureSPAM. Since all of your domains mail is local, or coming from a known authorized relay source, ExchangeDefender will categorize mail using your domain as SureSPAM when it comes from an unknown third party server. This feature is meant for organizations that cannot establish an SPF record.
ExchangeDefender Office Macro Protection - Enabling this policy will subject Microsoft OLE code to additional screening and warnings. Options for Office OLE protection are as follows:
- Off - Default, we will scan the attachment and enclosed files for known malware, viruses, trojans, etc. We ignore untrusted/usigned OLE code in Microsoft documents.
- On - If we detect dangerous/suspicious Microsoft OLE Macro code in the message from an untrusted (external) source that is not whitelisted, message will be categorized as SureSPAM.
- Strict - Same as on, but bypasses all other ExchangeDefender security checks (whitelists) and categorizes the message as SureSPAM
Subscription (Newsletter) Bomb Protection - Enabling this policy will make ExchangeDefender more aggressive in stopping known bulk-precedence SPAM and mailing list providers. Options for newsletter bomb protection are as follows and encouraged only as a temporary measure when you're experiencing an attack:
- Disabled - ExchangeDefender will ignore newsletter and bulk-mail specific content in the message and scan it as any other message.
- Enabled - ExchangeDefender will scan for newsletter and bulk-mail specific content and if detected, message will be catetgorized as SureSPAM.
- Whitelisted - ExchangeDefender will only allow newsletter and bulk-mail specific content from whitelisted senders. All other newsletters will be categorized as SureSPAM.
Flag External Emails - Enabling this policy will add [EXTERNAL] to the subject of every message that is received from outside of your organization. This policy can help protect organizations by clearly marking external messages so users do not accidentally open forged/spoofed messages from themselves or other members of your organization.
Mail Delivery - Disable TLS
ExchangeDefender allows you to disable industry standard security protocols if you are having issues sending or receiving certain types of messages. We strongly discourage you from disabling these features, and we offer these policies as a workaround.
Disable TLS- Disables a requirement for TLS messages, and enables your domain to send messages to hosts that do not have a valid SSL certificate.
WARNING: Enabling this setting allows ExchangeDefender to send email to the remote server without encryption, which might compromise your regulatory compliance requirement.
Disable Message Integrity Warning - Disables removal of suspicious attachments specifically designed to crash Microsoft Outlook.
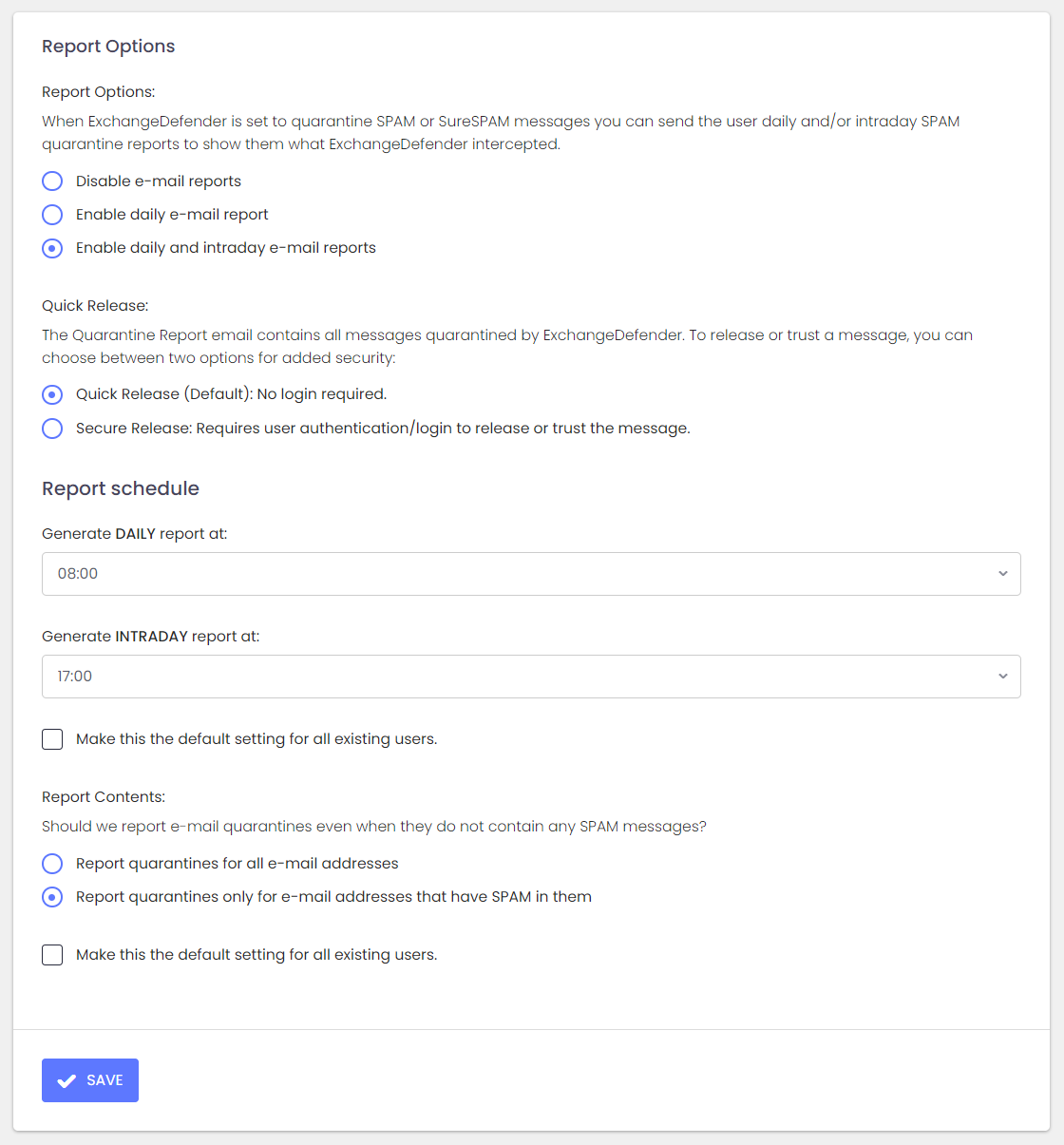
Mail Delivery - Report Options
Report Options - ExchangeDefender Pro allows users to receive up to two daily SPAM reports that contain a list of messages that ExchangeDefender quarantined as SPAM or SureSPAM. From that email report users can quickly see all the SPAM ExchangeDefender has caught and can whitelist or release the message just by clicking on a link in the email.
- Disable email reports - Do not send users quarantine reports at all.
- Enable daily email report - Send user a single daily email containing all the SPAM caught in the past 24 hours.
- Enable daily and intraday email report - Send users a single daily email containing all the SPAM caught in the past 24 hours and send an intraday report that contains all the SPAM caught since the daily report was generated. Intraday reports are meant for sales and executive personnel that needs to be reminded to check SPAM quarantines more often.
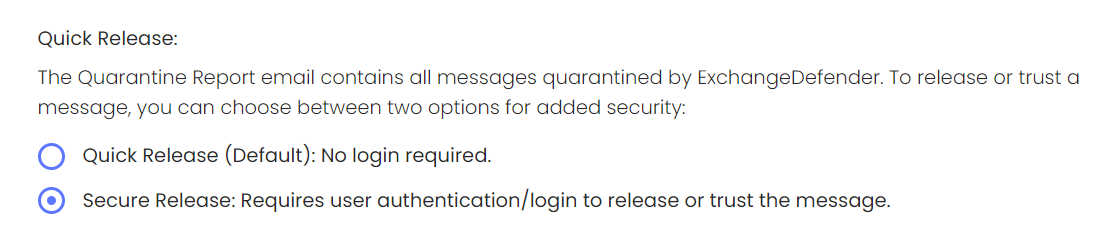
ExchangeDefender Quick Release Feature
Introducing the ExchangeDefender Quick Release feature, designed to offer flexibility between convenience and enhanced security in your release process. While a one-click release can be a significant time-saver for many organizations, it's essential to balance this with potential security risks.
For a Quick Release, simply select the Default option that requires no additional login.
Secure Release: Requiring Additional Security
- Secure Release Activation: ExchangeDefender provides a "Secure Release" setting, ensuring a more secure release process.
- Authentication Prompt: When users click to release or trust a message, they are prompted to authenticate, adding an extra layer of security.
- Protection Against Hacks: In the event of a compromised account or the introduction of link scanning/crawling software, messages remain inaccessible without proper authentication.
How to Activate Secure Release:
- Access your ExchangeDefender settings inside your dashboard at admin.exchangedefender.com
- Navigate to Quick Release preferences.
- Enable "Secure Release" for an added layer of protection.
Report Schedule
- Generate Daily report at - The time at which the SPAM report is generated. We recommend giving at least 30-60 minutes prior to the time you wish to receive the report. For example, if you want to be sure that the Daily SPAM report is in your Inbox by 9:00 AM, set the report time to 8:00 AM.
- Generate Intraday report at - The time at which the intraday SPAM report is generated.
Report Contents - The following settings determine if we sent the SPAM report and what sort of information it contains. For clients with lots of aliases it's best to select Report quarantines only for email addresses that have SPAM in them.
- Report quarantines for all email addresses - ExchangeDefender SPAM report will report SPAM for every mailbox that is protected for every given user. If there is no SPAM to report, the alias/mailbox in the report will simply say "No SPAM to report".
- Report quarantines only for email addresses that have SPAM in them - ExchangeDefender SPAM report will only be generated and sent if ExchangeDefender caught any SPAM during the past 24 hours (or the amount of time since the Intraday report).
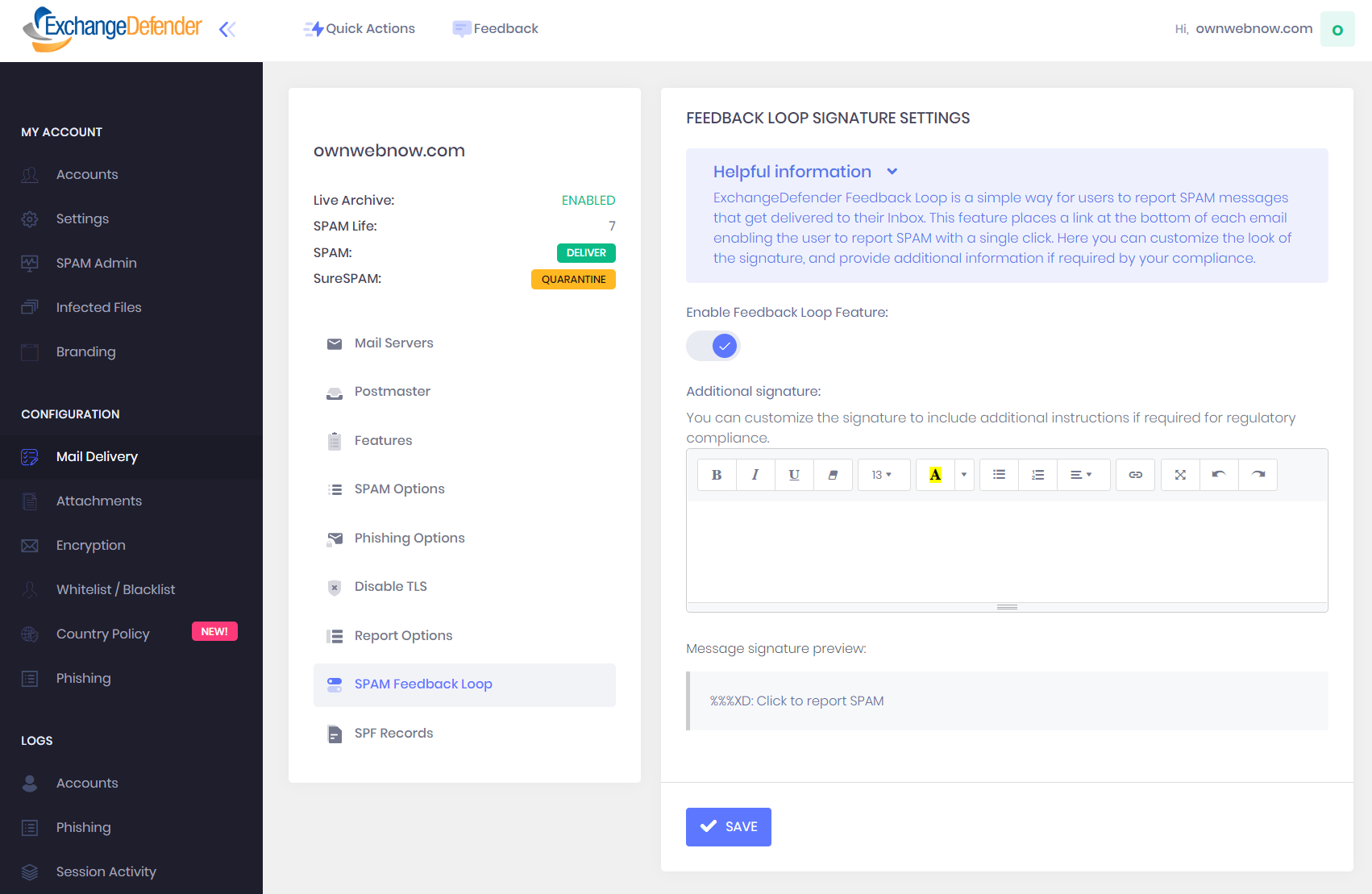
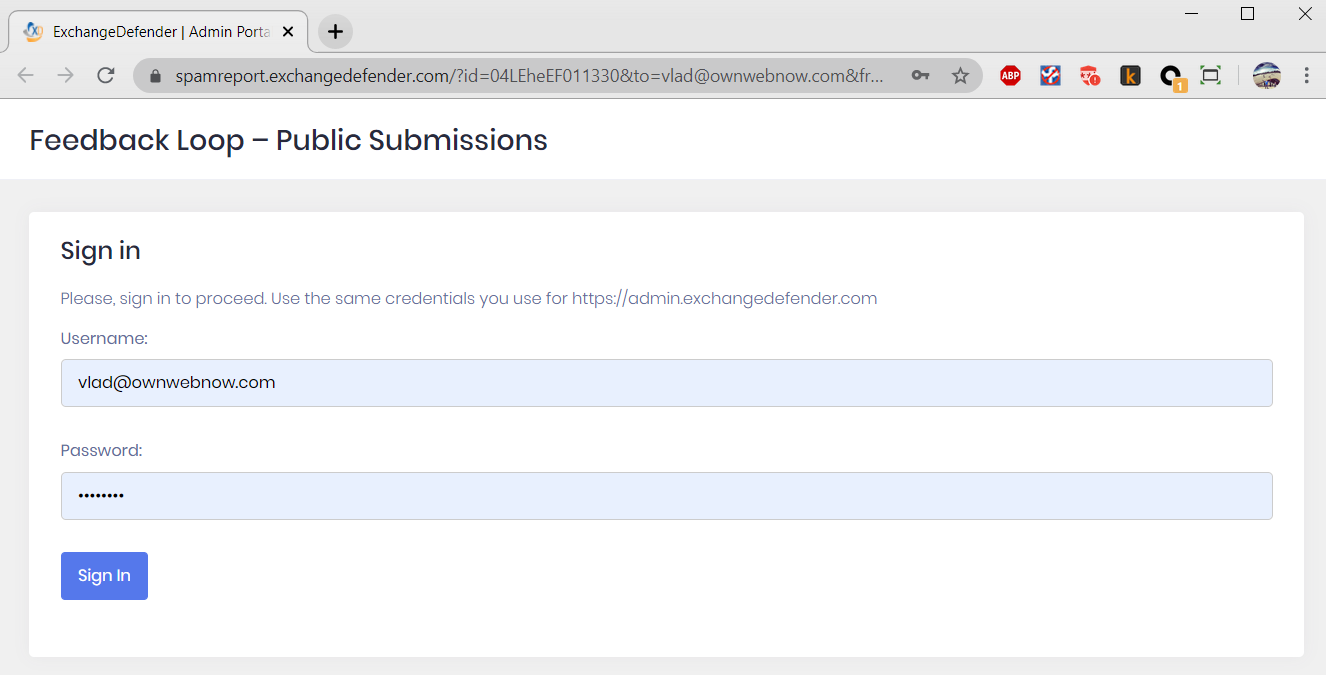
Feedback Loop - SPAM Reporting
ExchangeDefender SPAM Reporting (Feedback Loop) is a simple way for users to report SPAM messages that get delivered to their Inbox. This is a user-level feature in ExchangeDefender that inserts a link at the bottom of each processed email and gives users one-click reporting and blacklist management. Service providers and domain administrators can customize the appearance of the link that is automatically inserted at the bottom of the message.
How to access the Feedback Loop Feature
Login as the domain administrator And click on Mail Delivery > SPAM Feedback Loop. Click on Enable Feedback Loop Feature, make any optional additions to the signature, and click Save.
How to enable Feedback loop Reporting for Users
Once the feature has been enabled for the domain, Users will get a new feature in their Settings. Click on Settings > Settings > and click on the SPAM Feedback Loop to enable signatures for email addresses associated with this user.
Signature Design
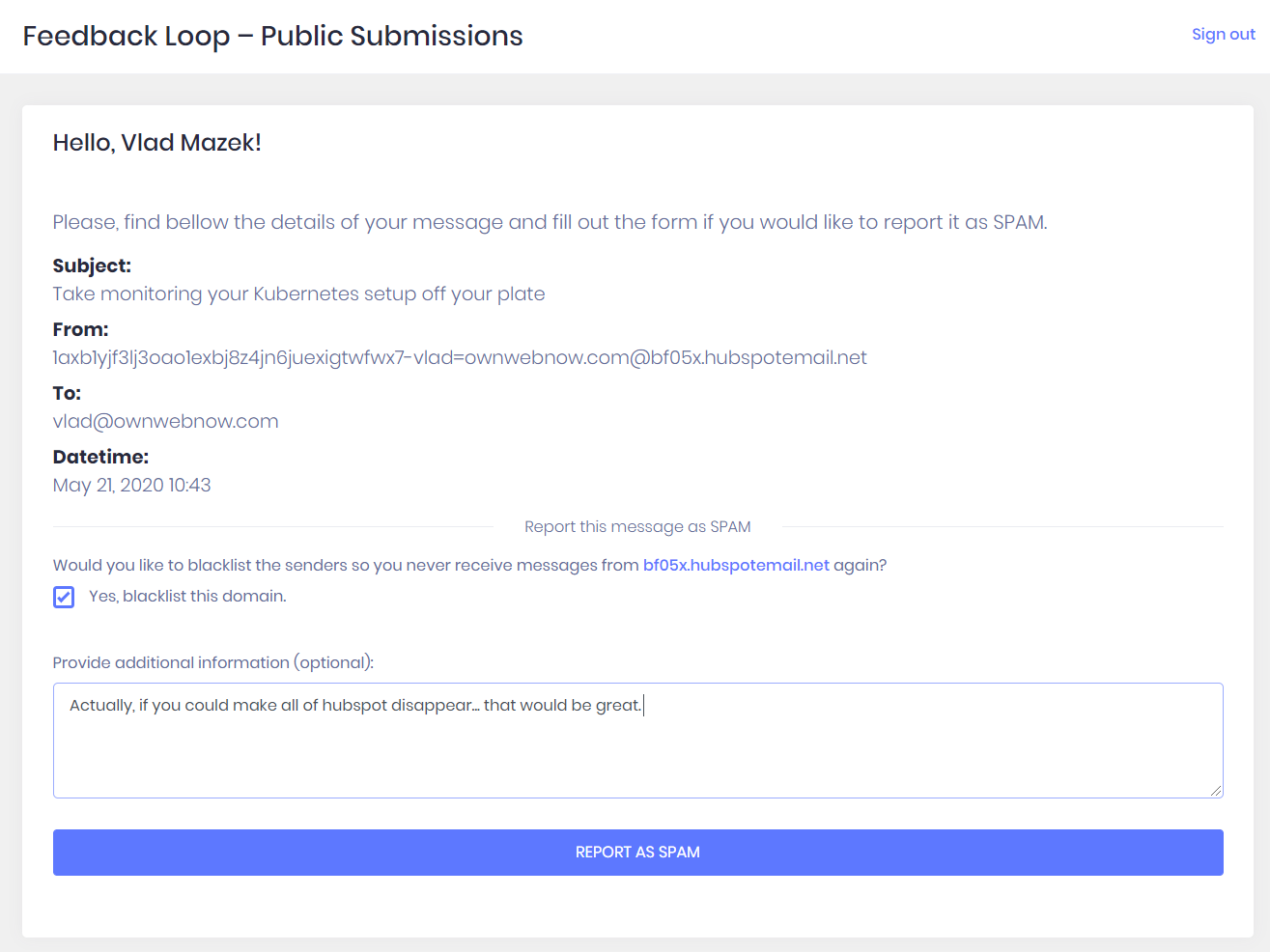
The signature you designed on the Domain admin level will appear at the bottom of every HTML/text message that arrives in your Inbox. When the users click on the link it will open a web browser and take them to their ExchangeDefender account (if they are not logged in, they will see the login screen).
Once authenticated, the user can review the message, confirm that's something they don't want to see again, and we'll look into it and make sure messages similar to the one they are reporting is not delivered to the Inbox.
Users also have an option of providing feedback, uploading a copy of .msg file, as well as a checkbox that will automatically place the sender domain on a blacklist.
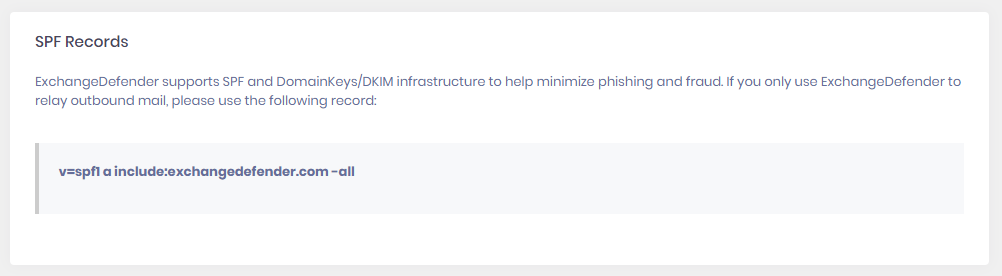
Mail Delivery - SPF Records
ExchangeDefender supports SPF and Domain Keys/DKIM infrastructure to help minimize phishing and fraud. If you only use ExchangeDefender to relay outbound mail, you would use the SPF record provided here. If you use other mail services to relay/send mail, they need to be a part of the SPF record. If you need any assistance with the SPF records, please contact your Domain Administrator and DNS admin, ExchangeDefender does not manage your DNS (SPF records).
Mail Delivery - DKIM Records
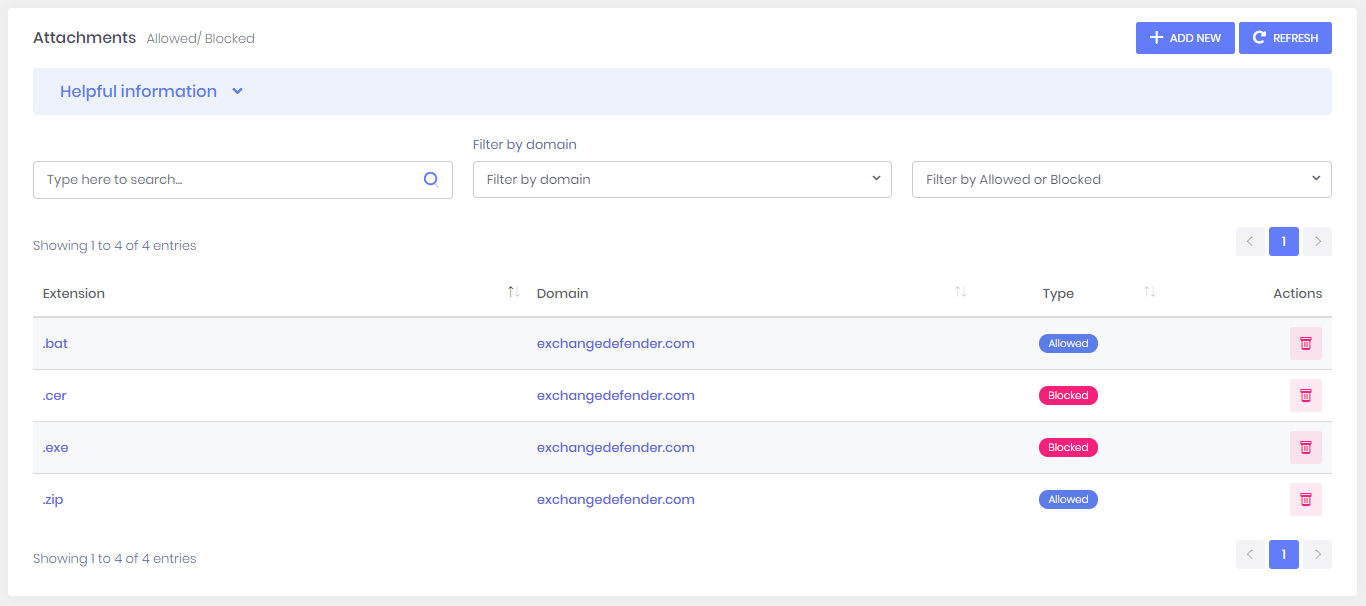
Configuration - Attachments
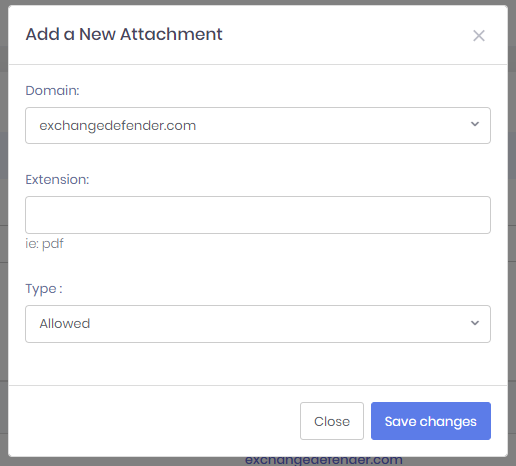
ExchangeDefender enables domain administrators to create a complex attachment handling policy. Whether you want to explicitly allow or deny certain attachments, you can do so from this screen. To add new attachment policies please click on +Add New.
ExchangeDefender Attachment Policy engine will allow the message containing prohibited attachments to pass through to the recipient, but the attachment will be replaced with a warning explaining why the attachment was stripped. If the attachment is absolutely necessary, Domain Administrators have the ability to retrieve attachments and infected files.
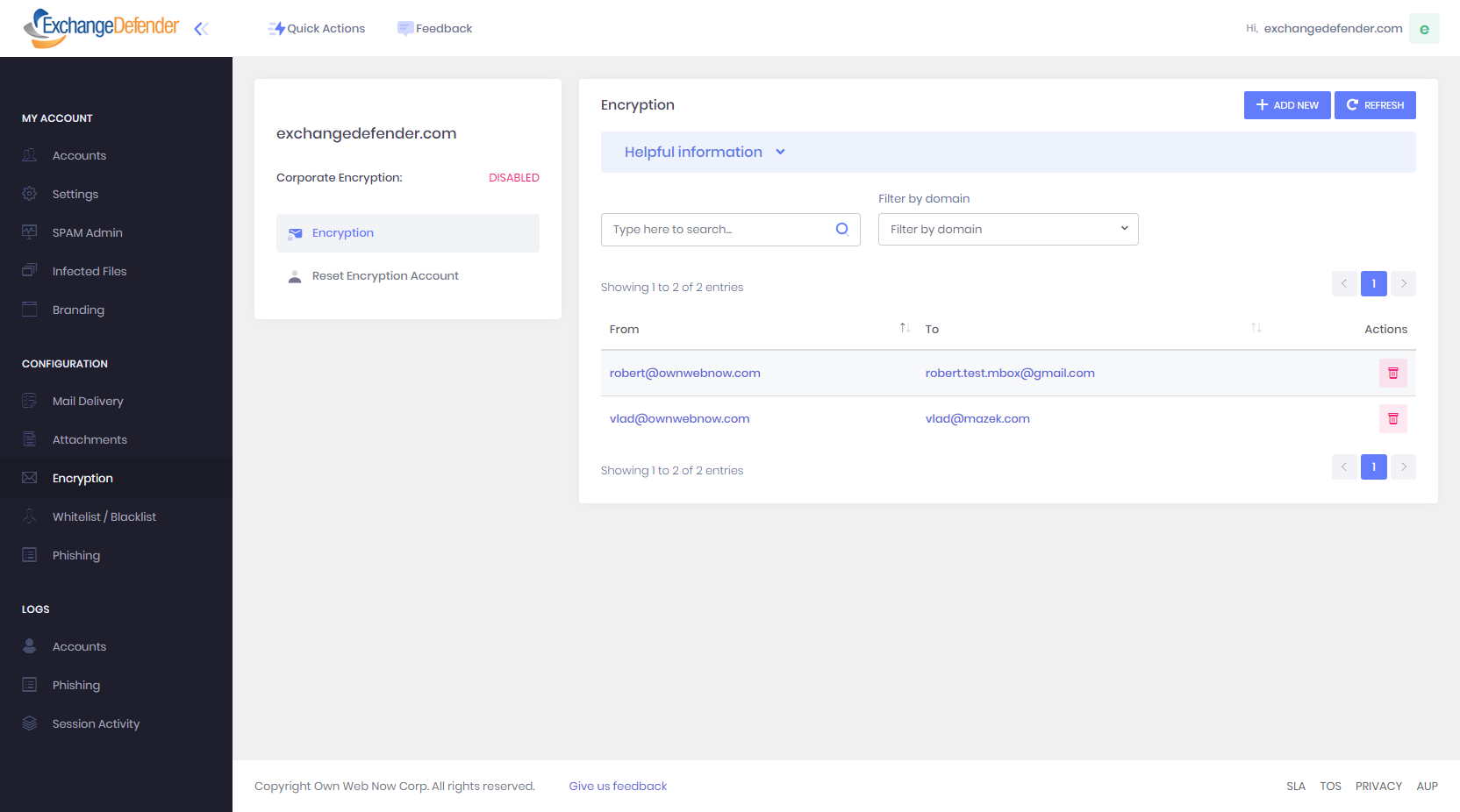
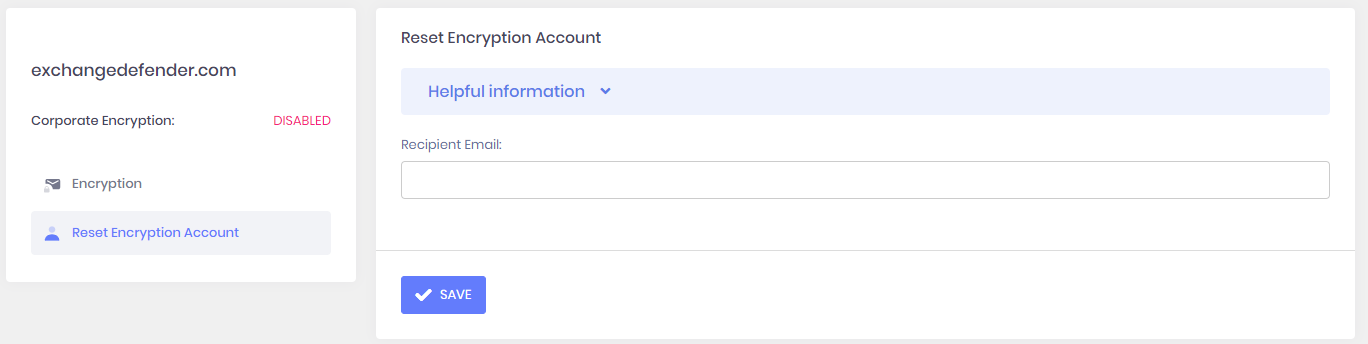
Configuration - Encryption
ExchangeDefender features a comprehensive Corporate Encryption service, but if you aren't subscribing to it yet you can still rely on ExchangeDefender to encrypt sensitive information free of charge. This section allows you to create Encryption Policies so that messages that match the From/To rule will always be encrypted by ExchangeDefender.
Domain Administrators also have the ability to reset the Corporate Encryption account of their recipient if they forget their login credentials for https://encryption.exchangedefender.com.
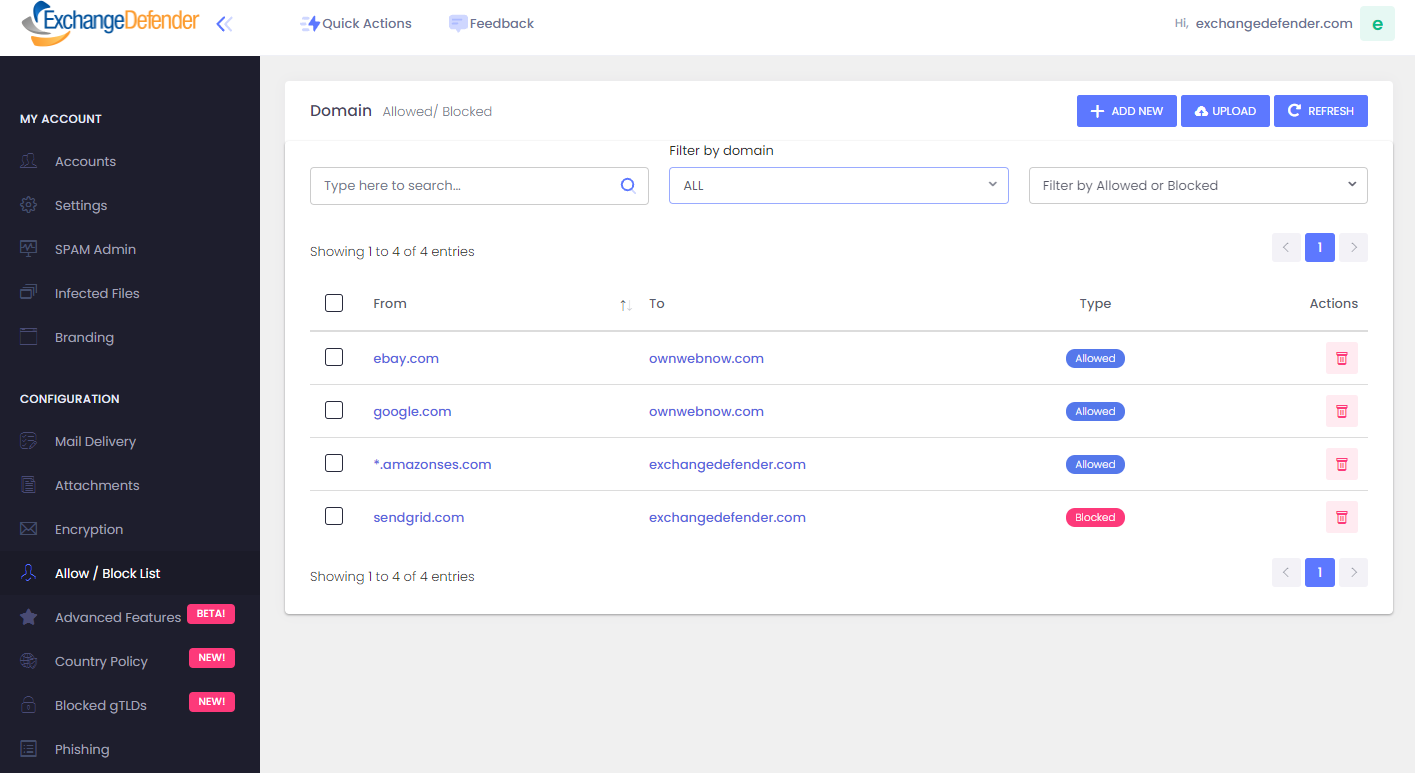
Configuration - Allow / Block List
ExchangeDefender Domain Administrators can create domain-wide organization allow and block lists policies that users cannot override or change. If your organization explicitly trusts or bans communication from some companies, you can define their domains and addresses here and they will either bypass or trigger SPAM protection.
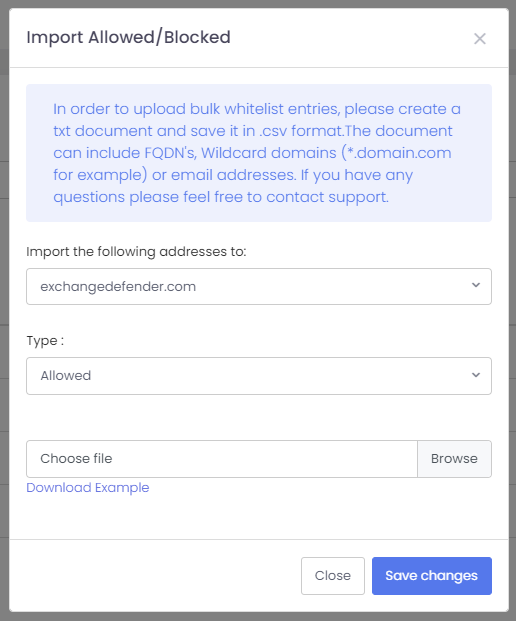
ExchangeDefender also enables you to upload files with the list of allowed or blocked domains instead of typing each domain at a time. Just create a csv file in Microsoft Excel (or your choice of spreadsheet) and provide a domain, email address, or subdomain one entry per line.
ExchangeDefender Policy Import / Export
ExchangeDefender Allow and Block policies are one of the most important tools for controlling mail flow into your mailbox and organization. ExchangeDefender makes them available on the Service Provider level, Domain level where they apply to every user in the organization, and User level where they are managed by the end user themselves by interacting with ExchangeDefender and their mail flow. ExchangeDefender makes it easy to export and import allow and black lists and manage your policies in bulk.
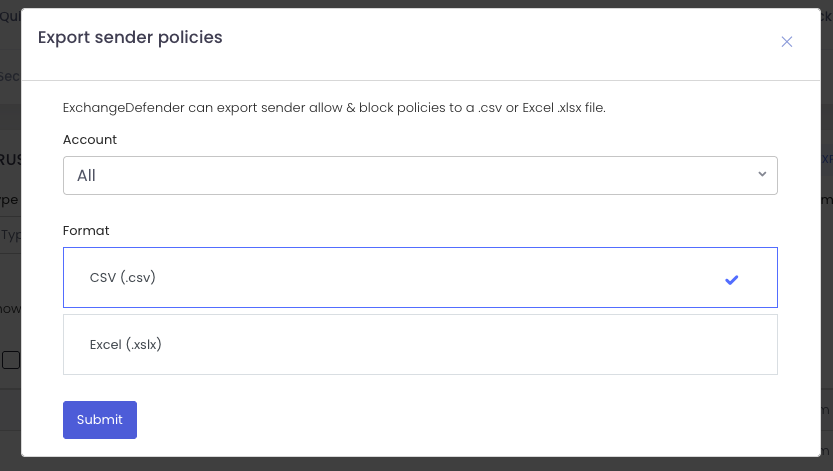
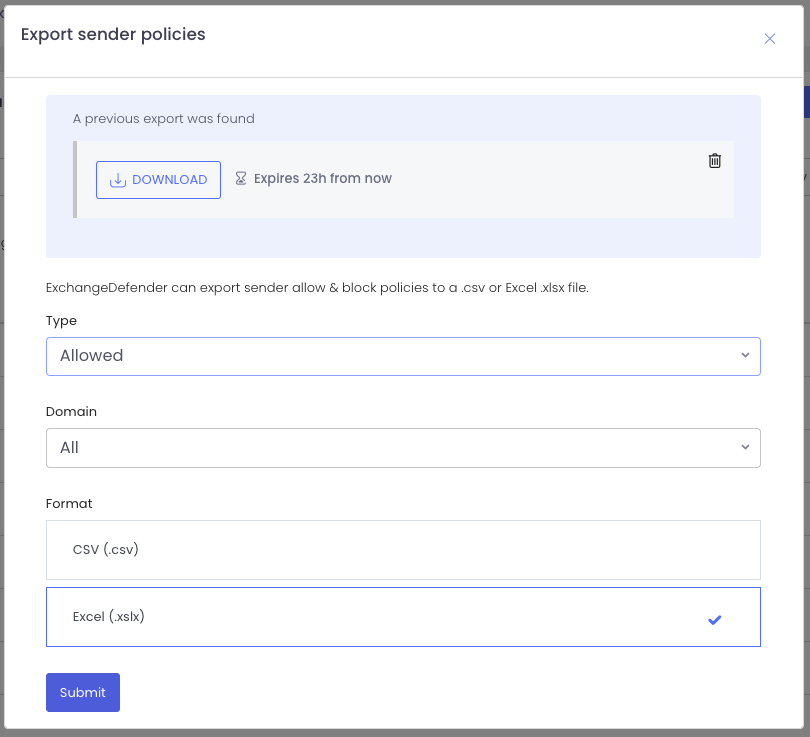
Export Formats: .csv and Excel .xlsx
Used for: Mass review & cleanup (export all your entries, sort/filter them in Excel, remove duplicates or outdated senders and reimport the clean list), Policy sharing (send policy to compliance teams, auditors, or SOC analysts), Integration with SIEM, logging or analytics systems for deeper insights into mail flow. Mostly, for faster onboarding.
Go to https://admin.exchangedefender.com. Go to your Trusted Senders (as user) or Allow / Block List (as domain admin) and you will see an Import and Export button on the top left. The interface is simple and intuitive.
To export your existing policies just click on the export button and give us the scope of the export. You can narrow down by policy (allowed or blocked) and you can pick .csv or Excel .xlsx as an export format. Your download is ready in the link next to the export button and will be available for the next 24 hours:
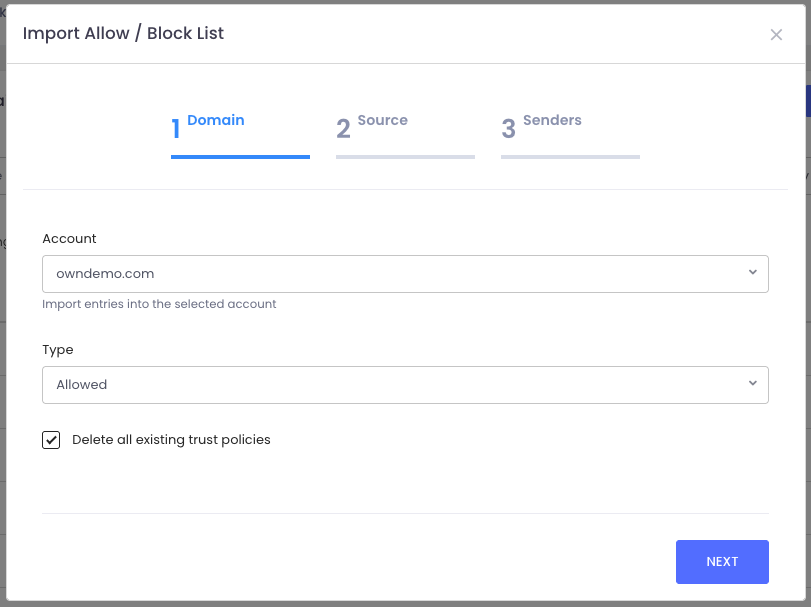
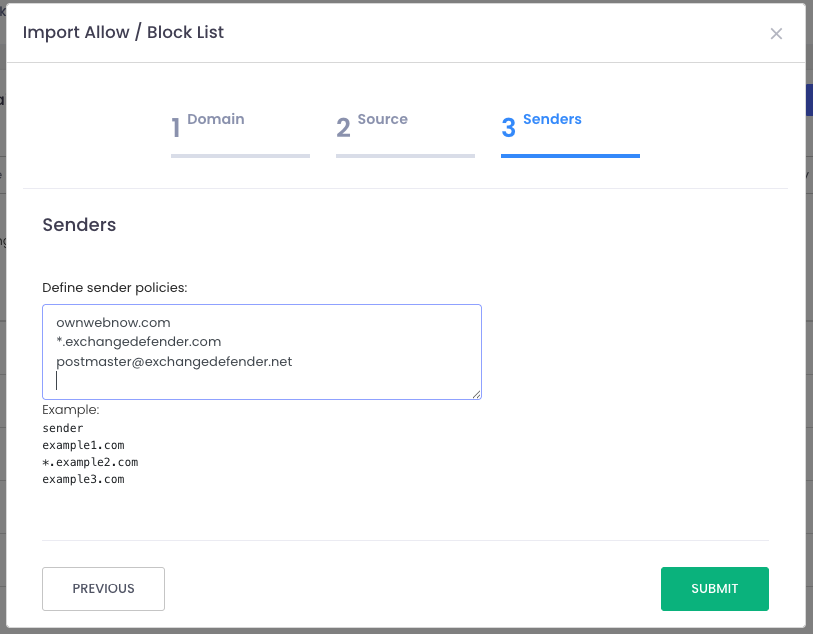
Import
Select the domain name and the policy type you are about to import. If you check "[ ] Delete all existing policies" we will delete all your existing policies and import the ones you provide. If you do not check this box, policies you import will be added to the existing list.
Import formats: Upload a .csv file or Manually type/paste in sender policies.
Just import the file and the system will create all policies for you or follow the example format to type them in manually, one address per line.
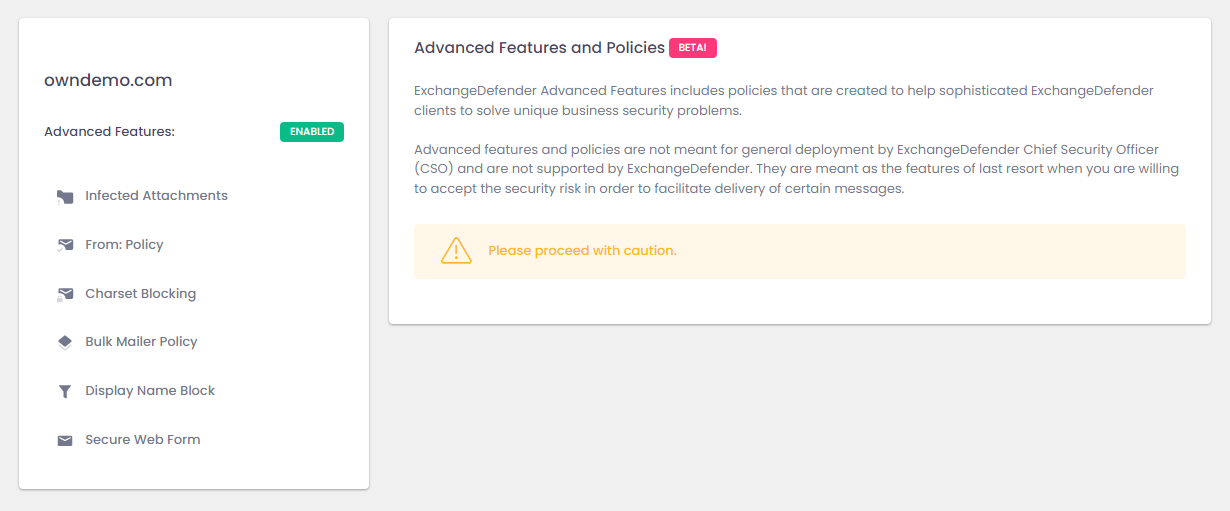
Configuration - Advanced Features
ExchangeDefender Advanced Features includes policies that are designed for the advanced ExchangeDefender admins who need a powerful policy to allow or block very specific types of email traffic. Because these features require special consideration, testing, and implementation there is no technical support for them offered by ExchangeDefender.
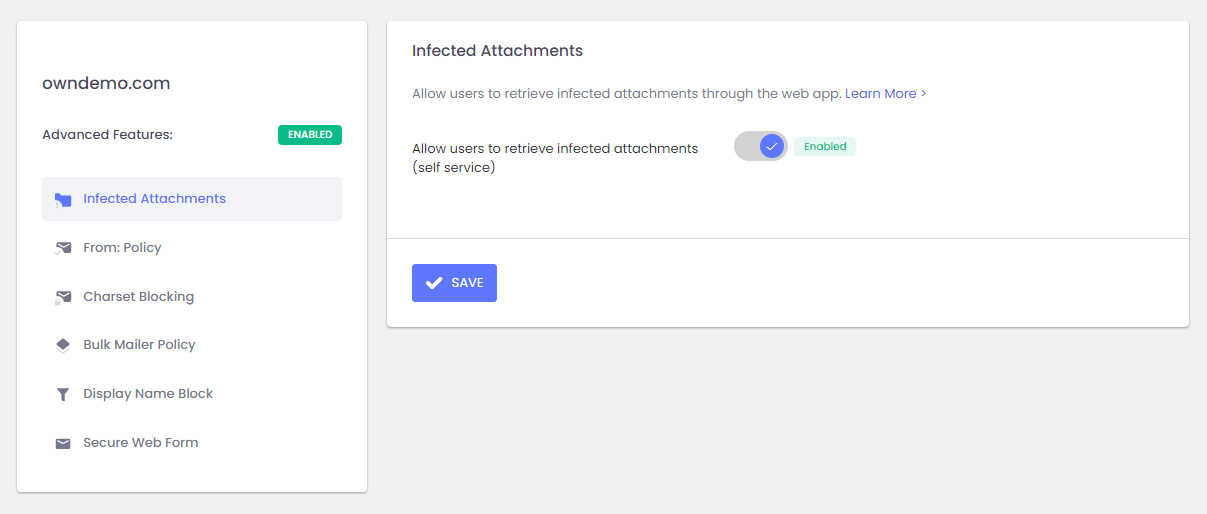
Advanced Features -Infected Attachments
ExchangeDefender allows domain administrators to retrieve infected attachments on behalf of users. Enabling this policy allows users to retrieve infected attachments through their account at https://admin.exchangedefender.com . ExchangeDefender recommends disabling this policy (off by default) because infected attachments should only be accessed by trained IT staff in a sandbox environment. Allow users to retrieve infected attachments (self service)
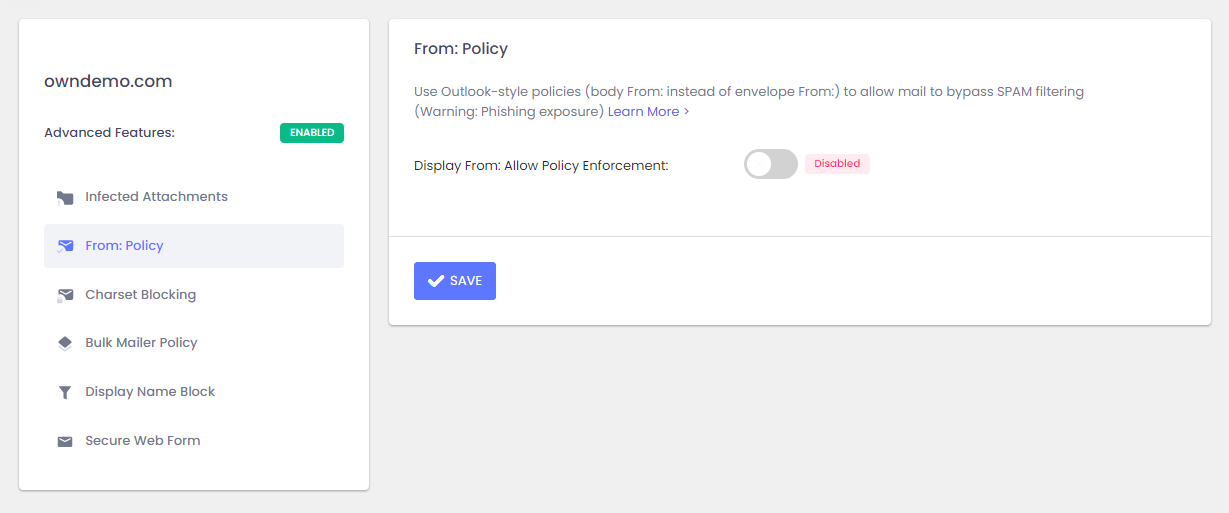
Advanced Features - From: Policy
ExchangeDefender enforces Allow Policies based on the envelope-sender From: address, which is the address the email actually comes from. This address has to comply with SPF, DKIM, DMARC and other standards and is difficult to forge. End user applications (Outlook, Gmail, Thunderbird, etc) show the more friendly "Display From:" address which can easily be forged and is frequently forged by automated mail systems.
Difference between envelope-sender and Display From
Many automated email systems (AWS, MailGun, MailJet, MailChimp, Constant Contact) use a different envelope-sender and display-from email addresses:
1) envelope-sender address is a system generated random email address that is unique to each email the system sends, and if the message needs to be returned for any reason it will be returned to that address. This is the only address that must conform to SPF, DKIM, and DMARC security protocols and makes it nearly impossible to forge.
2) display-from address is a more friendly looking email address that is displayed by the email client (Outlook, Gmail, Thunderbird, etc) so the user knows which domain the message came from. It does not have to comply with SPF, DKIM, or DMARC and can be easily forged by anyone.
Example envelope-sender From:
vlad=exchangedefender-com.81eql2.wo190@east-1.aws.amazon.com
Example Display From:
orders@amazon.com
The problem arises when ExchangeDefender user attempts to create an Allow Policy because they always want to receive emails from orders@amazon.com for example. Because the envelope-sender address is changed every time (to track every delivery issues) the only way to assure every email comes in is to create an Allow Policy for the whole sender domain.
ExchangeDefender From: Policy allows you to lower ExchangeDefender's security enforcement and allow it to consider display-from address (likely forged) when scanning for email. This is the default behavior of consumer email software (Outlook, Gmail) which is why clients often get compromised by phishing emails. However, we understand that there may be business requirements and additional security layers in place to minimize that so you can allow ExchangeDefender to work less securely by enabling this policy.
This policy enables ExchangeDefender to use Allow Policy with the potentially forged Display From: address (which will lower the security profile to that of M365/Gmail services).
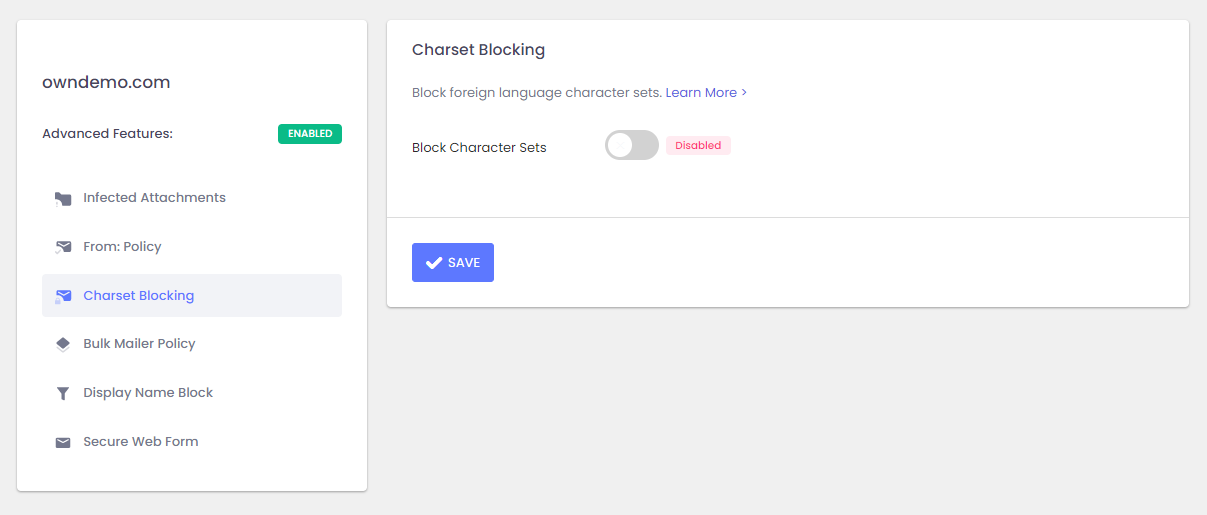
Advanced Features - Charset Blocking
ExchangeDefender can block specific character sets which is helpful when you want to block messages for clients that only communicate with locals. Please note this filter only works for legitimate mail, spammers tend to mask the actual character set.
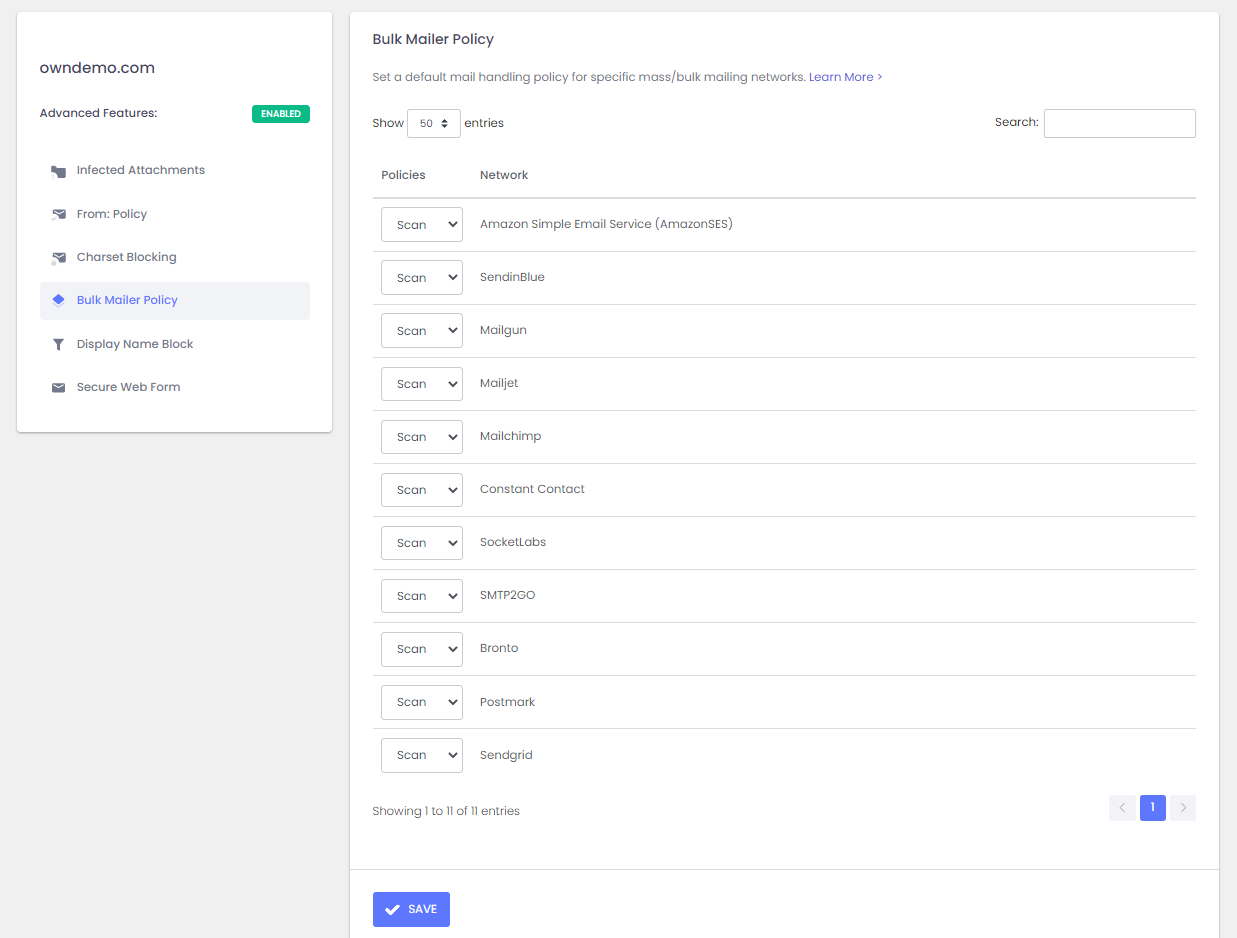
Advanced Features - Bulk Mailer Policy
ExchangeDefender enables you to better manage how mail from bulk (mass mailing) operations gets categorized. Due to the simplicity and lack of security enforcement of these networks (they get paid for every message sent) they carry both legitimate and dangerous content.
By default ExchangeDefender will Scan each message and categorize it as clean or SureSPAM based on the content. If you often receive messages from these networks that our scanning systems categorize as SPAM (due to their marketing content nature) you can enforce an Allow policy to make sure all messages from the network arrive in your inbox. If you would like to keep all messages away from your Inbox you can enforce a Block policy.
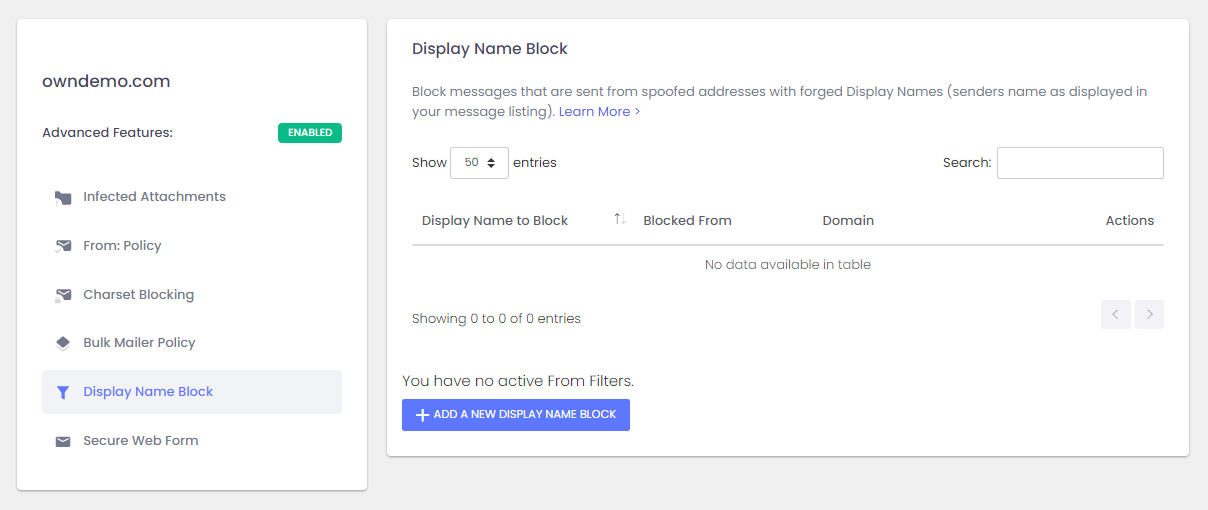
Advanced Features - Display Name Block
ExchangeDefender enables you to filter forged "From:" lines. Hackers often use a name familiar to the user, such as the CEO or members of the management, hoping that users will recognize the name and click on the message that contains dangerous content.
Display Name Block enables you to context-block messages from predefined display names and email addresses. ExchangeDefender will scan the incoming email from line (which typically looks like "From: Vlad Mazek <vlad@exchangedefender.com>") and categorize the message as SureSPAM if the blocked name doesn't match the email address. Please note that this is a very aggressive SPAM filtering policy that will be applied every time a blocked name match is found.
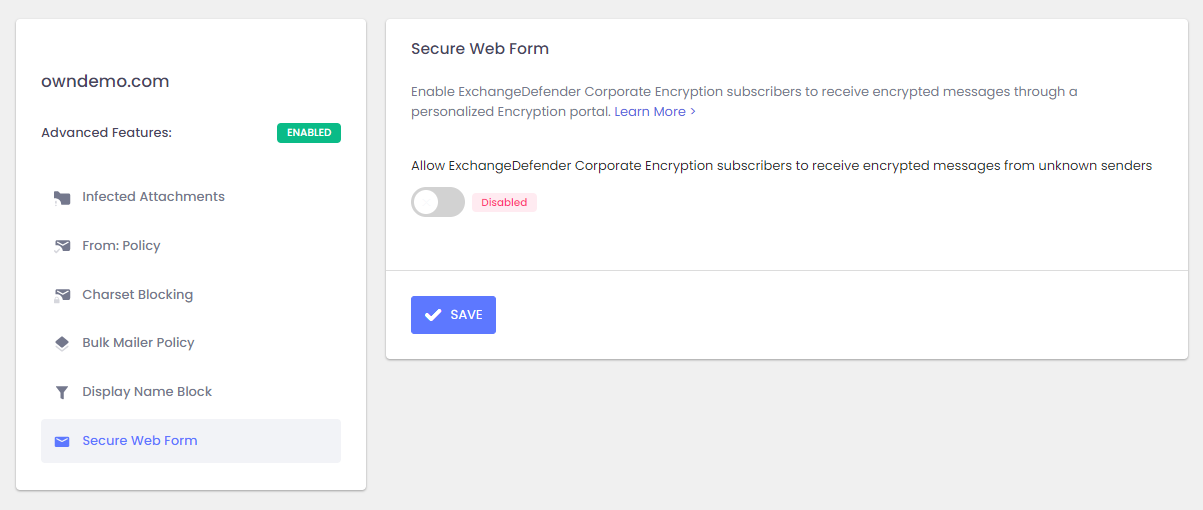
Advanced Features - Secure Web Form
ExchangeDefender Encryption can help your clients receive encrypted messages. This feature is helpful when your clients need to receive confidential materials securely but the sender does not have access to email encryption - they can simply go to a URL and send an email to you at any time (ex: https://encryption.exchangedefender.com/ownwebnow.com/vlad)
Allow ExchangeDefender Corporate Encryption subscribers to receive encrypted messages from unknown sender
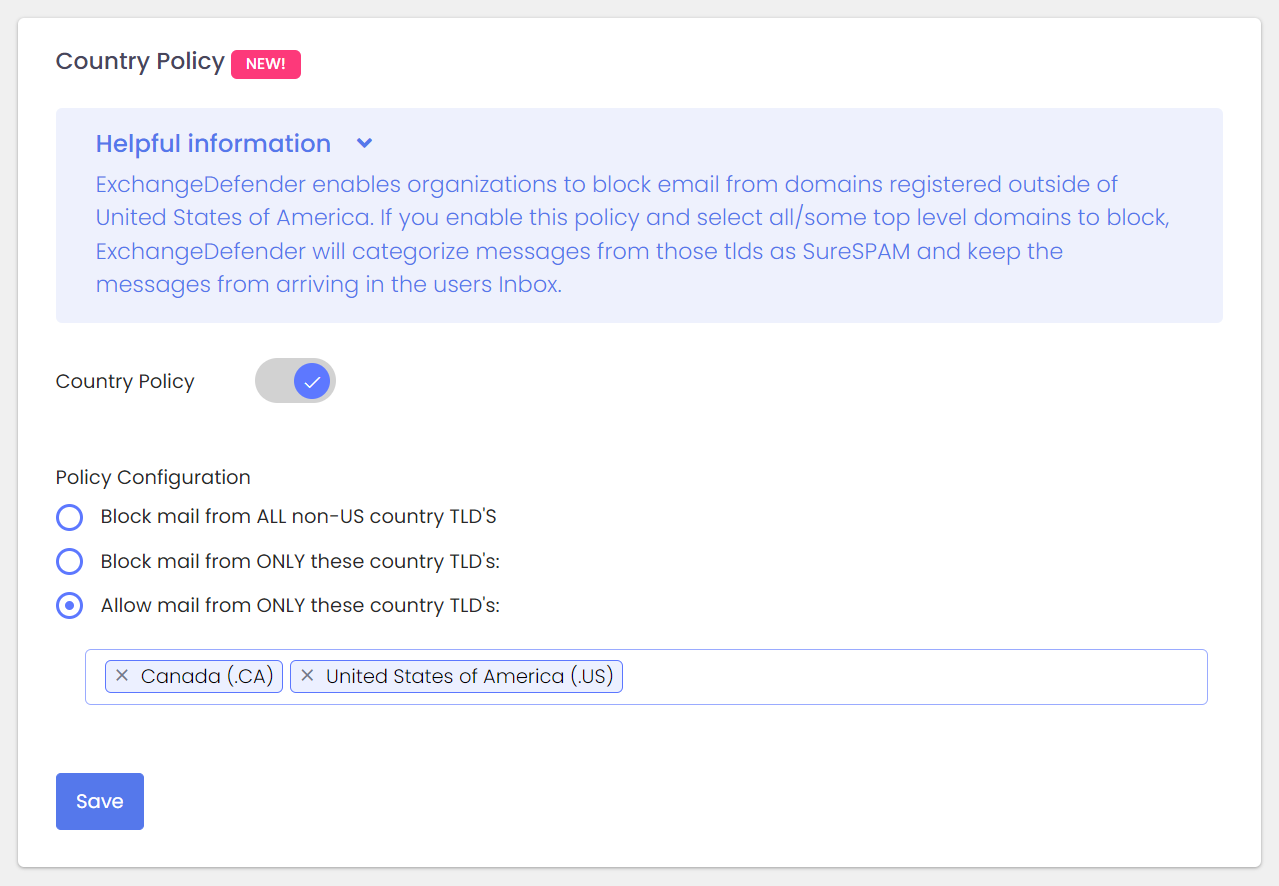
Configuration - Country Policy
ExchangeDefender Country Policy enables ExchangeDefender administrators to create country-specific routing policies and restrict access to their tenant/domain to specific countries. Simply type in the name or the tld of the country you wish to block and ExchangeDefender GeoIP will apply the policy on receipt and categorize mail from these countries as SureSPAM.
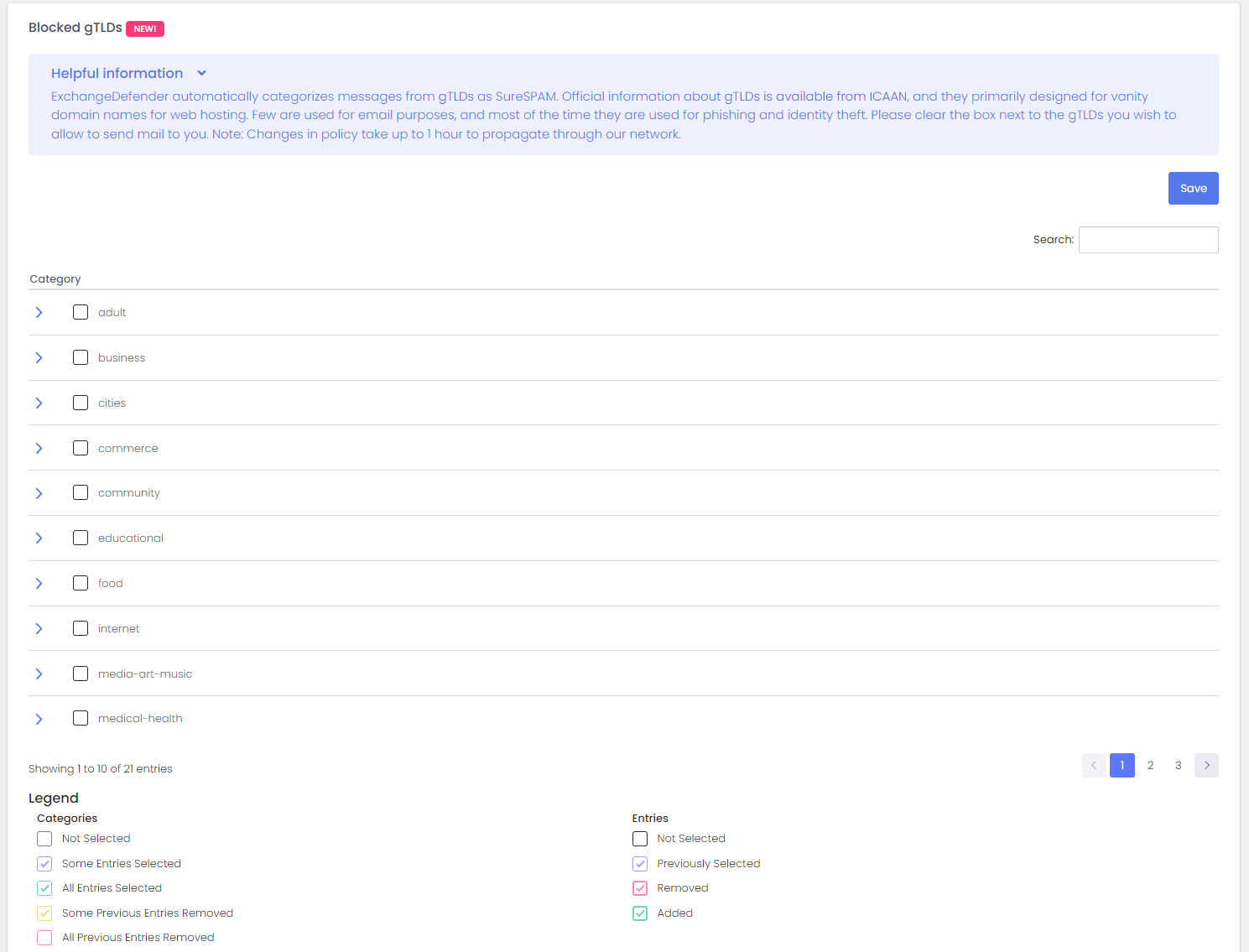
Configuration - Blocked gTLDs
ExchangeDefender automatically categorizes messages from vanity gTLDs as SureSPAM and keeps them out of the mailbox. These vanity tlds are generally used for web sites and many registrars lack the reputation or publish domain registration details which makes them extremely attractive for hackers and spammers.
Any changes to this policy are applied within 1 hour of change.
Simply click on the top level domain category to get started.
To accept mail from the tld, clear the checkbox next to the tld or category.
To block the tld from emailing you, check the checkbox next to the tld or category.
As you manage your permissions keep this legend in mind:
[ ] Not selected, all tlds are allowed.
[ ] Purple - Some entries are selected
[ ] Green - All entries are selected.
[ ] Yellow - Some entries that were checked before are now allowed.
[ ] Orange - Some entries that were allowed before are now blocked.
[ ] Red - All entries that were previously blocked are now allowed.
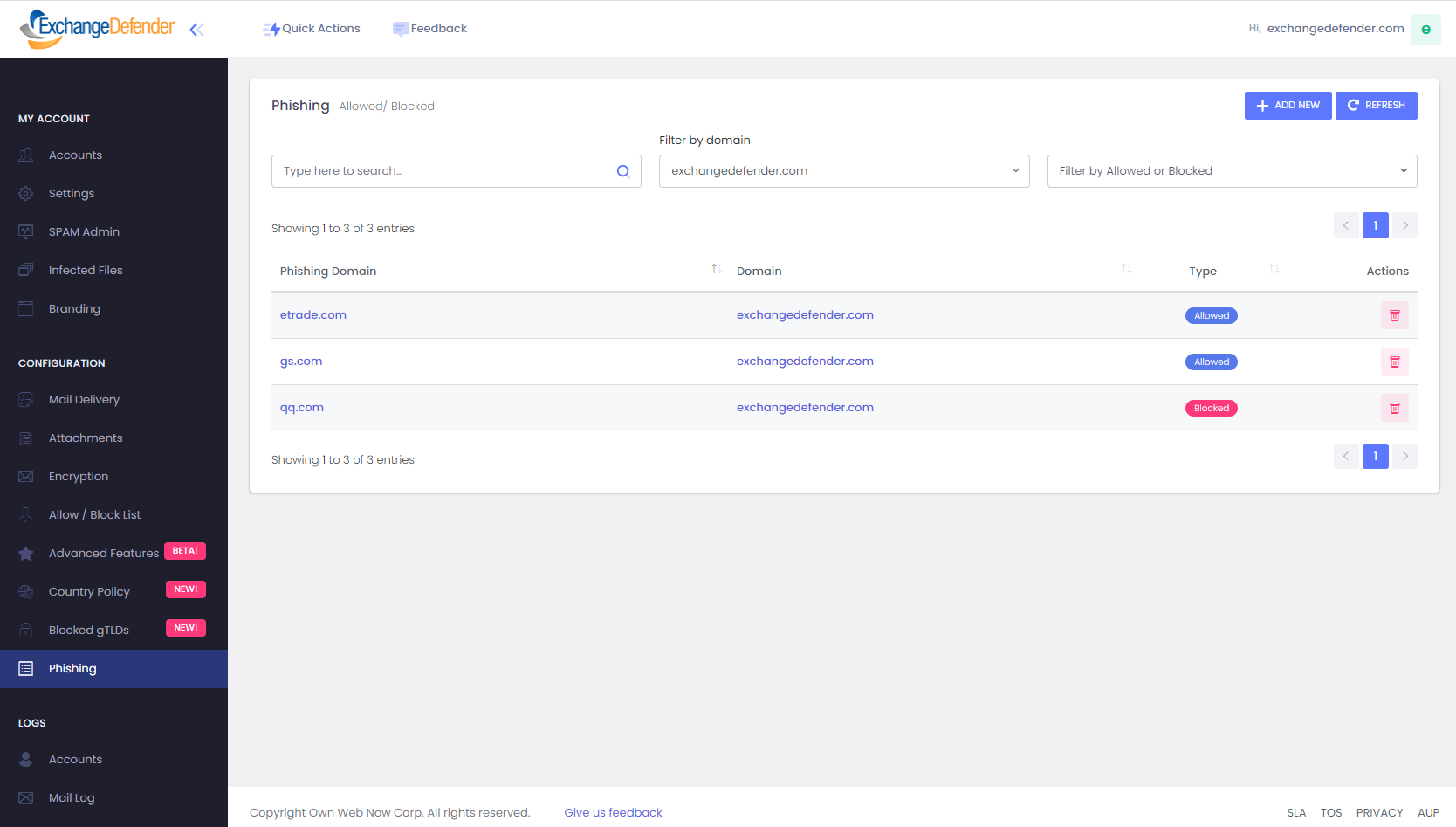
Configuration - Phishing
ExchangeDefender Phishing Firewall supports allowed and blocked policies for URLs from trusted or banned domains. Whenever ExchangeDefender PF encounters a hyperlink in the email it rewrites it so that it is proxied through our firewall at https://r.xdref.com
Allowed domain names do not get rewritten, and the user will automatically be redirected to the target domain.
Blocked, or banned, domains will have the link deactivated and will be presented with a warning when they attempt to go to the site.
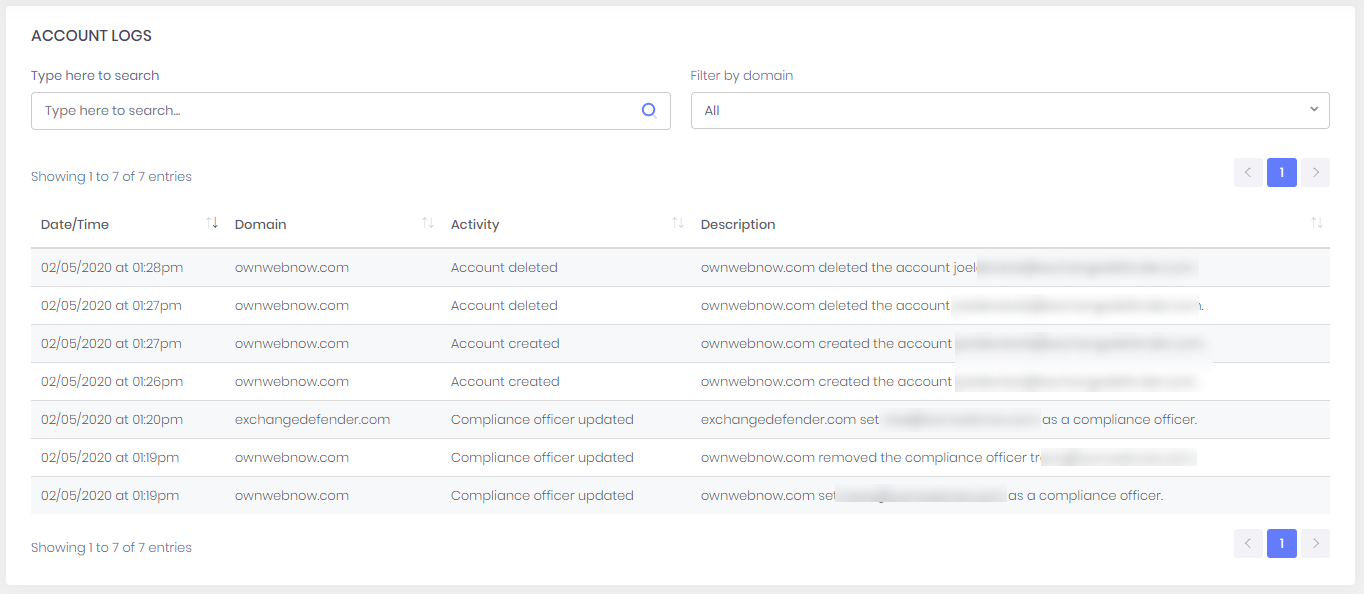
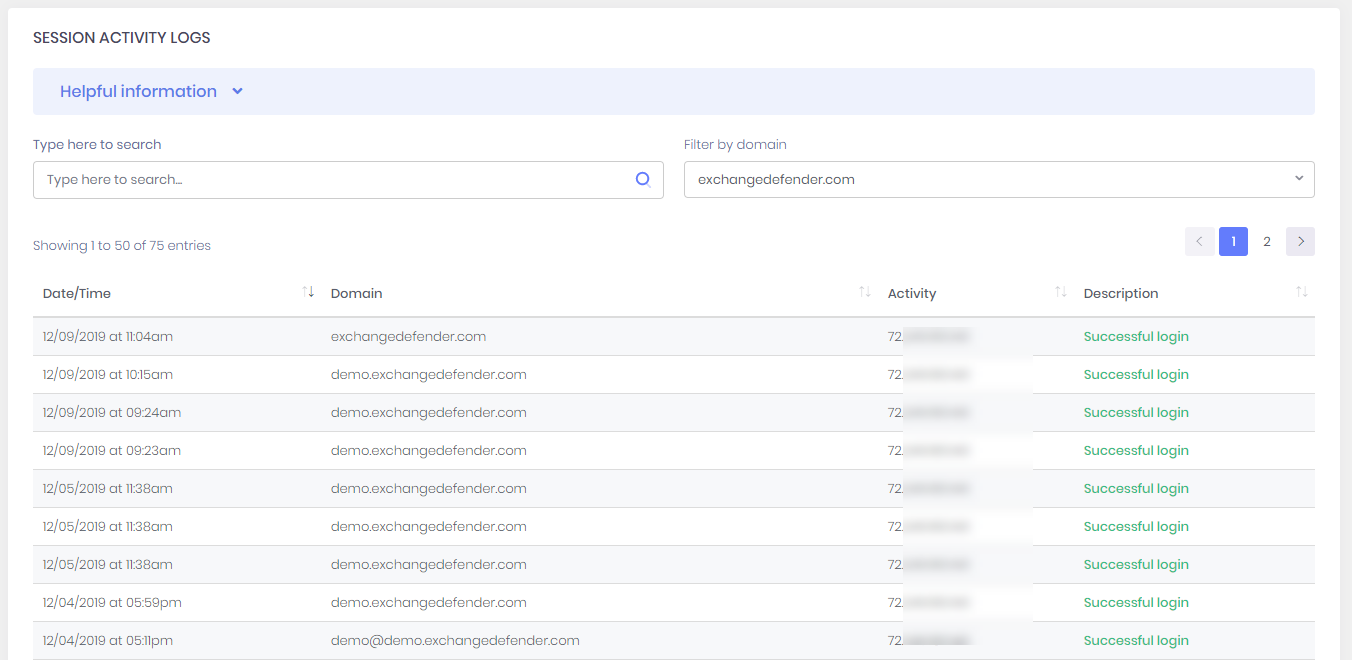
Logs - Accounts
ExchangeDefender Logs features extensive logging and security audit tools that can help domain administrators track login activity for security and troubleshooting purposes. The security audit log can be done on a Domain basis or you can click on Users to show the security login by email address.
The Accounts Log shows all account/domain policy changes so changes can be audited and tracked. The screen will show you the activity, description, time of the activity, and the source IP address.
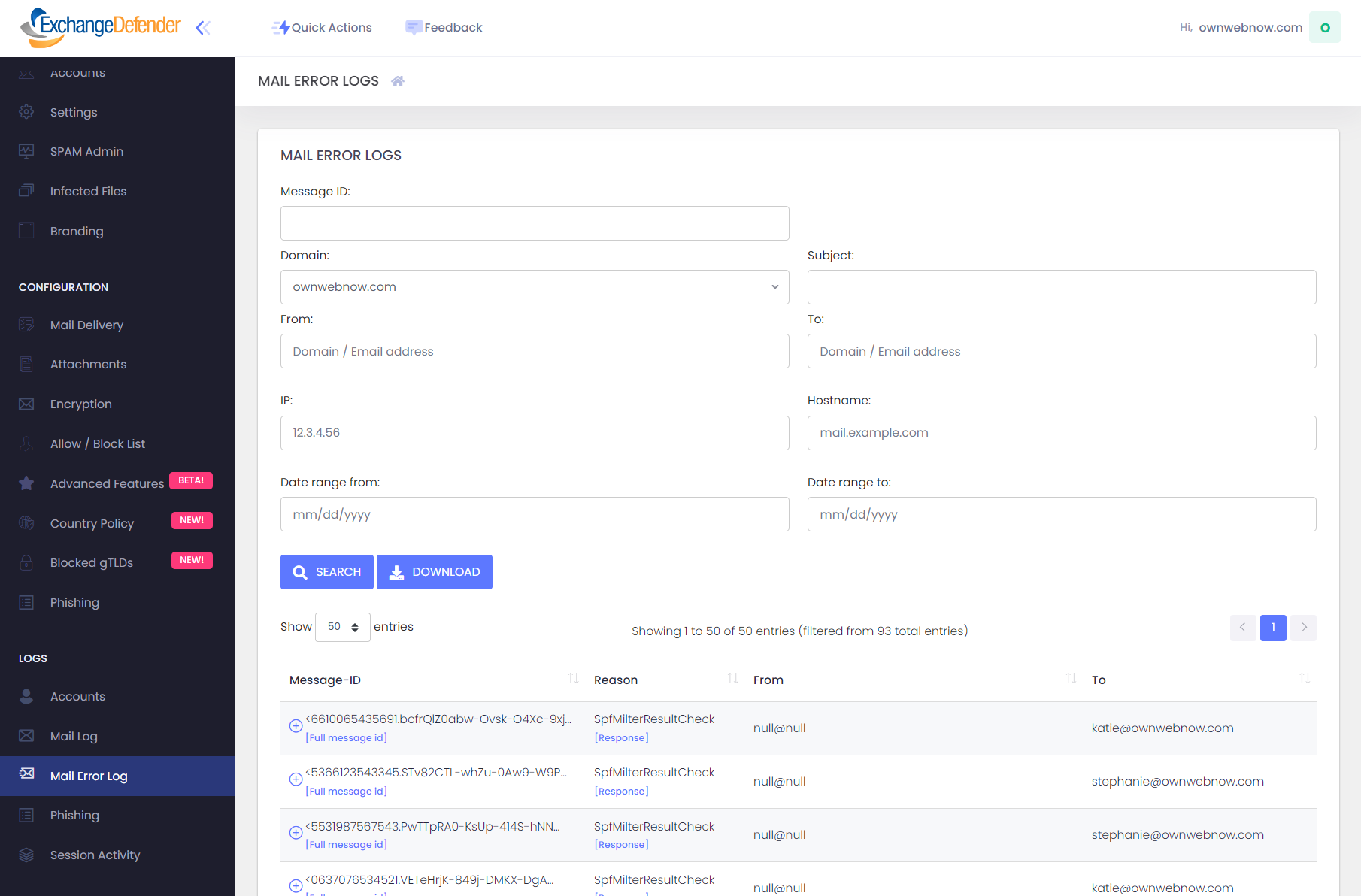
Mail Error Log
ExchangeDefender enables Domain Administrators and Service Providers to access low-level SMTP error logs. While email transaction logs ("Mail Logs", "SPAM Logs") provide all the details about message processing and delivery, Mail Fail (Error) logs provide errors ExchangeDefender issues to messages that are not accepted by our network.
ExchangeDefender usually rejects messages due to administrator policy configuration (your settings/routing), domain and geoIP settings, as well as protocol failures ranging from network issues to DNS authorization protocols (DKIM + SPF). When ExchangeDefender issues rejections all the data we have from the sender/mail server is available in this log.
ExchangeDefender offers a powerful search facility that can help locate messages if you know the sender/recipient. This screen gives you an easy way to identify potential issues and know exactly which messages are not getting through and why (so you can adjust your policies!)
Click on Download to download the entire fail log in the .csv format. This file can be opened using your spreadsheet or imported into another tool for better processing and analytics.
Domains - Logs - Phishing
ExchangeDefender Phishing logs contain activity from ExchangeDefender Security Center (https://r.xdref.com) and give domain administrators access to URLs that were intercepted by the ExchangeDefender Phishing Firewall with either no or bad reputation.
This information is provided for security audit purposes and for tracking which sites may have lead to a security breach/compromise. Because dangerous malware distributed through phishing often results in destruction of a PC and/or network, ExchangeDefender as an external resource can help you determine which links may have been involved in distributing dangerous payload.