Email Encryption: Top 10 things clients want

Cyber attacks and the stealing of sensitive data has been big business for hackers and cybercriminals. Especially due to the disruptive covid-19 pandemic that has pushed workers to work from home. The BYOD strategy has caused major concerns for businesses, and to the Managed Service Providers who are hired to protect them. It is not all bad news though, with the introduction of an advanced email encryption software. Today, more security layers are needed to be put in place in order to protect business data and communications.
Email Encryption: A must have
Let’s first talk about the (obvious) reasons as to why SMBs need email encryption. Firstly, to have the ability to securely share sensitive information. When using email, its not as secure as you would think, and offers no real privacy. Of course, we would need encryption in order to avoid data leaks that could ruin a small business. Whether its financial records, client information, or confidential information – all are at risk of being nabbed by hackers. Email compliance is crucial, especially for businesses operating within the EU, or doing business with those that are a part of the European Union due to GDPR regulations. SMBs that are caught violating GDPR requirements when it comes to protecting user information could be subject to major fines. Businesses have to be mindful when selecting an encryption software. The right software should be able to meet all, or most of the requirements set by the organization. It’s not just about price, there are plenty of factors that SMBs will consider when choosing the right service.
Businesses have to be mindful when selecting an encryption software. The right software should be able to meet all, or most of the requirements set by the organization. It’s not just about price, there are plenty of factors that SMBs will consider when choosing the right service.
Top 10: What clients want
We have researched the top 10 features that your clients are looking for when making their decision on encryption solution.
1 – The service must be easy to setup, preferably a cloud application. Also, there should be no real training required.
2 – It must work well with all email service providers and on all devices with wifi access.
3 – The encryption software must meet all compliance requirements set forth by both U.S and EU regulations.
4 – The service must be able to offer zero-step encryption. (The ability to auto-detect sensitive information.)
5 – Granular access controls, particularly the ability to control the expiration of the message, as well as the ability to revoke any individual message to any one specific individual.
6 – Advanced Reporting – they want to know the who, when they opened it, and what they did with it.
7 – Secure web forms templates. Particularly for law firms and medical offices.
8 – Seamless recipient experience – how their clients perceive them and their sensitive data is very important.
9 – Pre-defined policy rules “filters” – available healthcare, financial, state, and education.
10 – Branding : the ability to add custom branding to the secure messages.
[Guide] ExchangeDefender Solutions in 2021

We’ve accepted more partner program applications this year than in 2020 – which is great news! Let’s be real though, 2020 was our apocalyptic year with the rush of Covid-19 sweeping the U.S like an invisible tsunami. It was normal to see our new partner requests diminish to double digits given the way business had come to a complete halt. However, we are happy to announce that our numbers are rising in 2021 – and should be returning to “normal” within the year. Side note: Our consulting services has seen a 40% increase due to the nature of remote-working with businesses needing help setting up, and securing their offices from home.
Today, we wanted to focus on the core solutions that ExchangeDefender currently offers for business in 2021. This will include any new features or upgrades that have occurred within the past year.
Let’s talk about Email.
ExchangeDefender offers Hosted Exchange, a full-service email for business that is hosted, monitored, and managed by our email experts. The enterprise-grade email features 50GB storage, advanced search, and data loss prevention. Hosted Exchange 2019 means more security and reliability for email. It is now easier than ever to provide users with the right email, to stay productive. Thousands of organizations around the world trust in ExchangeDefender daily for their business email and security needs. Why? It’s affordable, offers real-time monitoring and technical support, and meets requirements for email compliance. For Hosted Exchange pricing, please see your 2021 partner guide, or submit a ticket for update prices.
Email security is our bread and butter.
We love speaking our Advanced Email Security solution, ExchangeDefender PRO. Simply because it is the gem of all of our solutions, and is the reason why we service thousands of clients. ExchangeDefender Advanced Email Security provides a multi-layered defense against email-borne threats like SPAM, viruses, malware, spoofing, phishing and more. ExchangeDefender protects your email from viruses, trojans, malware and spyware in four major ways: first, by providing multithreaded protection using six different commercial antivirus engines. Second, by stopping identity theft by blocking phishing, third by adding authenticity to your mail messages, and fourth by eliminating worthless traffic from your inbox. Yes, it is compatible with all major email service providers – including Office 365, on-premise Exchange, and G-Suite for Business. Learn more about ExchangeDefender PRO, there are plenty of more features to explore.
Email Archiving is for long-term storage.
Our Compliance Archive solution enables organizations to keep business emails secure and compliant with tamper-proof email archiving. Compliance Archive provides secure, long-term storage, recovery and eDiscovery system that assures compliance with regulatory requirements established by IRS, FINRA, HIPAA, SOX and SEC. The solution holds up to 10 years’ worth of email for regulatory compliance, and messages are always accessible. ExchangeDefender offers unlimited storage in the cloud which reduces the need for more storage, and also drastically reduces the risk of data loss. ExchangeDefender helps organizations achieve email compliance using the latest technologies to archive, index and replicate company messages safely and securely. See more benefits of our email archiving solution.
Data Encryption, our rising star.
ExchangeDefender Corporate Encryption software lets you easily send and receive encrypted messages by email, url, or sms text message. It is easy to use, can auto-detect sensitive data, and offers real-time reporting. Our Pattern-based encryption can detect credit card numbers, social security numbers, dates of birth, and other account-specific data. It also prevents data leaks by letting organizations configure their own lexicon dictionaries with specific words and word patterns that can trigger encryption mechanisms and protect from data leakage. ExchangeDefender email encryption integrates easily with our email hosting solution, and is compatible with all major email service providers – including Office 365, on-premise Exchange, and G-Suite for Business.
File sharing plus unlimited storage, can’t beat it.
Web File Server or “WebShare” is our file sharing solution that is built for modern workplace sharing and file storage. It is perfect for businesses that are still working remotely as it offers secure sharing, and management of business and client information. Imagine a central location to securely sync, store, and share files located in the cloud and accessible (securely) from anywhere. The service features unlimited file uploads, and recipients along with unlimited storage – which is unheard of for this price. You can also control access to files and libraries by enabling user permissions. Web file sharing makes it easy for teams to share documents without having to rely on email, or old file servers. Check out all the features here.
Email outage protection. Yes, its a real thing.
Introducing Live Archive, our most coveted email continuity solution that provides organizations with email outage protection, the ability to send and receive email during a service outage. Outages bring modern offices to a halt – especially the mobile workforce. With Live Archive, resuming operations is easy; just open a browser and resume where you left off. Most importantly, you have access to all your recent email, and the system works in real time allowing you to continue sending, replying to and forwarding any new email while your infrastructure is down. Say goodbye to email outages, see all the benefits that Live Archive has to offer!
Looking to offer our solutions? Click here to see our ExchangeDefender partner program.
Which industries use our services the most?

ExchangeDefender has been providing email security, compliance, and business continuity solutions since 1998. Over 22 years in business, we currently service approximately 10,000 users via 3,000 of our active partners worldwide. Our IT expertise allows businesses to streamline workflow, and increase productivity. No matter the business, ExchangeDefender is able to provide high-powered, industry-compliant solutions.
Industries that love us.
As with all businesses, we have our favorites. These are industries that, based on a recent audit of our users, we provide a lot of service and support for. Today, we’ll outline our top 4 industries that provide us with major revenue. So, who are they?
LEGAL
When we say legal, we mean lawyers, law firms, paralegals, consulting, recruiters, courts etc. Exchangedefender provides legal IT services that empower in-house and freelance staff. Our managed IT and cloud computing services make sure that firms can represent their clients efficiently and professionally. Some of the biggest services we offer to the legal sector are scalable solutions tailored to the size of the practice. This includes enhanced security and protection from cyberthreats, along with maintaining compliance with IT regulations and industry practices. Services that are most in-demand for the legal industry are: data encryption, email security, email archiving, and email outage protection.
HEALTHCARE
The healthcare industry is certainly a major player for us. We estimate about 35% of our clients provide services within this industry. For example, we service doctors and dentists, but also laboratories, pharmacies, and rehabilitation centers. ExchangeDefender provides services mainly to small and medium sized medical practices. Solutions that are most popular for this field are: Hosted email, email security, compliance (email archiving), and data encryption. It is important to note that the medical field has strict regulations on the protection of PHI (personal health information). When landing a new medical office, be sure to mention how secure ExchangeDefender is for their email and data, and that our solutions can be tailored to their organization’s needs. (Most small-to-medium size healthcare businesses will adhere to the same types of policies and rules as ordered by law.)
FINANCIAL
Today’s financial and accounting firms are built around the customer—and the wealth of confidential data they entrust to your care. This huge responsibility requires IT systems that are accessible, fast, efficient and affordable. But, finding the right balance is difficult when security risks, industry regulations, and economic conditions are changing daily in the finance industry.
How do ExchangeDefender solutions help? We make sure that financial services, and accounting businesses are able to safeguard their data with enhanced security and protection from cyber threats. We also make sure that our clients are in compliance with federal regulations and with industry standards. The most sought-after ExchangeDefender solutions for this industry are: Email security, data encryption, web file sharing, and our email outage protection (Live Archive).
GOVERNMENT
The pressure is on to embrace innovations such as cloud computing, enable mobile access, pave the way for big data, and keep it all running smoothly and securely. However, continually shrinking budgets, security concerns, and shifting mandates make developing and maintaining IT environments more challenging than ever. ExchangeDefender delivers comprehensive technology services to strengthen and modernize state and local government IT departments and give them the professionals the tools they need to improve operations.
Government agencies’ number one priority is adhering to privacy and data protection regulations. In a close second place is cyber and web security. Our clients depend on us to protect them from cyber threats, and to protect their big data. It is very common for us (and our MSPs) to be hired to offer strategic guidance in overcoming technology challenges. If you can offer industry-compliant, high quality solutions that fit the needs of government offices – you’ll definitely acquire new clients.
Today’s Final Thoughts
No matter the industry, we’re here to keep every client safe. Every business needs email security, to secure their email and their users from email-borne and web attacks. They also need unlimited storage, to archive their all of their emails for future access and for compliance. A proper business should be using data encryption to keep confidential information secure especially in industries mentioned today. And lastly, email continuity – or email outage protection. Our Live Archive solution does exactly that, it keeps email outages at bay, ensuring that clients can send and receive email at all times. In closing, a good business should have security, productivity, and continuity solutions in place to increase their resiliency.
New Corporate Encryption users get first month free

ExchangeDefender’s Corporate Encryption solution is our rising star, and has become our best-seller for 2020. Recently, we loaded the original Encryption product with tons of new features, and relaunched it as a multichannel encryption software for small business. It is the first of its kind. Now, users can easily send and receive encrypted messages by email, url, or sms.
Service Highlights and Selling Points
Corporate Encryption features a powerful web interface for desktop and mobile, and can provide on-demand encryption using any email software out there.
One-click encryption is a major highlight with a custom addin available for both Outlook and OWA.
The software boasts powerful policies functionality with custom encryption options like automatic expiration and message destruction.
Corporate Encryption can also auto-detect sensitive information without human intervention. It recognizes patterns like account numbers, SSNs, and DOB. Plus, the service provides even more control with lexicons (keyword matching), and dictionaries.
Talk about advanced, the software also includes a Compliance Officer interface that manages violations of policies on an organizational level, increasing the COs control of sensitive data.
To see all of Corporate Encryption’s features, click here.
The Special Offer
Signup new clients to our Corporate Encryption service, and get the first month free. We’re currently running a special offer to encourage our partners to sell, as well as help boost 2021 revenues altogether. The first month is free with no charges from us, which means partners can make full profit off of the new users. If you have any questions, please do not hesitate to submit and support ticket. We would love to help you seal the deal, here are a few protips we have to offer:
Tip #1: Partners can also add a one-time onboarding fee for the added users which would increase the profit even more.
Tip #2: The (general) market price for Encryption ranges from $4 to $10 per user, per month. Selling our service would offer a generous profit per user as we are offering it for under $2.
Tip #3: Access our sales and marketing collateral for Corporate Encryption to help seal the deal. For any questions, please contact us.
Special offer expires 06/30/21
5 things every MSP website needs in 2021
In 2021, every business should have an online presence via a company website. We all use the internet as the first step to search for the products and services that we are interested in purchasing. What do you call a MSP business without a website? A technical disaster. Today, we have 5 major pro-tips that all MSPs should take into account when having their website. These casual tips will offer major benefits to you, and your prospective customer. Remember, keep it simple.
1 – Keep a secure website, and keep it updated.
We highly encourage that every MSP have their own website that showcases their business, and the services that they offer. Be sure that the website is clean in design, and straight to the point. Take note whether your site is showing as ‘secure’. Keep in mind that user experience is key in landing a new client. It’s great to have your own website, please ensure that the information is current. There is nothing worse than an interested client who contacts you with outdated material in hand.
2 – Market everything you offer on your home page.
Normally, the homepage of your website is the most visited page. It is the first place that the client lands on, and it also determines whether they visit other pages you have to offer. Focus on showcasing all the major services that you offer on your homepage. Keep it clean, and straight to the point to encourage them to explore further, or to give you call for more information. Your future client should be able to look at your homepage and know: who you are, what services you offer, and how to contact you.
3 – Display your contact information on everything!
We mean that, place your contact details on every webpage. When a client is exploring your website, and navigates to a secondary page, you want them to be able to see that there is an option to contact you readily available. What type of contact information should be displayed? Your business name, phone number, and office hours. You can also add your office address if you take clients for appointments. Adding an email address is always great, and a live chat option is even better!
4 – Add affiliate logos to your website
Hear us out on this one, the more credibility you can show your prospective clients, the better! For instance, adding an ExchangeDefender Partner Logo to your homepage displays that you are a certified vendor of our services. It also showcases that you are an expert in your field, that your business is in good standing, and is respected by other businesses. If you have other vendors that you are in partnership with, we suggest adding their logos as well. A visual display of trustworthiness will certainly help convince future clients to work with your business.
5 – Add Pricing, at least an offer a price range.
We know it may be difficult to display pricing for clients, especially because there are a range of factors that are in play. The reality is though, that a client is more likely to pursue the MSP who clearly shows their pricing, or at least provides a general estimate. Why? We naturally think something is more expensive when the price is not displayed. It’s hard to change that consumer mentality, however you can definitely improve your odds by showcasing actual numbers that the customer can relate to.
How does one accomplish this? Well, you can show your services in packages or a-la-carte, and simply put: starting at (enter $ amount) per user, per month. This quick tactic is a game-changer, because it tells the client whether they can afford your services or not, before actually making contact.
Live Archive, an email continuity solution for all

ExchangeDefender’s Live Archive is becoming the rising star in 2021 after a recent update and redesign. The productivity solution is built to provide businesses uninterrupted access to live and archive email. Live Archive is an enterprise-grade email continuity service that lets you resume work after a service interruption, or other technical malfunction. Side note: Since the pandemic, we have more companies using Live Archive than we ever have before.
The best part of all is that Live Archive is always-on, constantly archiving your sent and received mail for up to one year. No maintenance or management needed in case of an outage. The software is continuously uploading your mail whether your system is up or not.
Live Archive packs some powerful features leading the way for email productivity. Users are able to access their email via the cloud even when outages from Microsoft and Gmail occur. More highlights of the solution include: real-time archiving, one year of storage, and secure online access. Bonus: there is no install or download required to use the service.
The Benefits
The benefits of having an email continuity solution as part of an overall disaster recovery plan are huge! First, users have 24/7 access to their emails now matter where they go, and what service coverage they have. Accessing your emails on-the-go is important to keep businesses running smoothly. Office internet connection down? Working from home or local Starbucks? Server down? With Live Archive, don’t miss a beat
Second, the enjoyment of no outage productivity issues. Organizations have access to all of their recent mail, and can continue working in real time sending, replying to, and forwarding any new email while their infrastructure is down.
Third benefit for sure, is the “no training required”. How is that possible, right? LiveArchive is automatic – go to https://livearchive.exchangedefefender.com – login with your current email address and password, and there you’ll see up to one year of your sent and received messages.
Interested in getting Live Archive for your organization?
Click here for a quote.
Are you an MSP? Become a Partner.
Frequently asked questions about SMS Proxy

ExchangeDefender SMS Proxy is our latest product release for 2021. It is a simple text forwarding service that can relay messages to other mobile phones, emails, Slack, and Microsoft Teams.
TXT Forwarding from ExchangeDefender enables you to share a number – with your team, your family, your entire department – so when all these sites and services need to send you something to your phone to confirm your identity, you don’t have to think about whose phone was used to enroll to the service.
Today, we want to share with you the most common questions to date that we are asked about SMS Proxy. Hopefully, it will answer any inquiries that you may have when considering to use our SMS forwarding service.
1 – How many SMS recipients can I forward the message to?
You can forward SMS to up to five (5) different mobile phone numbers.
2 – Can I have multiple numbers in the same account?
Yes, there is no limit to how many numbers you have for the same account. There is even a Display Name label for each so you can tell which person, team, or promotion it’s assigned to.
3 – Can staff reply to the copied text message from their phone?
No. Your virtual SMS number is similar to a group chat where everyone receives the message. The difference is that SMS Proxy is a one-way communication method, and recipients are unable to reply to the message.
4 – Can my number receive “shortcode” messages?
Yes. You’ll need to contact us via the support portal to have this feature enabled. (It is still in beta)
5 – How do I create a webhook for Microsoft Teams?
To create a Webhook url for Microsoft Teams, please follow the guidelines from Microsoft documentation.
6 – How do I create a webhook for Slack?
To create a Webhook url for Slack, please follow the guidelines outlined in Slack documentation.
7 – How do I terminate the service?
You can terminate the service of any number at any time by visiting our Support Portal . After logging in, please click: Service Manager > SMS Proxy > Manage (pick a number) > Terminate number.
Interested in using SMS Proxy for your business? Request a quote. (It’s super affordable.)
Announcement: ExchangeDefender Service Checker
ExchangeDefender Service Checker enables our clients to quickly tell if there are any technical issues related to email delivery, mail flow, or their hosted Exchange mailbox.
ExchangeDefender services are increasingly managed by non-technical users and the process of escalating technical questions is unnecessary in our new self-service world. ExchangeDefender Service Checker is available to assist users pinpoint what the issue is and points users to the documentation on how to further troubleshoot or resolve it.
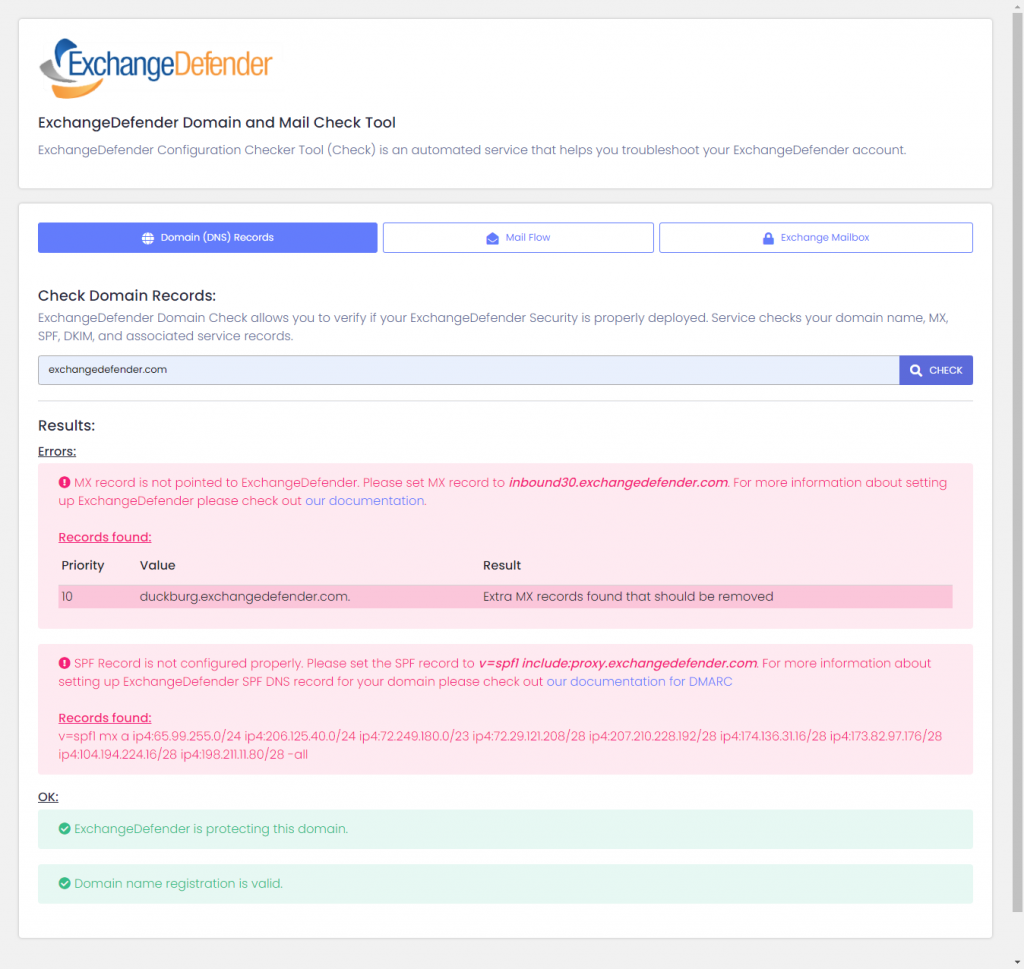
ExchangeDefender Domain (DNS) Records – We make sure your domain name is registered (clients sometimes forget to renew and only notice that their email isn’t working), that all the required DNS records for MX, SPF, and DKIM are properly configured.
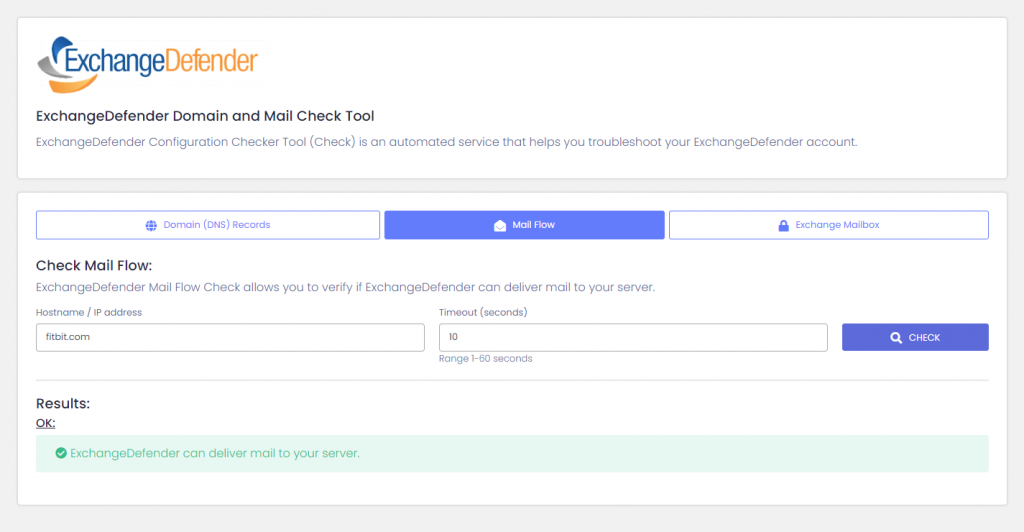
ExchangeDefender Mail Flow – Checker attempts to deliver a sample message, checking that we can connect to your mail server, get the welcome banner, and start SMTP conversation.
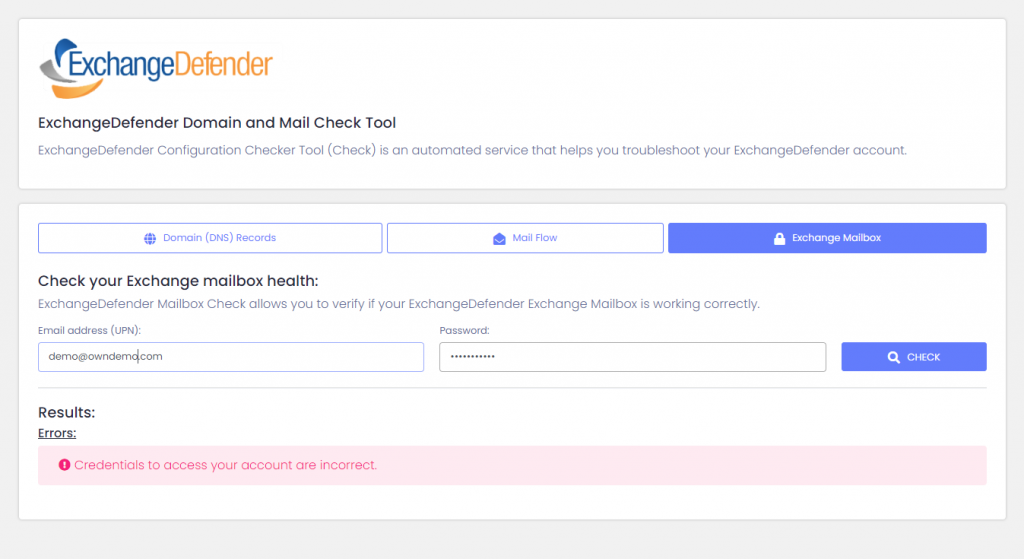
ExchangeDefender Exchange Mailbox – Checker will verify your credentials and make sure your username and password are correct. From there, a sample Outlook instance will attempt to connect to the target Exchange environment and open the mailbox.
We’re hoping that these service check tools will help our partners and clients quickly diagnose a problem with their email. Truthfully, nearly half of our support requests are answered by pointing back to the documentation. Our ExchangeDefender Checker tool will help pinpoint the problem and point the user in the right direction to help fix the issue. As always, please stay tuned to https://www.anythingdown.com that is managed by ExchangeDefender NOC and advises when there are service interruptions.
Webinar Highlights: 2021 Agenda and SMS Proxy Release

The latest webinar (4/21) with our partners featured our upcoming new features for ExchangeDefender, as well as showing a live showcase of our newest release – SMS Proxy. The buzzing one-hour presentation was well received by 100+ attendees with the Q&A session lasting more than 30 minutes.
2021: New Feature rollouts
We have an exciting timeline of new features that are currently in beta, and will be released for official use in the upcoming weeks. The new ‘solutions’ are based on client requests, and partner feedback:
Infected Attachments – ExchangeDefender now allows domain admin to retrieve infected attachments on behalf of users. Designed to allow users to have direct access to infected attachments. If users are frequently receiving files that violate the overall company policy, but retrieval is time consuming, this can help.
Charset and Alphabet Blocking – ExchangeDefender can block specific character sets which is helpful when blocking messages for clients that only communicate with locals. This is great for organizations that never want to see a foreign alphabet, helps with SPAM filtering for visual purposes and messages that violate policy end up in SPAM.
Bulk Mailer Policies– Mail policies for large mass mailer networks, can be used primarily for bulk/automated email and mail notifications. Users’ options are scan, allow and block. The “allow” policy is not/not recommended, but will simplify whitelisting.
Secure Web form– The Secure web form enables your clients to securely send you messages and documents, fully encrypted! No design maintenance or installation and works everywhere.
SMS Proxy
You’ve most likely heard about our latest release, SMS Proxy – through our blog, Facebook, or inside the portals. SMS Proxy is a virtual phone number service that connects SMS to up to 5 cell phones, email, Slack and Teams channels. Think of it as a central notification or alert service that uses mobile text messaging as the means of communication.
Why use SMS Proxy over other text messaging platforms?
1 – Compliance and policy-driven way to deliver incoming SMS messages
2 – Managed service that delivers, manages, and supports the entire message cycle
3 – Affordable. More predictable and more reliable and more secure
4 – New Security – New suite of policies for unique business solutions
You can sign up for SMS Proxy right now for free. Simply sign into the ExchangeDefender Support portal > go to Service Manager > pick a number > and tell us where to send the text messages.
[BENEFITS] Sharing files securely without using email
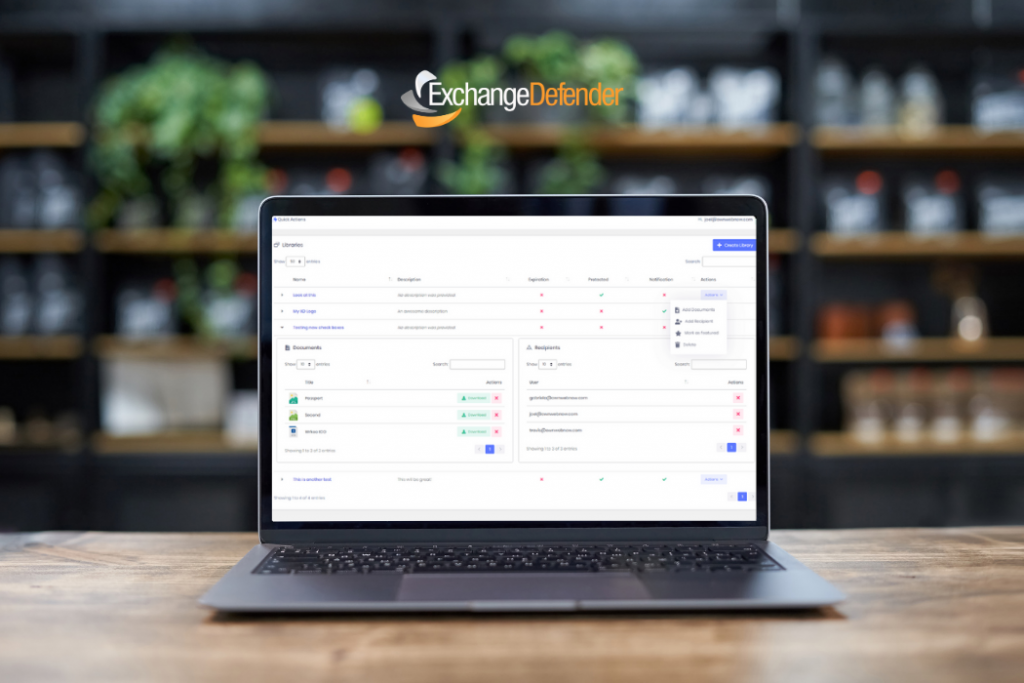
Quickly create libraries for easy document sharing and collaboration.
ExchangeDefender Web File Sharing makes it easy to quickly share a ton of large files without relying on email, clunky file servers, or cloud services primarily designed for file sync. Simply visit https://wfs.exchangedefender.com, login and create a library. Add files, add recipients, and just wait for reports.
Reviewing new documents, uploads, and comments is a breeze.
ExchangeDefender is quick, simple, and powerful! You can password protect a library, and set automatic expirations. Plus, you get email notifications when new files are added by your coworkers, or downloaded by your clients. You can even give access to your libraries. For example, you can allow recipients to delete files, or to upload files. They can make changes/revisions from their devices. We’ll even save previous versions of the file automatically so you can roll back any changes.
Built for modern workplace sharing and file storage
ExchangeDefender WFS (Web File Sharing) knows you are working on multiple projects at the same time, and makes collaborating with others a breeze. WFS makes sharing easy and secure without IT personnel. You can save your frequent recipients in groups, and as you add a new user to a group. They will have access to all the document libraries that are available to that group. The same process applies when you need to remove someone, they are instantly removed from all libraries without a lot of clicking around.
Inviting coworkers or clients
Getting someone into WFS is as simple as typing in their email address and inviting them to a library. They will receive an email invitation. If you password protected the library, they’ll get an additional email with their password. Nothing to sign up for, no enrollment process, no software to download and install. After they accept your invitation, they will be directed to wfs.exchangedefender.com to access the files you sent them.
Interested in getting Web File Server for your business? Request a quote.
Are you a Managed Service Provider? Become a Partner




