New look for ExchangeDefender SPAM Release & Re-directions
It’s been about a decade since our last face-lift to the end-user facing part of ExchangeDefender – suffice to say, lot’s of cool new things are possible with the web technology that wasn’t possible in the past. So, allow me to introduce you to the ExchangeDefender Security Center!
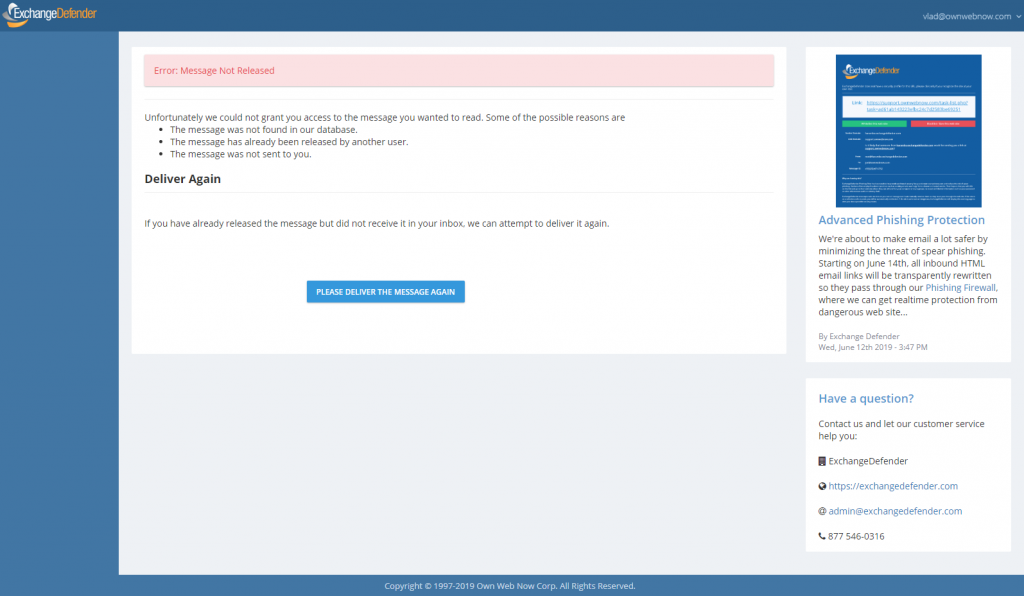
As of Thursday, June 27th, when you attempt to release a SPAM message,
you will see our new security center:
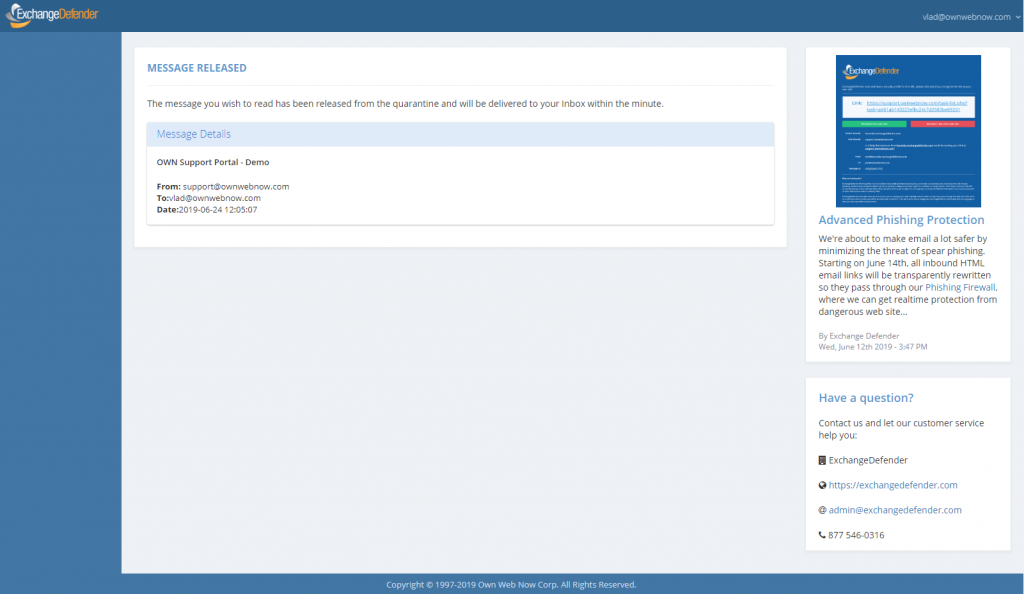
Of course, yours will look a little different. If you have ExchangeDefender from a service provider, it may have their color scheme. You can still upload your own logo (at https://admin.exchangedefender.com).
The idea here is to help connect our self-service portals https://www.exchangedefender.com/ss, our chat, our alerts, and documentation into one spot so when an issue comes up we can help the end user right then and there.
Remember that all of this stuff is data driven, so if you’re one of our partners we encourage you to put up your own announcements, deploy the XD NOC for your organization so your branding is preserved, work with our account managers, etc.
Going forward, this will be the default view for unauthenticated connections – so WFS, Encryption Download, SPAM release, and the Phishing Firewall Redirect.
P.S. How do IP restrictions play into this? They don’t. If you have ExchangeDefender enabled only for Trusted Devices and admin portal locked down to the enterprise IP range, the site will still allow the user to release SPAM from the quarantine no matter where they are (think mobile device access). For other functionality, once they click on Login the same 2FA/OTP/Known Device/IP Restrictions are in play.
ExchangeDefender Phishing Firewall Whitelist and Blacklist explained
ExchangeDefender Phishing Firewall goes online tomorrow, and we wanted to explain our policy and our implementation of the URL rewriting/redirection because it is a departure from a traditional IT hierarchy where organizational policies override group and user requirements.
Our goal with ExchangeDefender PF is to provide a level of alert and notification to our clients that is designed to provide additional information about the link they clicked on. As we scale this service out, that will be it’s purpose: Be aware of what you clicked on, and prepare for what you’re about to see. Phishing, and spear phishing in particular, is designed to be a convincing fraudulent identity theft of an organization you know and trust (your bank, your coworker, your vendors) and our goal is to help you discern if something is valid or not.
Our whitelist/blacklist implementation is in line with “we inform, you decide” mantra, as we cannot outright block you from actually going to the dangerous site. That is the responsibility of your IT department, your network management, and your organization.
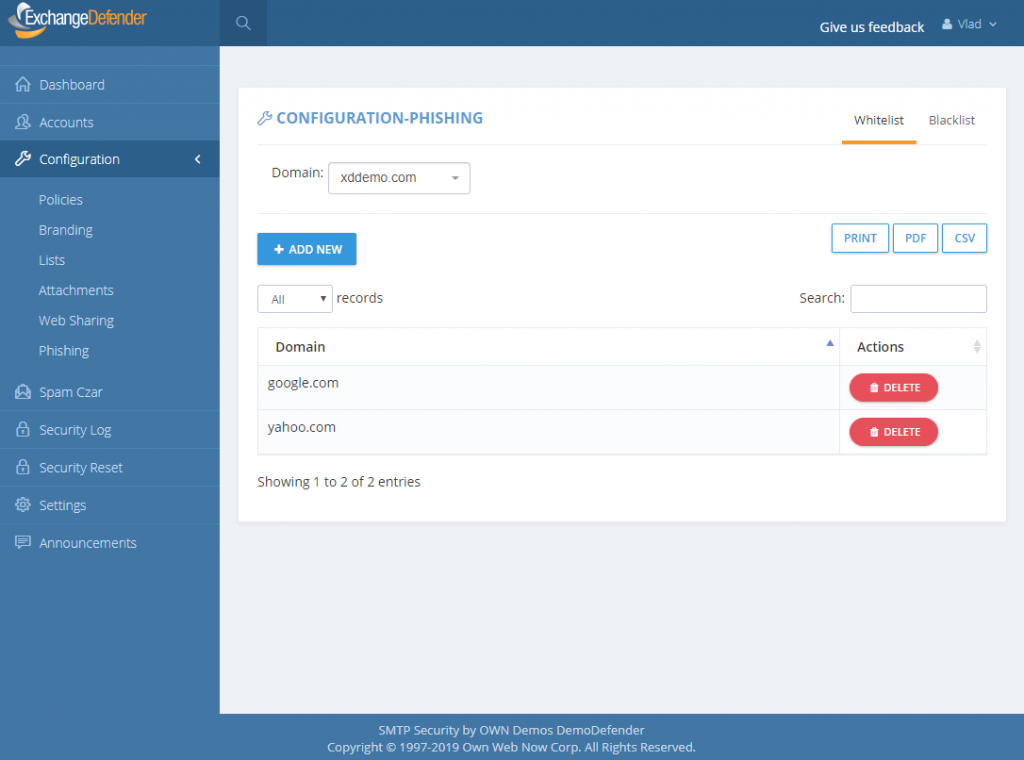
How do Whitelists and Blacklists work?
In ExchangeDefender we have 4 sets of whitelists and blacklists: user, domain/organization, service provider, and global. Our global lists are automatically populated for our service providers and when they protect a domain with ExchangeDefender, those entries are applied on the domain/organization level, and further down to the end user. As we continue to monitor, manage, and get additional intelligence about dangerous sites we will continue to curate these lists as a part of the service.
For example, we might find out that *.vlad8150.microsoft.net is a Microsoft Azure instance that is attempting to spread malware. We will promptly add it to our global blacklist and that site will now be blacklisted for every ExchangeDefender user. When they click on a link that leads them to that domain, they will see the ExchangeDefender PF notice with the URL in red. User will then have the option of ignoring it and proceeding to the site, or adding it to their whitelist. If they whitelist a domain/web site, any future requests will bypass ExchangeDefender PF web site and automatically redirect to the target URL.
The hierarchy of whitelists/blacklists is as follows, whichever rule is defined on the top is the one that is applied to the user when they click on a link.
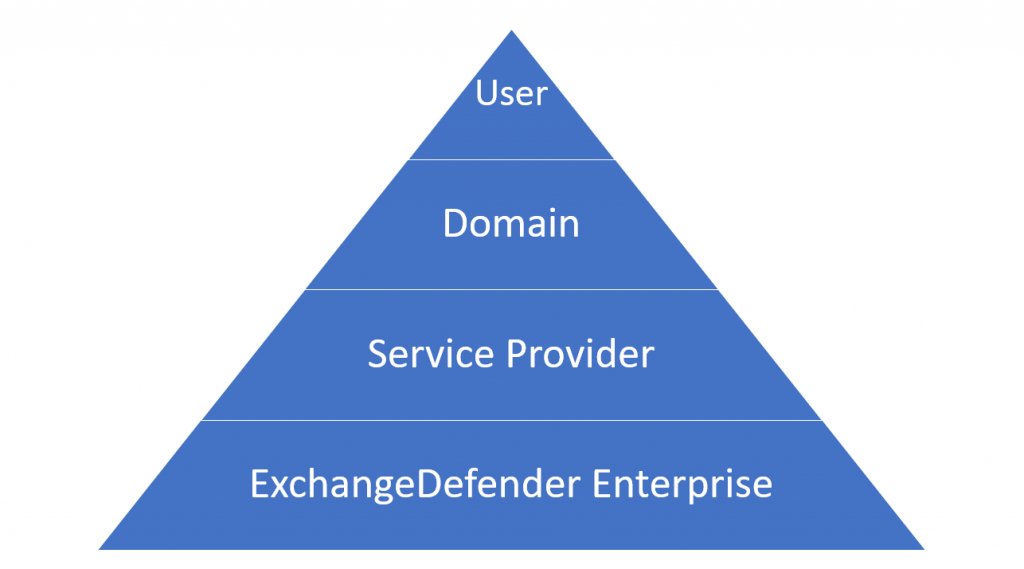
But why, why not implement policies like NTFS, access list, or any other policy in which global deny rules override end user policies?
Simply put: Traffic blocking should be done on the network level. We are simply the alert service, we will advise you when we see something dangerous and it’s up to you to discern if the site is trustworthy or not. We believe that this implementation will cause the least amount of interruption to the day-to-day use.
That said, we have been working on additional controls and policies to help our service providers and CIO’s better enforce company security policies. As with everything, security policies must be implemented in layers – and dangerous content should be enforced in accordance to business requirements. This means that if your clients should not be downloading .exe files, the network firewall should be doing that. We don’t have the means to do that as an email service – users can right click on the email, put it in notepad, remove https://r.xdref.com/url= from the link and go straight to the web site.
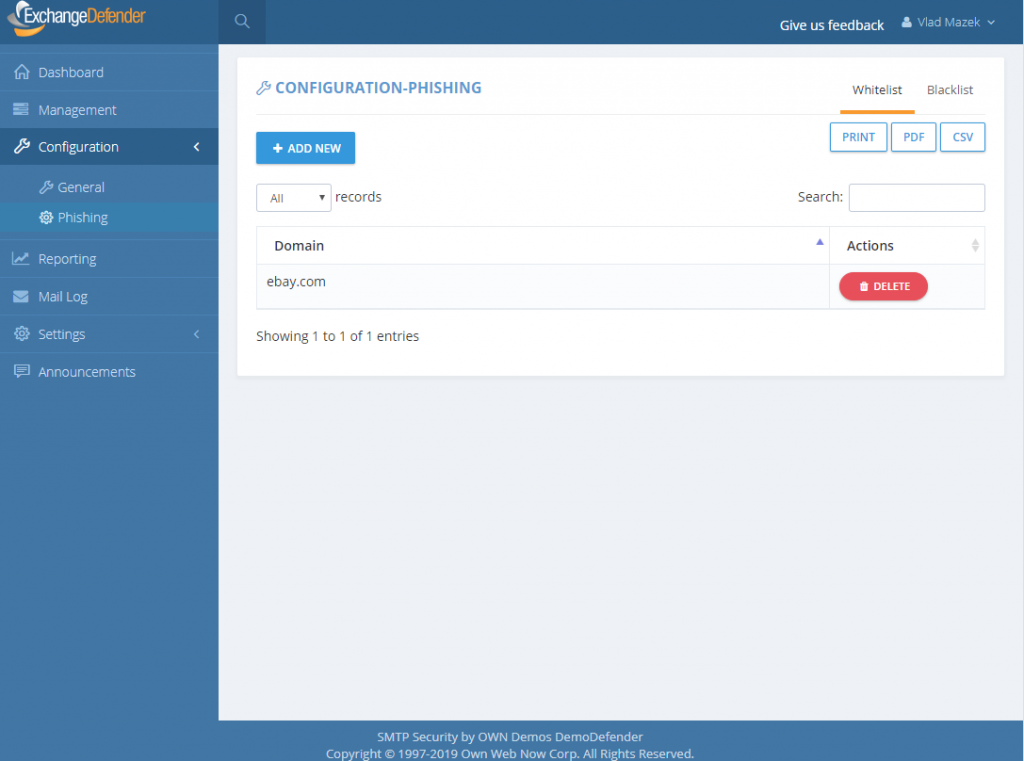
How do we manage them?
ExchangeDefender PF whitelists are available at every level of ExchangeDefender. Simply add a site to either a whitelist and blacklist and ExchangeDefender will automatically propagate your rules down through the entire organization. Users will have the ability to add / block sites from the ExchangeDefender PF in real-time and their settings will be preserved in their account only.
P.S. Officially the service goes online tomorrow, unofficially it’s been in place for months we just haven’t rewritten a single URL except for the emails you received from us – we have worked very hard on the implementation and we don’t expect major problems but will have staff on hand around the clock to address any issues immediately. Spear phishing is an epidemic, over 90% of compromises start with a link in an email. We will handle any glitches, bugs, and issues as fast as possible and have full confidence that having an alerting service with potential problems is far more useful than having nothing and leaving clients exposed.
ExchangeDefender Phishing Firewall FAQ
ExchangeDefender Phishing Firewall officially launches tomorrow, June 12th, 2019.
Every service provider and every user will be contacted with the information about the new service. Since some users may see the redirection site, we wanted to assure everyone was aware of the service, how it works, what it looks like, and what it does to protect them.
Note from Vlad: We hate changing the user experience. We understand that every time we change anything there will be an issue, folks don’t like having their cheese moved, I get it. However, this isn’t a futile exercise in self-promotion, up-selling, cross-selling, or useless noise: we are doing this to eliminate the problem that 90% of security compromises are triggered by. This implementation comes down to ethics: If I know that something is 90% likely to hurt you, and I have the means to protect you, and I choose to let you get hurt anyhow… why would you ever do business with me or ExchangeDefender? I understand we may lose some business over this, and I am willing to make less money in order to do a better job for people that trust us with their business.
Here are the answers to some questions we’ve already received:
Q: Does ExchangeDefender PF work on every device I receive email on?
A: Yes, ExchangeDefender PF automatically encodes all links sent through our system in HTML messages and redirects them through ExchangeDefender PF. This means that the link will be secured no matter which device you use to access your ExchangeDefender-protected email.
Q: Does ExchangeDefender PF protect me from non-email links?
A: ExchangeDefender only protects you from email links in HTML messages sent to your email address through ExchangeDefender. If your mail client downloads mail from 3rd party external services (Yahoo,
AOL, Microsoft, Google) that are not protected by ExchangeDefender, you will not be protected.
Q: Is ExchangeDefender PF available in ExchangeDefender Essentials?
A: ExchangeDefender PF is only available in ExchangeDefender Pro and ExchangeDefender Enterprise.
Q: Is there any way to turn off URL encoding for specific domains or users?
A: ExchangeDefender encodes the URL at the edge, as the message is being scanned for malware and other phishing forgeries.
Q: I don’t want to see the ExchangeDefender PF warning/site, can I bypass it?
A: Yes, you can simply whitelist the domain and ExchangeDefender PF will not be displayed. Whitelisted domains are automatically displayed without ExchangeDefender PF. ExchangeDefender maintains a list of known good/legitimate domains so the likelihood that you will see a dangerous (or questionable) website is very low. Additionally, your IT department or IT Solution Provider has access to organization-wide whitelist and can bypass ExchangeDefender PF to any site you need to visit.
Q: Is it possible to still get hacked/compromised even with ExchangeDefender PF?
A: ExchangeDefender PF simply applies your organizational policies to traffic and gives you additional information about the link you have clicked on. If you ignore warnings, or if you proceed to a dangerous site as a part of your organizational policy, you can still be compromised.
Q: Is there anything special I need to do on my network in order to support the redirection?
A: No, you should not have to make any modifications to your clients network in order to support this. If you do something exceptionally unusual (we would have contacted you separately, DoD requirement) and only have an allow access policy while blacklisting the rest of the Internet, redirection happens through https://r.xdref.com domain that needs to be in the safe sites.
Q: Can I turn URL rewriting off?
A: The ExchangeDefender URL rewriting code is implemented at the edge without regard for domain/user policies. In order not to introduce delays in processing, this is a global rule. If you are concerned about your clients seeing the redirection screen, whitelist the domains they typically go through. If we get complaints about it, we will look at deploying this policy further down in the scanning path which will slow down processing times for domains that opt out of the service and that feature is already in the development queue.
Q: Can I see the copy of the messages you are sending users, so I know what to expect?
A: Here is a copy of the message in PDF and Outlook format.
Q: Will the links stay live for X number of years for compliance purposes?
A: There is no expiration date for the links, as clearly stated in our Privacy Policy we do not collect or archive the links that you click on or that we encode, they will stay in your downloaded / cached / archived messages. While many regulatory requirements have message retention policy expectations, those requirements do not extend to external content, ie: you have to archive the message, you DO NOT have to archive the documents that are externally linked on third party sites. Either way, messages will continue to redirect as long as we stay in business.
Q: Can I get a list of good/bad sites for my compliance records?
A: Please contact our compliance officer at compliance@ownwebnow.com with the letter from your regulatory body and we will do our best to provide this confidential information ASAP.
ExchangeDefender Service Provider Branding
ExchangeDefender is happy to announce the enhancement of it’s Service Provider branding options. ExchangeDefender is primarily distributed and managed by other IT Solution Providers (MSPs, VARs, IT professionals) and we have exposed as much of our infrastructure as possible for white label functionality. Starting this week, we are also encouraging you to brand messages sent by ExchangeDefender:
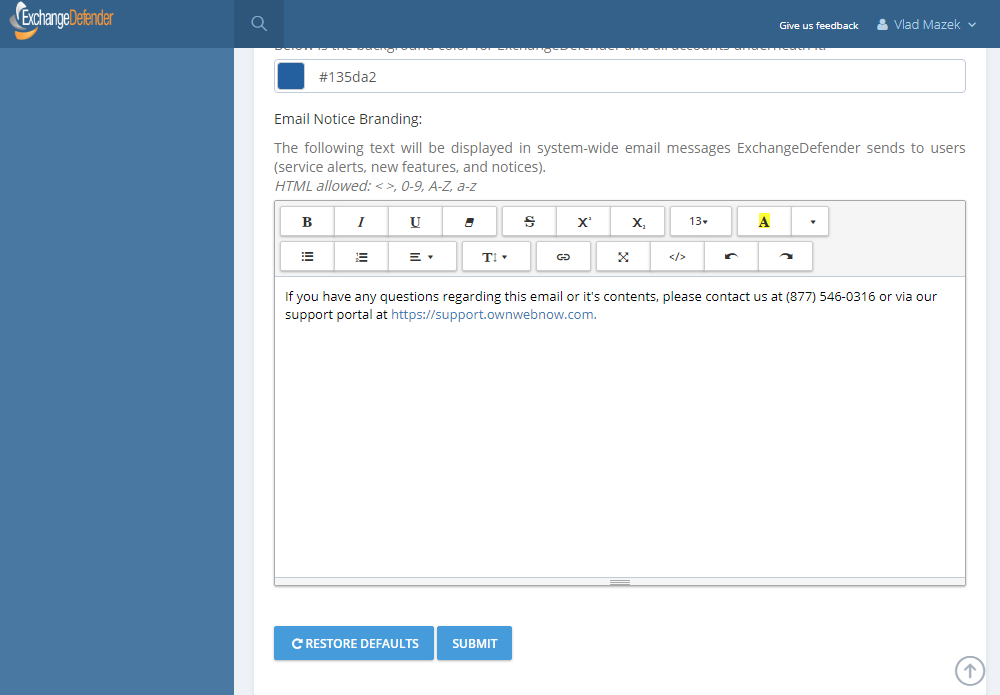
ExchangeDefender Email Notice Branding is available at https://admin.exchangedefender.com under your Service Provider login. Click on Configuration > Branding and you will see a section that will allow you to provide any content you’d like us to include on messages sent to users automatically.
We encourage all of our Service Providers to provide at least their basic contact information and a note in this section. While we are always concerned with our partners brand, system notices and urgent security issues may at times require us to contact the user directly. In the event that we do that, it’s helpful for the client to see your information at the top of the message instead of the bottom.
We’re also working hard on delivering additional features to ExchangeDefender sites, so if you have any suggestions or wishes, please let us know by hitting the feedback link anywhere in our system.
P.S. This feature was discussed in detail during our webinar on June 6th, 2019. Watch the webinar here: https://www.exchangedefender.com/media/XDNewPhishing.mp4
ExchangeDefender: Overhaul of Phishing Protection
ExchangeDefender is thrilled to announce the new Phishing Firewall in the cloud, going into full production – Wednesday, June 12th, 2019 for all ExchangeDefender Pro and Enterprise protected clients. The old way of highlighting, underlining, inserting warnings and so on will be removed from the service at the same time because it lacks the ability to protect clients in real-time.
The ExchangeDefender Phishing Firewall (EPF) is a real-time, active pishing protection. As ExchangeDefender processes inbound mail, it will rewrite every link to proxy it through EPF when user clicks on it. If the site is safe, the user will be automatically redirected to it and will not even know that EPF is in the way. If the site is not on the safe list, end users will see this warning:
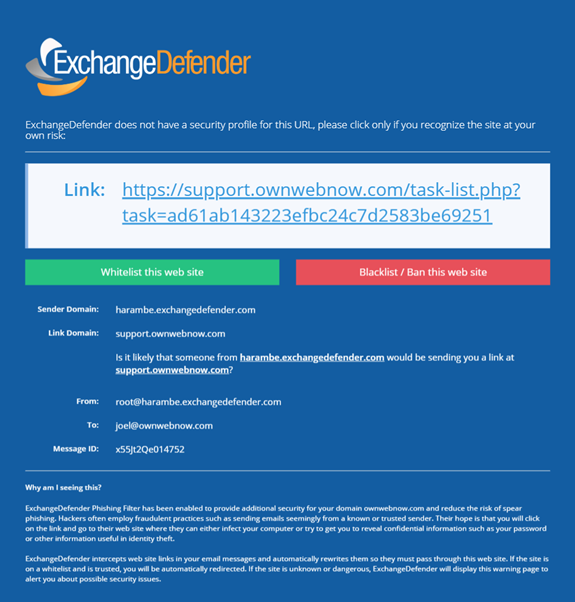
They will have the option to just click on the link and proceed, add to whitelist (at which point they are automatically allowed through in the future) or add to blacklist.
Because of the way phishing works, and all identity theft or forgery in general, it is impossible to secure email messages in transit without making annoying modifications to the message that often distort the look and feel of it. Majority of those links are in the 95% of the mail that passes through ExchangeDefender as SPAM/SureSPAM, meaning that they would never even be seen by anyone. By moving the Phishing Firewall to the cloud, we can now secure every device and provide additional metrics and advisory on top of it to protect our clients from 0-day exploits.
This feature is provided to our clients free of charge and replaces expensive “security awareness training” solutions that users typically hate and do nothing to adequately secure the client. With Exchange Phishing Firewall we enable our clients to create custom policies, maintain whitelists, blacklists, get enterprise reporting and more. It further allows us to go one step beyond – in the upcoming releases we’ll offer the ability to display a screenshot of the site as well as link intelligence data (How long ago was the domain name registered? Where is the IP you’re about to go to located? Is the domain a close spelling error of a widely recognized site? Is the forged site just a cloud hosted Google, Microsoft or Amazon cloud service instance that is holding or redirecting you to another more dangerous location?)
If you’re currently on ExchangeDefender Essentials, we encourage you to schedule a demo with our team to check this feature out as it’s significantly cheaper than antivirus or “security training” solutions and will do a far better job. If you’re on ExchangeDefender Pro or ExchangeDefender Enterprise, you will get this feature free of charge. On Monday, June 10 we will send an email notification announcing this launch to our partners, MSPs, and Service Providers. On Tuesday, June 11 we will send an email notification to end users. Finally, on Wednesday, June 12th we will go live with the service and hope to minimize the annoyance of phishing once and for all. Email is the single most popular attack vector, with 91% of the compromises starting through a phishing attack, and we look forward to protecting all our users even better.
Phishing: Beware of Strangers
This Thursday, June 6th, we will be announcing a major overhaul in the way we deal with spear phishing SPAM. No, it’s not a mind-blowing patent-pending stroke-of-genius sort of stuff, it’s much closer to what your parents told you growing up: Don’t get into a car with strangers don’t click on links or open attachments from strangers.
In a way, ExchangeDefender has had protection from this issue for years. If you had a decent IT Solution Provider implementing ExchangeDefender for you, they would have setup your SPF record and eliminated this issue – but many don’t. Or they would have turned on ExchangeDefender protection where all messages spoofing/forging your domain would automatically get junked – almost none of them do. Which is why ExchangeDefender as a service has become less of an IT tool and more of an end user suite of services to get stuff done.
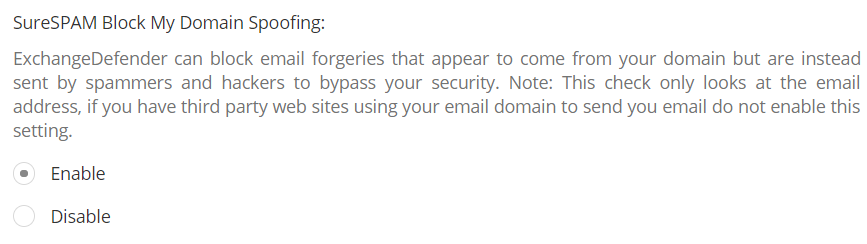
When features like this are left disabled “because they might become support issues” it becomes really difficult to secure users. But I get it, IT companies have a business to run too, which is why we’ve really stepped up our support efforts and are going to be there to help folks get things done without becoming an additional problem for the IT department. Doing so has really made us rethink how we implement features and how the service behavior needs to speak the same language as the end user. Which brings me to phishing beyond forgeries.
Can you spot a stranger?One of the new phishing protection features in ExchangeDefender will allow you to flag messages that are coming from outside of your organization. You will have two settings – to modify the subject and to modify the header of the message so when you look inside of your mailbox you’ll know what came from a stranger right away. Try it:
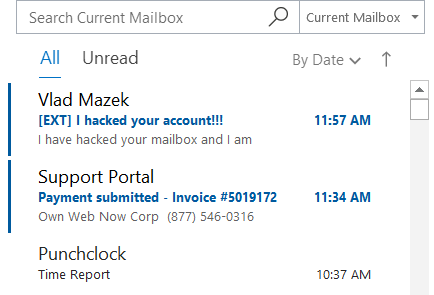
Even from the message listing you’ll know which messages shouldn’t even be opened. But suppose you ignored even that – you can set another warning, printed inside of the message, giving the user even more of an instruction of what to do.
Warning: Message was sent from outside of the organization. Do not click on links or open attachments if you don’t recognize the sender.
Far from subtle. And it has to be – because most people check email quickly, between tasks, or are simply interrupted by it. ExchangeDefender has your back, and we’ll make sure we alert you to possible issues before they become problems. Which we hope everyone will be aboard with.

Please join us, June 6th at Noon, for our NEW webinar featuring ExchangeDefender’s Phishing and Spoofing protection, plus see what’s new with Encryption, WFS, and Wrkoo!
