The Truth About SPF, DKIM & DMARC (Made Simple)

Let’s be honest—email security terms like SPF, DKIM, and DMARC sound like alphabet soup mixed with cybersecurity gibberish. But if you’ve ever wondered how spam gets caught, how scammers spoof emails, or why legit messages sometimes land in junk folders… this is for you.
We’re breaking down the big 3 of email authentication—in plain English—so you know exactly what’s happening behind the scenes when you hit “Send.”
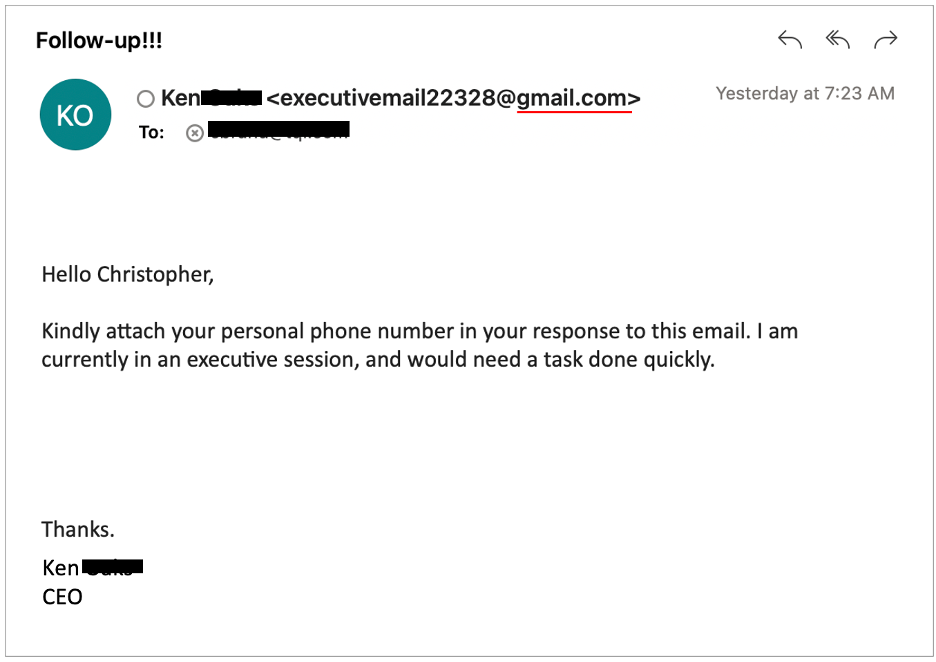
🛡️ SPF – Sender Policy Framework
What it does:
SPF tells the world which servers are allowed to send emails on your behalf.
Real-world example:
Think of SPF like a bouncer at a club. Your email server hands over a guest list (SPF record) at the door. If someone tries to get in wearing your domain name but isn’t on the list? Denied.
Why it matters:
It helps stop spammers from pretending to be you—but on its own, it’s not foolproof.
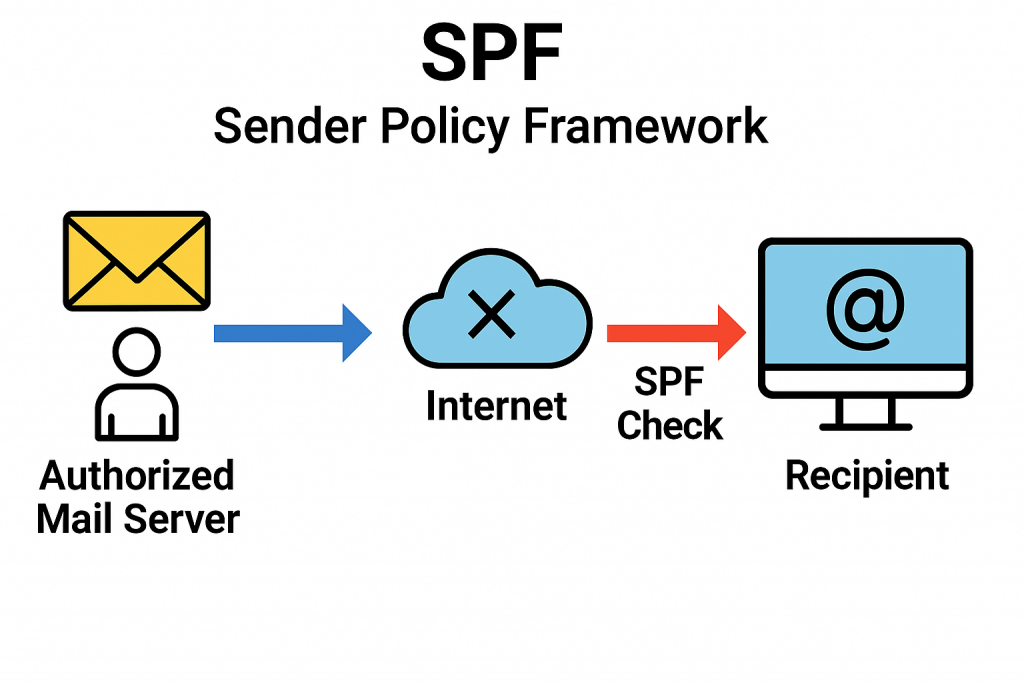
🧾 DKIM – DomainKeys Identified Mail
What it does:
DKIM adds a digital signature to your email that proves the message hasn’t been tampered with.
Real-world example:
Imagine sealing a letter with a wax stamp. If the seal’s broken, you know something’s up. DKIM is your email’s digital seal, verifying that it really came from you—and nothing changed in transit.
Why it matters:
It prevents sneaky edits to your message and proves authenticity. Combine it with SPF, and you’re already leveling up.
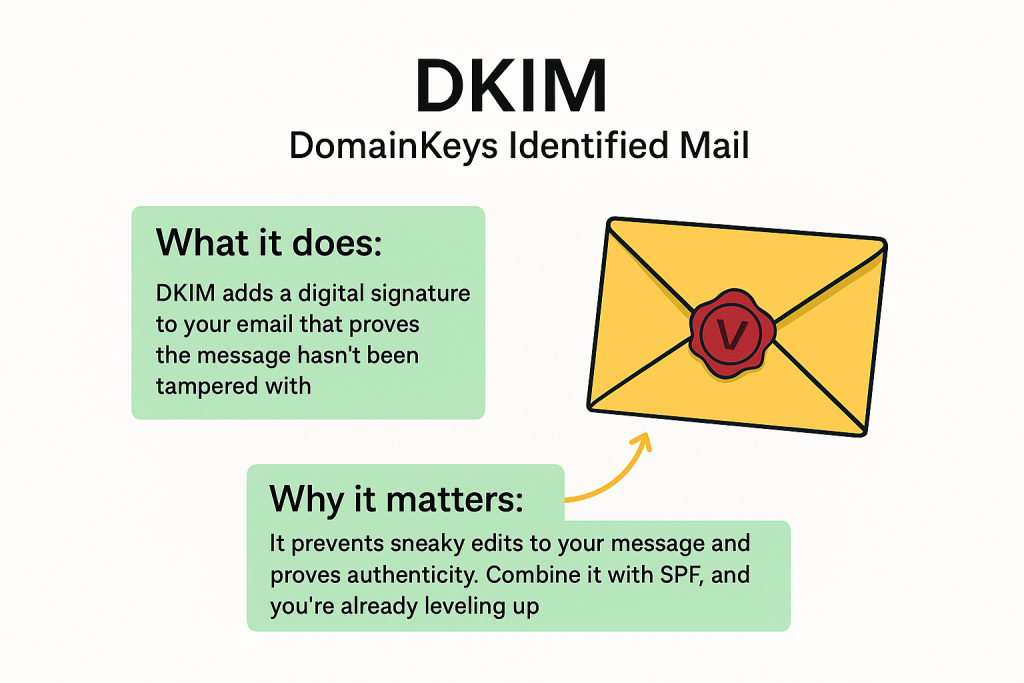
🕵️♀️ DMARC – Domain-based Message Authentication, Reporting & Conformance
What it does:
DMARC is like the manager that makes sure SPF and DKIM are actually being followed—and decides what happens when something fails.
Real-world example:
Let’s say someone shows up at your email club with a fake ID. DMARC is the one that decides: “Should we let this slide, quarantine them, or kick them out completely?”
Why it matters:
DMARC tells mail providers how to handle sketchy emails that claim to be from you. It also gives you reports so you can see who’s spoofing your domain.
🔒 Why Should You Care?
Because your email reputation = your digital trust. If you send emails from your business domain and don’t have SPF, DKIM, and DMARC properly set up, you’re basically telling the internet, “Hey, anyone can pretend to be me!”
That leads to:
- More emails going to spam
- Higher chance of getting spoofed or blacklisted
- Less trust from customers, vendors, and partners
✅ How ExchangeDefender Helps
We make email security easy, even if you don’t speak fluent geek. ExchangeDefender includes tools to:
- Set up and manage SPF, DKIM, and DMARC
- Monitor spoofing attempts
- Keep your reputation clean and your messages trusted
🧠 TL;DR
- SPF = Who can send your email
- DKIM = Prove it wasn’t tampered with
- DMARC = Enforce the rules + get reports
If you’re not using them, your email could be getting filtered—or worse, faked.
Ready to secure your domain like a pro? Let us help → www.exchangedefender.com
Why Email Backup Should Be Part of Your Disaster Recovery Plan
Because when your inbox goes dark, your business shouldn’t.
🚨 The Problem: Email Outages Happen
Imagine this: a sudden power outage, a server crash, or a cyberattack strikes. Your team can’t send or receive emails. Projects stall, client communications halt, and productivity plummets. It’s not just inconvenient—it’s a business risk.
🛡️ The Solution: Email Backup with ExchangeDefender LiveArchive
Enter ExchangeDefender LiveArchive—your safety net when email systems fail. LiveArchive ensures uninterrupted access to your emails, even during outages. Here’s how it supports your disaster recovery plan:
- 24/7 Email Access: Keep your team connected with continuous email availability.
- Seamless Integration: Works alongside your existing email infrastructure without disruption.
- Real-Time Archiving: Automatically backs up emails, ensuring no data loss.
- User-Friendly Interface: Access archived emails easily through a web portal.
📈 Why It Matters
Incorporating email backup into your disaster recovery strategy isn’t just smart—it’s essential. It minimizes downtime, protects sensitive information, and maintains client trust. With LiveArchive, your business stays resilient, no matter what.
Don’t let an email outage derail your operations. Integrate ExchangeDefender LiveArchive into your disaster recovery plan today.
Top 5 Email Threats You Didn’t Know Were Hiding in Your Inbox

Let’s face it—email is the lifeblood of modern business. But behind every “urgent” subject line or familiar sender name, there could be something much more sinister lurking. At ExchangeDefender, we spend our days defending inboxes against threats most people don’t even know exist. So today, we’re spilling the secrets. Here are 5 sneaky email threats that could be hiding in plain sight:
1. Lookalike Domains (a.k.a. Evil Twins)

These emails come from addresses that look legit—maybe a single letter off from your CEO’s real email, or a domain that’s cleverly misspelled.
Why it’s dangerous: They’re made to trick you into clicking links or wiring money.
How we stop it: ExchangeDefender uses advanced domain and sender verification to block imposters fast.
2. Zero-Day Attachments
These are brand-new threats that haven’t even made it to antivirus databases yet. They come disguised as invoices, resumes, or project files.
Why it’s dangerous: Traditional filters might miss them.
How we stop it: Real-time scanning and sandboxing help catch unknown threats before you open them.
3. Credential Harvesting Links
Not all phishing scams are loud and obvious. Some hide in the form of password reset requests or shared documents.
Why it’s dangerous: One click can expose your login—and open the door to your entire system.
How we stop it: Link analysis and real-time URL scanning keep you protected, even from shortened or masked links.
4. Conversation Hijacking
Hackers insert themselves into real email threads and respond like they’re part of your team. Creepy, right?
Why it’s dangerous: You’re more likely to trust something that feels familiar.
How we stop it: Behavioral monitoring flags unusual responses—even when they happen mid-thread.
5. Impersonation of Internal Staff
Ever get a weird request from “Accounting” or “HR”? Sometimes, attackers mimic your internal teams to request sensitive info or payments.
Why it’s dangerous: These attacks rely on trust and internal knowledge.
How we stop it: ExchangeDefender uses AI and policy enforcement to detect when internal communication doesn’t add up.
So, What Can You Do?
Well, you already did the first step: you’re here. 🧠👏
The next step? Put a solution like ExchangeDefender Email Security between your team and the bad guys. We’re built to detect, block, and neutralize all of these threats—before they hit your inbox.
Because email should be for collaboration, not chaos.
👉 Learn more about how ExchangeDefender protects your business: https://exchangedefender.com/email-security
Email Outages Are Inevitable—Downtime Doesn’t Have to Be

We all know that email is the backbone of business communication. A disruption in email services can halt operations, delay responses, and impact customer trust. Recent events, such as the Microsoft Outlook outage in March 2025, left thousands without access to their emails, highlighting the vulnerability of relying solely on a single email provider.
The Business Impact of Email Downtime
When email services go down, the consequences can be severe:
- Operational Delays: Employees unable to access emails may miss critical deadlines and meetings.
- Customer Dissatisfaction: Delayed responses can frustrate clients and damage relationships.
- Financial Losses: Interruptions can lead to missed opportunities and revenue losses.
Introducing ExchangeDefender Inbox
To combat these challenges, ExchangeDefender offers Inbox — a robust email continuity solution designed to keep your business running smoothly during email outages. Inbox provides:
- Uninterrupted Access: Continue sending and receiving emails even when your primary service is down.
- Seamless Integration: Works alongside platforms like Outlook, Gmail, and Yahoo without the need for additional installations.
- Secure Storage: Automatically archives inbound and outbound emails for up to a year, ensuring data is always retrievable.
- User-Friendly Interface: Accessible on all modern devices, allowing your team to stay connected from anywhere.
Stay Prepared with ExchangeDefender Inbox
Email outages may be inevitable, but downtime doesn’t have to be. With ExchangeDefender Inbox, ensure your business remains responsive, reliable, and resilient.
Discover more about how Inbox can safeguard your communications: ExchangeDefender Inbox
How Secure File Sharing Enhances Remote Team Collaboration
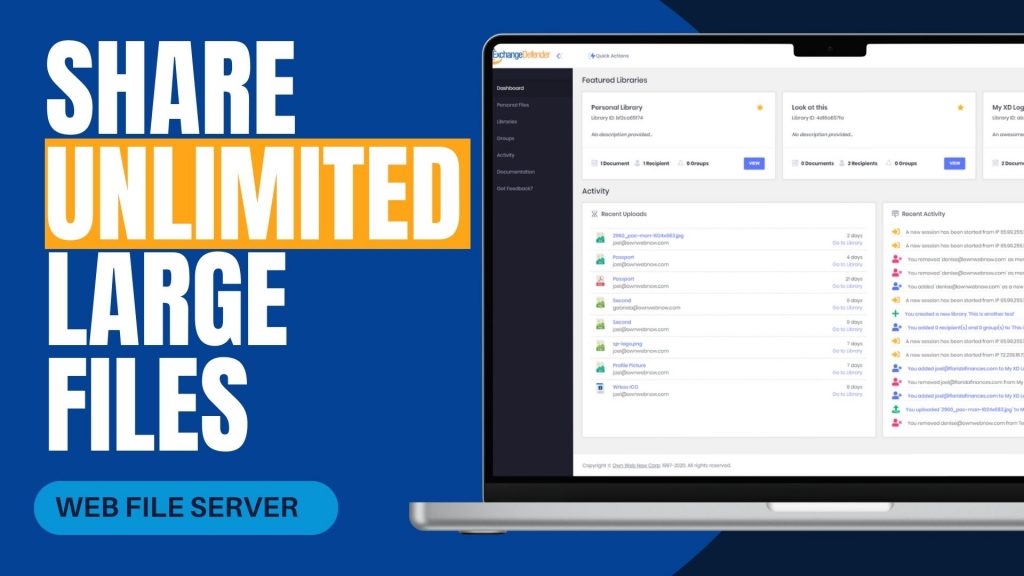
In today’s increasingly remote work environment, teams often face challenges when sharing large files securely and efficiently. Traditional methods like email attachments or outdated file servers can be cumbersome and pose security risks. ExchangeDefender’s Web File Server (WFS) offers a solution tailored to these needs, facilitating seamless and secure collaboration across different locations.
Challenges in Remote File Sharing
Remote teams frequently encounter issues such as:
- File Size Limitations: Email systems often restrict attachment sizes, making it difficult to share large documents.
- Security Concerns: Transferring sensitive information without robust security measures can lead to data breaches.
- Lack of Real-Time Collaboration: Without centralized platforms, coordinating on document edits and updates becomes challenging.
How ExchangeDefender WFS Addresses These Challenges
ExchangeDefender WFS is designed to overcome these obstacles by providing:
- Unlimited File Sharing and Storage: Users can upload and share files of any size without worrying about storage limits, ensuring that large documents like contracts or design files are easily accessible.
- Enhanced Security Features: With 128-bit SSL encryption, password protection, and auto-destruction capabilities, WFS ensures that sensitive data remains secure during transit and storage.
- User-Friendly Interface: The platform’s intuitive dashboard allows users to create document libraries, manage recipients, and track activity without requiring extensive training or IT support.
- Real-Time Collaboration: Teams can work simultaneously on documents, with features like version control and activity logs keeping everyone informed of changes.
Real-World Application
A local real estate company, Orange Avenue Homes, utilizes ExchangeDefender WFS to share contracts between remote team members and clients. The platform’s ease of use and robust security features have streamlined their document management processes, enhancing overall productivity.
For remote teams seeking a reliable and secure method to share large files, ExchangeDefender Web File Server offers a comprehensive solution. Its combination of unlimited storage, advanced security, and collaborative tools makes it an invaluable asset in today’s digital workspace.
Explore more about ExchangeDefender Web File Server and how it can benefit your remote team at ExchangeDefender Web File Server.
How to Report Phishing Emails in Outlook: A Step-by-Step Guide

Phishing emails are deceptive messages designed to trick you into revealing personal information or installing malicious software. Reporting these emails helps protect your account and assists in improving Microsoft’s security measures. Here’s how you can report phishing emails in Outlook:

For Outlook on the Web (Outlook.com):
- Sign In: Log into your Outlook.com account.
- Select the Email: In your inbox, click the checkbox next to the phishing email you wish to report.
- Report as Phishing:
- At the top of the message list, click on the “Report” button.
- From the dropdown menu, select “Phishing”.
- Confirmation: The email will be moved to your Junk Email folder, and Microsoft will be notified to enhance their spam filters.
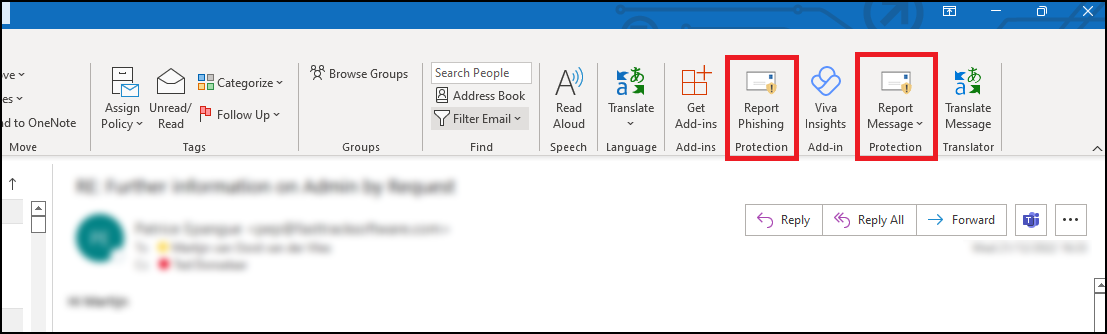
For Outlook Desktop Application (Windows):
- Open Outlook: Launch the Outlook application on your computer.
- Select the Email: In your inbox, click to highlight the phishing email.
- Access the Report Feature:
- Navigate to the “Home” tab in the ribbon at the top.
- Click on the “Report” button. If you don’t see this option, you may need to add the “Report Phishing” add-in:
- Click “Get Add-ins” in the ribbon.
- Search for “Report Phishing” and click “Add.”
- Report as Phishing:
- After adding the add-in, select the phishing email again.
- Click “Report” in the ribbon, then choose “Phishing.”
- Confirmation: The email will be moved to your Junk Email folder, and Microsoft will receive a report to improve their spam filters.
For Outlook Mobile App (iOS and Android):
- Open the App: Launch the Outlook app on your mobile device.
- Select the Email: Tap on the phishing email to open it.
- Access More Options:
- Tap the three-dot menu (⋮) at the top right corner of the email.Microsoft Support
- Report as Junk:
- Tap “Report Junk.”Microsoft Support
- Choose “Phishing” from the options provided.Microsoft Answers+1Gettysburg College+1
- Confirmation: The email will be moved to your Junk folder, and Microsoft will be notified to enhance their spam filters.
Source: Microsoft Support
Understanding Email Headers: How to Detect and Prevent Email Spoofing

Email Spoofing is a deceptive tactic where attackers forge email headers to make messages appear as if they originate from trusted sources. This technique is commonly used in phishing attacks to deceive recipients into revealing sensitive information or downloading malicious software. Understanding how to analyze email headers can help you identify and protect against such fraudulent activities.
What Are Email Headers?
Email headers are essential components of an email message that contain vital information about its origin, route, and authenticity. They include fields such as ‘From’, ‘To’, ‘Subject’, ‘Date’, and several others that provide a trail of the email’s journey from sender to recipient. While some of these fields are visible in your email client, many are hidden and can be viewed by accessing the email’s source or original message.
How to Access Email Headers:
- Outlook: Open the email, click on “File,” then “Properties,” and view the “Internet headers” box.
- Gmail: Open the email, click on the three vertical dots next to the reply arrow, and select “Show original.”
- Yahoo Mail: Open the email, click on the three horizontal dots, and select “View raw message.”
Delivered-To: user@example.com
Received: by 2002:a17:902:5307:0:0:0:0 with SMTP id v7csp1452976ejw;
Wed, 03 Apr 2024 12:34:56 -0700 (PDT)
X-Received: by 2002:a1c:4b09:: with SMTP id g9mr1234567wma.67.1712172896123;
Wed, 03 Apr 2024 12:34:56 -0700 (PDT)
Return-Path: sender@domain.com
Received: from mail.domain.com (mail.domain.com. [123.45.67.89])
by mx.google.com with ESMTPS id b7si1234567qke.287.2024.04.03.12.34.56
for user@example.com
(version=TLS1_3 cipher=TLS_AES_256_GCM_SHA384 bits=256/256);
Wed, 03 Apr 2024 12:34:56 -0700 (PDT)
Received-SPF: pass (google.com: domain of sender@domain.com designates 123.45.67.89 as permitted sender) client-ip=123.45.67.89;
Authentication-Results: mx.google.com;
dkim=pass header.i=@domain.com header.s=selector1 header.b=abcd1234;
spf=pass (google.com: domain of sender@domain.com designates 123.45.67.89 as permitted sender) smtp.mailfrom=sender@domain.com;
dmarc=pass (p=REJECT sp=REJECT dis=NONE) header.from=domain.com
DKIM-Signature: v=1; a=rsa-sha256; c=relaxed/relaxed;
d=domain.com; s=selector1; t=1712172896;
bh=VYgWqzXb1q83L9efk9EtqvL7W0U=;
h=Date:From:To:Subject:Message-ID;
b=abcd1234efgh5678ijkl9012mnop3456qrstuvwx…
Date: Wed, 3 Apr 2024 12:34:56 -0700
From: Sender Name sender@domain.com
To: Recipient Name user@example.com
Message-ID: CAJ1234567890abcdefg@mail.domain.com
Subject: Important Update on Your Subscription
MIME-Version: 1.0
Content-Type: text/plain; charset=”UTF-8″
Content-Transfer-Encoding: 7bit
Key Email Header Fields to Examine:
- From: Indicates the sender’s email address. However, this field can be easily forged and should not be solely relied upon to verify the sender’s identity.
- Reply-To: Specifies the email address to which replies should be sent. Discrepancies between the ‘From’ and ‘Reply-To’ addresses can be a red flag for spoofing.
- Received: Shows the servers that handled the email during its transmission. By examining the sequence of ‘Received’ fields, you can trace the path the email took and identify anomalies.
- Return-Path: Indicates where non-delivery receipts (bounces) are sent. A mismatch between the ‘Return-Path’ and ‘From’ addresses may suggest spoofing.
- Received-SPF: Displays the result of the Sender Policy Framework (SPF) check, which verifies if the email comes from an authorized server. A ‘Fail’ or ‘Softfail’ status can indicate potential spoofing.
Detecting Spoofed Emails:
- Examine the ‘Received’ Fields: Trace the email’s path by reviewing the ‘Received’ fields. Inconsistencies or unfamiliar server names can be indicators of spoofing.
- Check SPF, DKIM, and DMARC Results: These authentication mechanisms help verify the legitimacy of the email. Failures or absence of these checks can be warning signs.
- Analyze the ‘Return-Path’ and ‘Reply-To’ Fields: Ensure these fields match the ‘From’ address and are consistent with the sender’s domain.
- Use Email Header Analysis Tools: Online tools like MxToolbox’s Email Header Analyzer can simplify the process by parsing headers and highlighting issues.
By understanding and analyzing email headers, you can better detect and prevent email spoofing attempts, thereby safeguarding your personal and organizational security. Need extra security? Try ExchangeDefender PRO for free!
Are the BCBS settlement emails legit?

The recent Blue Cross Blue Shield (BCBS) settlement has led to a wave of emails notifying individuals about potential compensation. While many of these messages are legitimate, cybercriminals are using this as an opportunity to launch phishing scams. Here’s what you need to know to protect yourself.
What Is the BCBS Settlement?
BCBS agreed to a $2.67 billion settlement in an antitrust lawsuit alleging the company engaged in anti-competitive practices. Individuals or entities that had BCBS health insurance or administrative services between February 2008 and October 2020 may be eligible for compensation.
The official settlement administrator has been sending notifications via email and mail. Legitimate emails come from Notice@BCBSsettlement.com, and the official website is www.BCBSsettlement.com.
How Scammers Are Exploiting the Settlement
Cybercriminals are taking advantage of this widespread settlement by sending fraudulent emails that:
- Contain suspicious links, such as those prompting users to “request an electronic debit card”
- Use convincing BCBS logos and branding to appear legitimate
- Request personal or financial information
Users on forums like Reddit have reported phishing attempts disguised as official settlement notifications. Clicking on these fake links can lead to identity theft, malware infections, or financial fraud.
How to Protect Yourself
- Verify the Sender – Legitimate emails will come from Notice@BCBSsettlement.com.
- Avoid Clicking Links – Instead of clicking email links, visit the official website directly by typing www.BCBSsettlement.com in your browser.
- Contact the Official Source – If you’re unsure, reach out to the settlement administrator via info@BCBSsettlement.com or call (888) 681-1142.
- Use Email Security Solutions – A robust security tool like ExchangeDefender PRO can help filter out phishing emails before they reach your inbox.
Stay One Step Ahead with ExchangeDefender
With the rise of sophisticated phishing attacks, businesses need reliable email security solutions to prevent scams like these. ExchangeDefender PRO offers advanced phishing detection, real-time email filtering, and security awareness training to keep your organization safe from evolving cyber threats.
Protect your inbox today—ask us for a demo of ExchangeDefender PRO!
How the eBay Phishing Scam Works

The eBay phishing scam is a common cyberattack where scammers impersonate eBay to steal user credentials, financial details, or personal information. These scams often take the form of fake emails, text messages, or websites designed to trick users into providing sensitive information.
In eBay phishing scams, attackers send counterfeit emails or messages that appear to originate from eBay. These communications often contain urgent prompts, such as warnings about account issues or unauthorized transactions, compelling recipients to click on malicious links. These links lead to fake websites resembling eBay’s login page, where users are tricked into entering their credentials. Once obtained, cybercriminals can exploit this information for fraudulent activities, including unauthorized purchases or identity theft.

Red Flags to Watch Out For:
🚨 Generic Greetings – Legitimate eBay emails usually address you by name. Look for fake logos!
🚨 Suspicious Links – Hover over links before clicking—real eBay links should start with “ebay.com.”
🚨 Poor Grammar & Spelling – Many phishing emails have obvious errors. Look for fake phone numbers!
🚨 Requests for Personal Info – eBay never asks for passwords, payment info, or security details via email.
How to Protect Yourself:
✅ Enable Two-Factor Authentication (2FA) for extra security.
✅ Go Directly to eBay – Instead of clicking links, log in at eBay.com.
✅ Report Suspicious Emails to eBay at spoof@ebay.com.
✅ Use Strong, Unique Passwords – Avoid reusing your eBay password on other sites.
Mitigating Phishing Risks with ExchangeDefender PRO
To safeguard against such evolving threats, businesses require robust cybersecurity solutions. ExchangeDefender PRO offers comprehensive email security designed to protect organizations from advanced email-borne attacks. Key features include:
Anti-Phishing Protection: Identifies and blocks phishing attempts, preventing unauthorized access to sensitive information.
Anti-Spam and Malware Defense: Filters out spam and detects malicious attachments, reducing the risk of malware infections.
Ransomware Protection: Guards against ransomware attacks that can encrypt critical business data.
Domain Fraud Prevention: Prevents spoofing and unauthorized use of your domain, protecting your brand’s integrity.
On-Demand Encryption: Ensures sensitive communications are securely encrypted, maintaining confidentiality.
Adding ExchangeDefender PRO to your cybersecurity setup can help protect your organization from phishing scams and other email threats. It’s a smart way to stay safe online and keep your business and relationships secure.
How to Spot and Avoid Geek Squad Email Scams
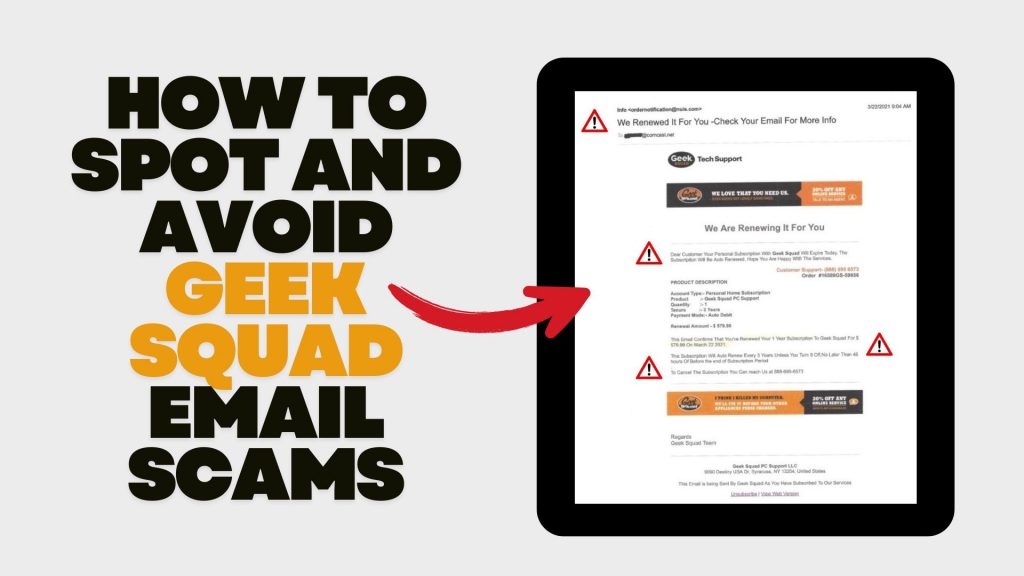
In recent years, scammers have increasingly impersonated Geek Squad, Best Buy’s tech support service, to deceive individuals into divulging personal information or making unnecessary payments. Understanding how these scams operate and how to recognize them is crucial for safeguarding your personal data and finances.
Understanding the Geek Squad Email Scam
The Geek Squad email scam is a phishing attempt where fraudsters pose as Geek Squad representatives to steal personal information or trick victims into paying for fake services. These emails often appear legitimate, making it challenging to distinguish them from authentic communications.
Common Types of Geek Squad Email Scams
- Auto-Renewal Scam: Scammers send emails stating that your Geek Squad subscription is about to auto-renew at a substantial cost. The email urges you to call a provided number or click a link to cancel the subscription, aiming to extract personal and financial details.
- Fake Antivirus Software Offer: You might receive emails warning of malware infections among Geek Squad customers, offering free antivirus software downloads. However, these downloads are malicious and designed to infect your device, steal data, or gain remote access.
- Password Reset Scam: Emails claim suspicious activity on your Best Buy account, prompting you to reset your password via a provided link. The link leads to a fake website designed to capture your login credentials, allowing scammers unauthorized access to your account.
Recognizing Scam Emails
Be vigilant for the following signs:
- Sense of Urgency: Scammers often pressure you to act quickly, creating a false sense of urgency.
- Suspicious Sender Addresses: Examine the sender’s email address for inconsistencies or misspellings. Official communications will come from a legitimate Best Buy domain.
- Generic Greetings: Emails that don’t address you by name, such as “Dear Customer,” may be fraudulent.
- Poor Grammar and Spelling: Legitimate companies maintain professional communication standards.
- Unsolicited Attachments or Links: Avoid clicking on links or downloading attachments from unknown senders.
Protective Measures
- Verify Communications: If you receive a suspicious email, contact Geek Squad or Best Buy directly using official contact information from their website.
- Avoid Unsolicited Links and Downloads: Refrain from clicking on links or downloading attachments from unknown sources.
- Use Security Software: Ensure your devices are equipped with reputable antivirus and anti-malware programs.
- Stay Informed: Educate yourself about common phishing tactics to recognize and avoid potential scams.
Reporting Scams: If you encounter a Geek Squad scam, report it to Best Buy. Additionally, file a complaint with the Federal Trade Commission (FTC) through their Complaint Assistant.