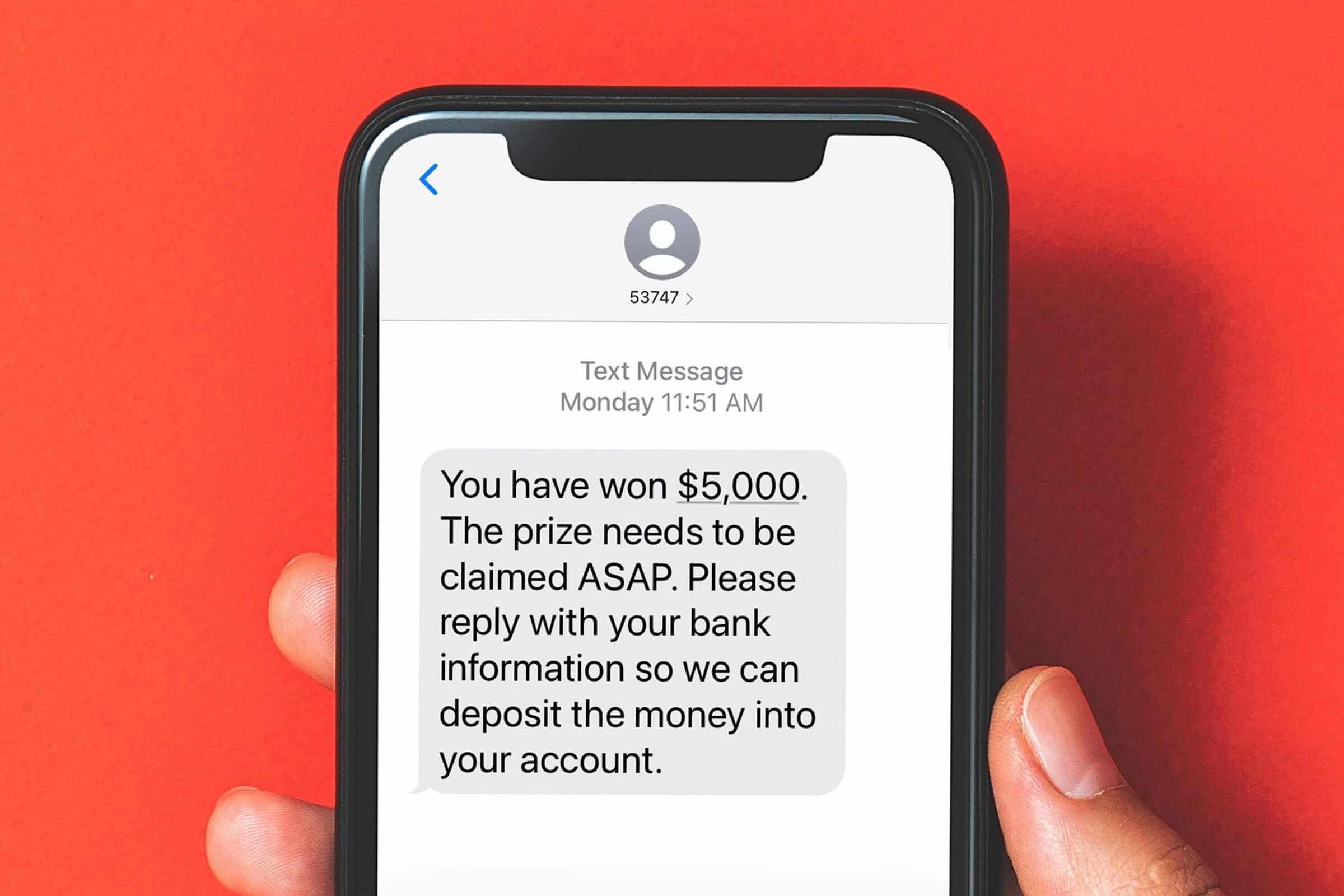
Smishing: The Text Message Scam You Need to Know!

Cybercriminals are always looking for new ways to trick people, and one of the latest and most dangerous scams is smishing. But what exactly is smishing, and how can you protect yourself? Let’s break it down in simple terms.
What Is Smishing?
Smishing (a combination of “SMS” and “phishing”) is a type of cyberattack where scammers send fake text messages to trick people into giving up personal information. These messages often pretend to be from legitimate sources like banks, delivery services, or even government agencies.
The goal? To get you to click on a malicious link, call a fake customer service number, or reveal sensitive details such as passwords, credit card numbers, or Social Security numbers.
How Does Smishing Work?
Smishing messages typically create a sense of urgency, making you feel like you must act immediately. Here are a few common examples:
- Bank Alerts: “Urgent: Your account has been compromised. Click here to verify your identity.”
- Delivery Notifications: “Your package is delayed! Click this link to confirm your details.”
- Government Scams: “You are eligible for a tax refund. Claim it now by following this link.”
Once you click on the link, you might be taken to a fake website designed to look like a real one. If you enter your information, it goes straight into the hands of cybercriminals.
How to Protect Yourself from Smishing Attacks
- Don’t Click Links in Unsolicited Messages – If you receive a text from an unknown sender with a link, be cautious. Go directly to the company’s website instead.
- Verify the Sender – If a message appears to be from your bank or another trusted organization, contact them directly using a verified phone number.
- Look for Red Flags – Watch out for poor grammar, strange URLs, and urgent language designed to pressure you into acting quickly.
- Use Security Features – Many mobile carriers offer spam message filtering. Enable these features to reduce unwanted messages.
- Report Suspicious Messages – Most mobile carriers allow you to report spam texts by forwarding them to 7726 (SPAM).
Smishing is on the rise, but you don’t have to fall victim to it. By staying informed and practicing good cybersecurity habits, you can keep your personal information safe. If you’re ever unsure about a message, always take a moment to verify before responding.
For more cybersecurity tips and updates, stay tuned to the ExchangeDefender blog!
How to Report an Amazon Phishing Email (Step-by-Step Guide)

Have you received a suspicious email claiming to be from Amazon? Phishing emails try to trick you into giving away personal information, such as your login details or payment info. It’s important to recognize and report these scams to protect yourself and others. Here’s how to do it:
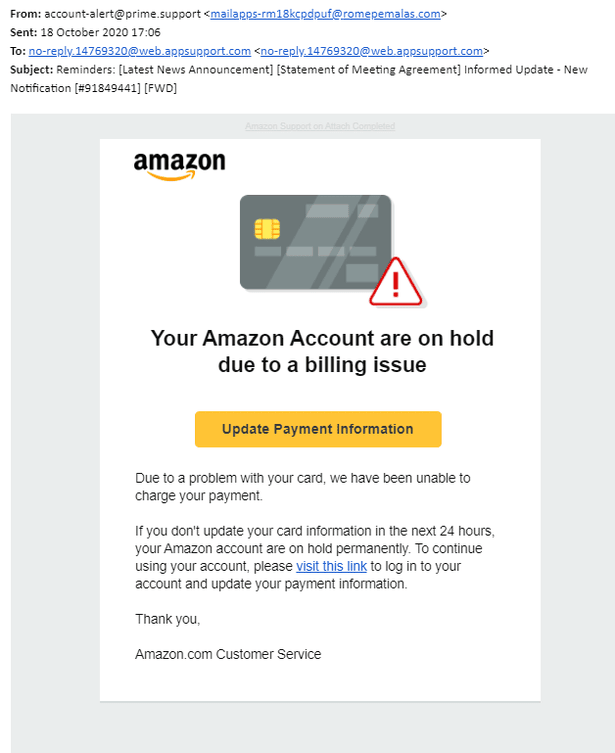
1. Identify a Phishing Email
Phishing emails often:
✅ Ask for personal or payment information.
✅ Have urgent or threatening language (e.g., “Your account will be suspended!”).
✅ Contain misspellings or strange formatting.
✅ Include fake Amazon links (hover over them to check the real URL).
2. Do NOT Click Any Links
If you suspect an email is fake:
❌ Don’t click on links or download attachments.
❌ Don’t reply or enter any personal information.
❌ Don’t call phone numbers listed in the email.
3. Report the Phishing Email to Amazon
📧 Forward the suspicious email to stop-spoofing@amazon.com.
🗑️ After forwarding, delete the email from your inbox.
4. Secure Your Amazon Account
🔑 Change your Amazon password if you accidentally clicked on anything.
🔐 Enable two-step verification for extra security.
🛑 Check your account for unauthorized purchases or changes.
By reporting phishing emails, you help protect yourself and others from online scams. Stay alert and stay safe! 🚀 Looking for phishing protection for your business? Go for ExchangeDefender, start with a 14-day free trial!
ExchangeDefender Web Services Update

ExchangeDefender Web Services Update has concluded and the new infrastructure is handling 100% of the ExchangeDefender traffic. So far the new platform is performing exactly as expected and we have already closed several minor bugs. Overall, we are extremely happy at ExchangeDefender today!
We want to take a moment to high-five ourselves and highlight three main areas where our clients and partners are going to benefit from this investment:
1. Enhanced Security
With the changes in the development backend, our platform now utilizes the latest security patches and modern language features, significantly reducing vulnerabilities and providing a more robust threat defense.
Our old platform was also rock-solid in terms of performance and security, but that secure-by-design methodology forced us to reverse-engineer as well as design and manage everything from input validation to report routing. Modern web services take care of these routine things allowing us to spend more time on policy development.
2. Improved Performance
The new infrastructure supports faster processing and is optimized for global operations allowing us to deliver a more responsive and reliable service.
You’ve already seen a hint of this in the ExchangeDefender LiveArchive relaunch as a standalone data vault for cloud operations. By breaking up our infrastructure into microservices we’re able to deliver edge operations closer to where our clients are, we can keep data more securely in your local data geography, and we can delegate away control as required.
3. Features Shipped Faster
By moving away from legacy code and internal systems/plugins for policy and protocol enforcement, we can dedicate more of our development cycles to policies and training that will keep your organization more secure. You will be able to benefit from the latest improvements and security innovations while we deliver more.
Thank you for filling out our survey, if you haven’t done so please take a moment to tell us where we can help. We have intentionally dedicated a large window to bringing the new web service infrastructure online so we do have spare cycles to help alleviate some pain points our clients are experiencing. Please take a moment to fill out our survey
We are hard at work on the new User Interface, we’re nearly ready for the public launch of our Phishing platform, all sorts of goodies are heading your way so once again – thank you for your business and your faith in us to deliver safe and secure email to your organization.
Sincerely, Vlad Mazek CEO ExchangeDefender
What All Phishing Scams Have in Common

Phishing. We hear about it constantly, but with new variations popping up all the time, it can be hard to keep track. While the delivery methods and specific lures might change, there’s a common thread that runs through every single phishing scam. Understanding these core elements is key to protecting yourself and your information.
At ExchangeDefender, we’re dedicated to helping you stay safe online. So, let’s break down the common characteristics that define all phishing attempts.
1. The Art of Deception: Impersonating Trust
The foundation of any phishing scam is deception. Scammers meticulously craft their messages to appear as if they’re coming from a trusted source. This could be:
- Big-name companies: Think PayPal, Amazon, Microsoft, or major banks. Scammers often use logos, branding, and even copy website layouts to create a convincing facade.
- Government agencies: The IRS, Social Security Administration, and other government bodies are frequently impersonated to instill a sense of authority and urgency.
- People you know: Scammers might spoof email addresses or social media profiles to impersonate colleagues, friends, family members, or even your boss.
The goal is to trick you into believing the message is legitimate, lowering your guard and making you more susceptible to their tactics.
2. The Pressure: Creating Urgency and Alarm
Once they’ve established a false sense of trust, scammers introduce a sense of urgency or alarm. This is designed to pressure you into acting quickly without thinking critically. Common tactics include:
- Account alerts: Claiming your account has been compromised, suspended, or limited.
- Security breaches: Warning of a data breach or security incident that requires immediate action.
- Missed payments or deadlines: Threatening late fees, service interruption, or legal action.
- Limited-time offers or prizes: Luring you with the promise of a reward if you act fast.
Scammers hope to bypass your rational thinking and trigger an emotional response by creating a sense of urgency, leading you to make a hasty decision.
3. The Hook: Requesting Information or Action
The final piece of the phishing puzzle is the hook – the specific action the scammer wants you to take. This usually involves:
- Clicking a malicious link: These links lead to fake websites designed to steal your login credentials, financial information, or install malware on your device.
- Opening an infected attachment: Attachments can contain viruses, ransomware, or other malicious software.
- Providing personal information directly: Scammers might ask you to reply to the email with your username, password, Social Security number, or other sensitive data.
The hook is the culmination of the scam, the point where the scammer attempts to extract valuable information or gain unauthorized access to your systems.
Staying Safe: The ExchangeDefender Approach
At ExchangeDefender, we believe that education is the first line of defense against phishing attacks. By understanding these three core elements – deception, urgency, and the hook – you can significantly reduce your risk of falling victim.
Here are a few key takeaways:
- Be skeptical of any unexpected communication, especially those requesting personal information or urging immediate action.
- Always verify the sender’s identity through a separate communication channel.
- Never click links in suspicious emails. Instead, type the website address directly into your browser.
- Enable multi-factor authentication whenever possible for an extra layer of security.
By staying vigilant and informed, you can avoid getting hooked by phishing scams and protect your valuable information. #cybersecurity #phishing #scams #onlinesafety #exchangedefender
Is That PayPal Email Real? How to Spot a Phishing Scam

PayPal is a convenient way to send and receive money online, but it’s also a popular target for scammers. PayPal phishing scams aim to trick you into handing over your login details or other sensitive information, potentially leading to financial loss and identity theft. At ExchangeDefender, we’re committed to helping you stay safe online, so let’s break down how these scams work and, more importantly, how to avoid them.
How PayPal Phishing Works
Imagine receiving an email that looks exactly like it’s from PayPal. It uses the familiar logo, branding, and even sounds official. The message might say there’s been unauthorized activity on your account, that your account has been limited, or that you need to update your information. It creates a sense of urgency, urging you to act quickly.
This is the core of a phishing scam. The email contains a link that leads to a fake website designed to mimic the real PayPal login page. If you enter your username and password on this fake site, the scammers instantly capture your information and can use it to access your real PayPal account.

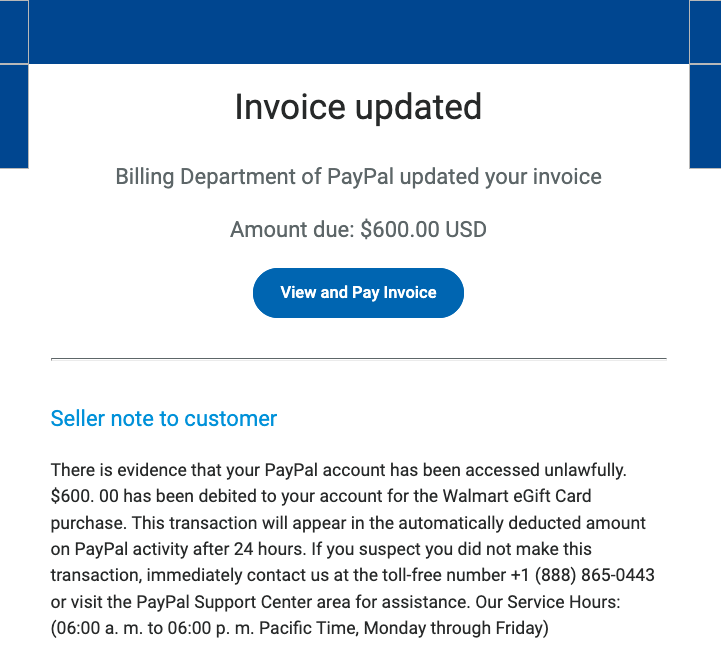
Common Red Flags to Watch Out For:
- Unexpected Emails or Messages: Be suspicious of any unsolicited communication claiming to be from PayPal. Legitimate companies rarely ask for sensitive information via email or text.
- Urgent or Threatening Language: Scammers often use language that creates a sense of panic, such as “Your account will be suspended” or “Immediate action required.”
- Suspicious Links: Hover your mouse over any link without clicking to see the actual URL. Look for misspellings, unusual characters, or domains that don’t match PayPal’s official website (www.paypal.com).
- Generic Greetings: Phishing emails often use generic greetings like “Dear Customer” instead of your name.
- Requests for Personal Information: PayPal will never ask for your password, bank account details, or credit card numbers directly in an email.
Protecting Yourself: Practical Tips
Here are some simple but effective steps you can take to protect yourself from PayPal phishing scams:
- Never Click Links in Suspicious Emails: Always go directly to the PayPal website by typing www.paypal.com into your browser’s address bar. This ensures you’re on the legitimate site.
- Check the Sender’s Email Address: Carefully examine the sender’s email address. Look for any misspellings or unusual characters. Legitimate PayPal emails usually come from addresses ending in @paypal.com.
- Enable Two-Factor Authentication (2FA): 2FA adds an extra layer of security to your account by requiring a second form of verification, such as a code sent to your phone.
- Be Wary of Attachments: Avoid opening attachments from suspicious emails, as they may contain malware.
- Report Suspicious Activity: If you receive a suspicious email or message, forward it to phishing@paypal.com.
ExchangeDefender: Your Partner in Cybersecurity
At ExchangeDefender, we’re dedicated to providing comprehensive cybersecurity solutions to protect you from online threats. While we can’t prevent every phishing email from reaching your inbox, we can empower you with the knowledge and tools to identify and avoid them. By staying vigilant and following these tips, you can significantly reduce your risk of falling victim to a PayPal phishing scam.
ExchangeDefender 2025 Web Service Expansion

In less than a week, ExchangeDefender will be running on a new generation of web services. While improving security and performance, the new platform will enable us to launch a ton of new features in 2025 and we would like our clients and partners have a say.
If you have a moment, we would appreciate some feedback. Only (3) questions, should take less than ONE minute and will help us a TON!
https://www.surveymonkey.com/r/YXQ5TKZ
In 2025 we are looking forward to growing ExchangeDefender to do every aspect of email security. We want to extend our protection to phishing simulations, training, and analytics tools. We have also heard from you regarding having mobile apps to manage the user mailbox for users who are full-time mobile. We are redesigning our SPAM reports. We are improving our M365 security footprint with built-in monitoring and performance metrics.
But most of all, we are looking to help meet the problems you’re experiencing in your organization with better solutions, better documentation, and the AI integrations you’ve been demanding.
Please take a moment to fill out our survey and let us know if you’d like us to get in touch with you. We often work with partners on custom solutions and if we can make ExchangeDefender work better for you let us know in the survey or the support ticket and we’ll be happy to set a time.
Looking forward to working with you in 2025 and thank you for your business.
Facebook Security Email Scams You Need to Know

We all rely on Facebook to stay connected with friends and family, but are you aware of the sneaky scams targeting Facebook users through fake security emails? These phishing attempts can have serious consequences, so it’s crucial to know how to spot them and protect yourself.

The Scam: How It Works
Imagine receiving an email that looks like it’s from Facebook Security. It might say something alarming like:
- “Suspicious activity detected on your account!”
- “Your Facebook account will be suspended if you don’t act now!”
- “We’ve noticed unusual login attempts from an unknown location.”
These emails are designed to scare you into taking immediate action without thinking. They often include official-looking logos and urgent language to make them seem legitimate. The real danger lies in the links within these emails. Clicking them takes you to a fake Facebook login page, meticulously crafted to mimic the real thing. If you enter your username and password on this fake page, you’re handing your account directly to scammers.
What Happens Next?
Once scammers have your login credentials, they can:
- Take over your account: They can change your password, profile information, and even lock you out.
- Spread more scams: They can use your account to send spam messages and phishing emails to your friends, potentially tricking them as well.
- Steal personal information: They might access your personal messages, photos, and other sensitive data.

How to Protect Yourself: Stay Safe Online
Luckily, there are simple steps you can take to avoid falling victim to these scams:
- Be suspicious of unexpected emails: If you receive an unexpected email about your Facebook account security, be extra cautious. Facebook rarely contacts users directly via email regarding security issues unless you’ve specifically requested it.
- Check the sender’s address: Carefully examine the sender’s email address. Legitimate emails from Facebook usually come from an address ending in “@facebookmail.com”. Anything else should raise a red flag.
- Don’t click on links in emails: This is the golden rule! Instead of clicking on links in suspicious emails, go directly to the Facebook website by typing “facebook.com” into your browser. This ensures you’re on the real website.
- Enable two-factor authentication: This adds an extra layer of security. Even if a scammer gets your password, they’ll need a code from your phone or another device to access your account. You can find this option in your Facebook security settings.
- Report suspicious emails: If you receive a suspicious email, don’t just delete it. Report it to Facebook to help them combat these scams.
Stay Vigilant, Stay Safe
Facebook security email scams are a constant threat, but by staying informed and following these simple tips, you can significantly reduce your risk. Remember, vigilance is key to staying safe online. Don’t let fear or urgency cloud your judgment. Always double-check, and when in doubt, go directly to Facebook’s website. By taking these precautions, you can protect yourself and your online presence.
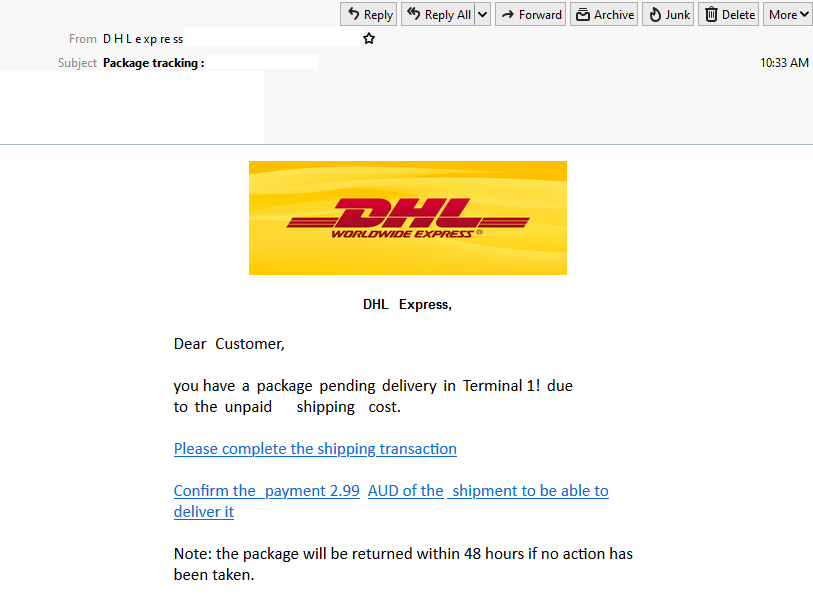
Watch Out! The USPS Text Scam is Back (and Sneakier Than Ever)

We all rely on the USPS to deliver our mail and packages, but scammers are exploiting that trust with a devious new trick: the USPS text scam, also known as “smishing.” This isn’t just another annoying robocall; it’s a carefully crafted attempt to steal your personal information and leave you vulnerable to identity theft.

How the Scam Works:
Imagine this: You receive a text message that appears to be from the United States Postal Service. It might say something like:
- “Your package delivery has been delayed due to an unpaid shipping fee. Click here to resolve.”
- “We were unable to deliver your package. Please call this number to reschedule.”
- “Your package is being held at our facility. Verify your address to avoid return to sender.”
These messages often use urgent language to create a sense of panic. They want you to act quickly without thinking. The key element is a link or a phone number. Clicking the link takes you to a fake website that looks convincingly like the real USPS site, where you’re asked to enter sensitive information. Calling the number connects you to a scammer posing as a USPS representative.

The Danger Lurking Behind the Link:
The goal of these scams is simple: to trick you into handing over your personal and financial data. This could include:
- Account usernames and passwords
- Social Security numbers
- Dates of birth
- Credit and debit card numbers
With this information, scammers can wreak havoc on your finances and your identity.
How to Protect Yourself:
The good news is, you can easily protect yourself by remembering these crucial points:
- USPS Doesn’t Initiate Contact via Text or Email (Unless You Specifically Request It): The USPS will not send you unsolicited text messages or emails. The only exception is if you’ve signed up for tracking updates using a specific tracking number.
- USPS Messages Never Contain Links: Legitimate USPS communications will never include clickable links. This is a huge red flag.
- Be Wary of Urgent Language: Scammers use urgency to pressure you. Take a moment to think before you act.
What to Do If You Receive a Suspicious Text:
- DO NOT click on any links.
- DO NOT call any numbers provided in the text.
- Delete the message immediately.
- Report the scam: You can report the message to the USPS Inspection Service (www.uspis.gov) or the Federal Trade Commission (FTC) at ReportFraud.ftc.gov.
Stay Vigilant, Stay Safe:
By staying informed and following these simple tips, you can protect yourself from the latest USPS text scam and avoid becoming a victim of identity theft. Don’t let scammers ruin your day – be smart and stay safe!
The Latest Cyber Threats You Need to Know About (2025 Edition)

The cyber threat landscape is constantly evolving, with new and sophisticated attacks emerging every day. In 2025, we’re seeing a convergence of several concerning trends:
1. AI-Powered Attacks:
- Sophisticated Phishing: AI is now generating incredibly convincing phishing emails, making them harder to detect.
- Automated Exploits: AI can quickly identify and exploit vulnerabilities in systems, launching attacks at unprecedented speeds.
- Deepfakes: AI-generated deepfakes are becoming increasingly realistic, making it difficult to distinguish between real and fabricated content, leading to social engineering and disinformation campaigns.
2. The Rise of IoT Attacks:
- With the proliferation of Internet of Things (IoT) devices in homes and businesses, attack surfaces are expanding dramatically.
- Hackers can exploit vulnerabilities in connected devices to gain access to sensitive information or even control critical infrastructure.
3. Cloud Security Challenges:
- As more businesses migrate to the cloud, the security of cloud environments becomes increasingly critical.
- Cloud misconfigurations, vulnerabilities in cloud services, and insider threats pose significant challenges.
4. Ransomware 2.0:
- Ransomware attacks are becoming more sophisticated and targeted, with attackers demanding higher ransoms and threatening to release sensitive data publicly.
To stay safe online, practice strong password hygiene, be wary of suspicious emails and links, keep your devices and software updated, and be mindful of what you share online. The cyber threat landscape is constantly evolving, but by staying informed and taking proactive steps to protect yourself, you can minimize your risk of falling victim to cyberattacks.
Why Phishing Simulations Are Essential for Your Organization
Phishing attacks remain one of the most prevalent and effective cyber threats facing businesses today. These deceptive tactics target the human element, tricking employees into divulging sensitive information or installing malware. That’s why phishing simulations are no longer a “nice-to-have” but a critical component of any robust cybersecurity strategy. At ExchangeDefender, we understand the importance of proactive security measures, and we’re here to explain why phishing simulations are essential for protecting your organization.
1. Turning Employees into a Human Firewall
Your employees are your first line of defense against cyber threats. Phishing simulations empower them to recognize and avoid phishing attacks in the real world. Here’s how:
- Real-World Scenarios: We craft simulations that mimic real-world phishing attempts, using realistic emails, text messages, and even voice calls. This exposes your team to the latest tactics used by cybercriminals, preparing them for what they might encounter.
- Learning by Doing: Experiencing a simulated attack provides invaluable hands-on experience. Employees learn to identify red flags like suspicious sender addresses, urgent requests, unusual links, and grammatical errors.
- Driving Behavioral Change: This practical training is far more effective than simply reading about phishing in a manual. It helps employees develop the instincts to spot and avoid real threats, fostering a culture of security awareness.
2. Identifying Vulnerabilities Before Attackers Do
Phishing simulations not only train your employees but also provide valuable insights into your organization’s security posture:
- Measuring Employee Susceptibility: Simulations reveal how many employees are likely to fall for a phishing attack, highlighting areas where additional training is needed. This data-driven approach allows you to focus your resources effectively.
- Pinpointing Weaknesses: By analyzing simulation results, we can identify specific types of phishing attacks that are most effective against your workforce. This enables us to tailor training programs to address your organization’s unique vulnerabilities.
- Improving Training Programs: The data gathered from simulations allows for continuous improvement of your security awareness training, making it more relevant and effective over time.

3. Reducing the Risk of Successful Attacks (and the Costs They Incur)
The ultimate goal of phishing simulations is to reduce the risk of successful phishing attacks and the devastating consequences they can bring:
- Proactive Security: Phishing simulations take a proactive approach to security, addressing the human element before it becomes a vulnerability.
- Mitigating Incident Response Costs: By preventing successful phishing attacks, you can avoid the significant financial and reputational damage associated with data breaches, ransomware infections, and other security incidents.
- Building a Stronger Security Culture: Regular simulations foster a security-conscious culture where employees are actively engaged in protecting sensitive information, making security a shared responsibility.
ExchangeDefender: Your Partner in Cybersecurity
In today’s complex threat landscape, phishing simulations are an indispensable tool for protecting your organization. At ExchangeDefender, we offer comprehensive cybersecurity solutions, including phishing simulation services, to help you strengthen your defenses and empower your employees. Contact us today to learn more about how we can help you build a more secure future.



